As of Nov 2021, CMMC 2.0 was introduced and the information below may not apply in its entirety.
The Department of Defense(DoD) has decided that self-attestation will no longer be acceptable. They want an accredited third party to certify their contractors or vendors at one of five levels of maturity for the contractor to be eligible for a contract award from the DoD. This new certification is called CMMC, the full form of which is Cybersecurity Maturity Model Certification. According to Chief Information Security Officer for Acquisition Katie Arrington, “Given the diversity of the DOD supply chain, the fact that cybersecurity is not one-size-fits-all, CMMC consists of five levels that enable the progression of cybersecurity maturity for defense contractors, as you can see by this, from basic cybersecurity hygiene to advanced.”
The motto of CMMC, according to the Accreditation body, is “Securing our Nation’s Supply Chain.” Undersecretary of Defense Ellen Lord has announced that CMMC is a critical element of DoD’s overall cybersecurity implementation.
How CMMC can help you
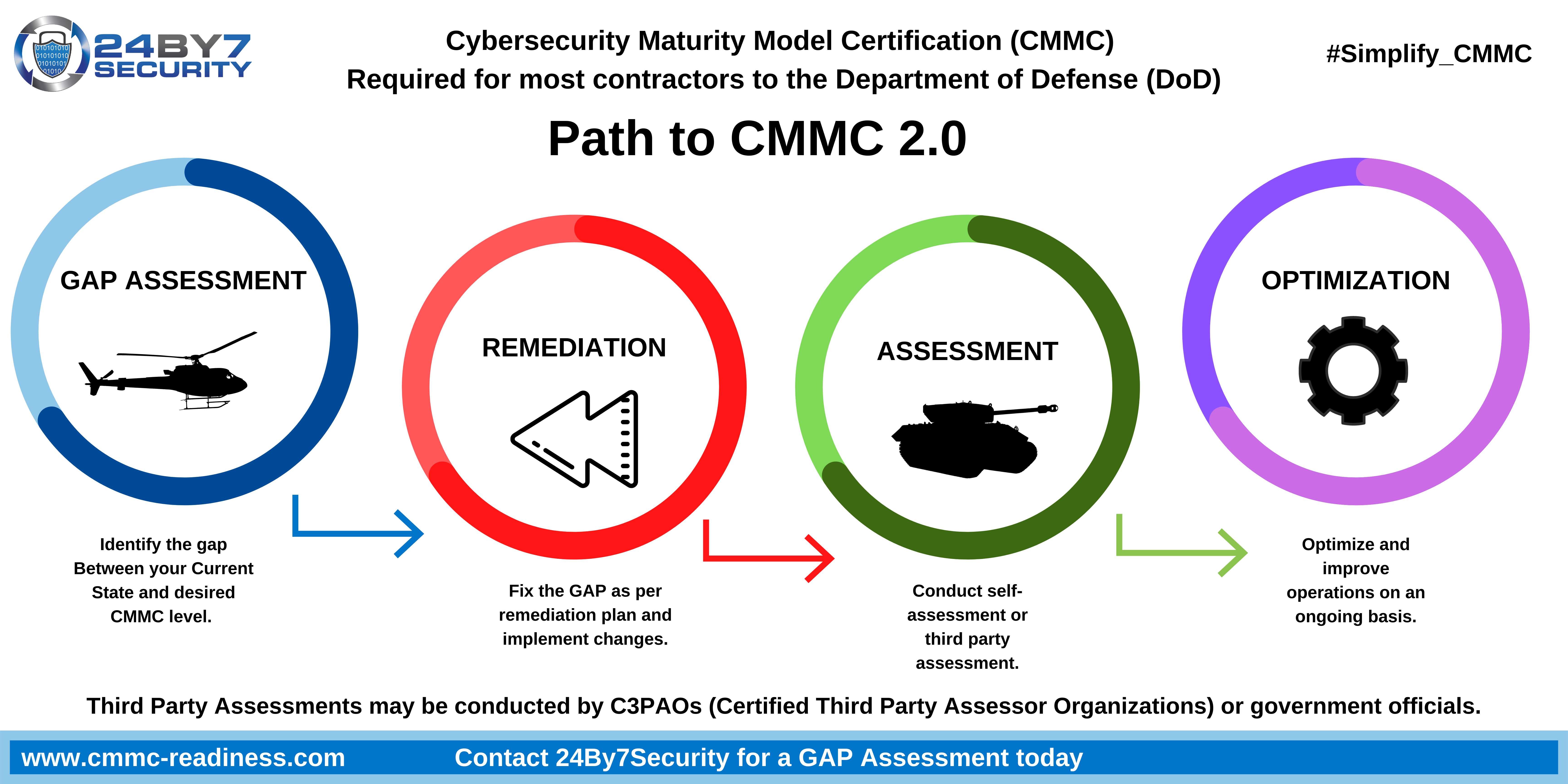
Current DoD contractors should see the CMMC as a positive step forward and should use this certification as an opportunity to take an in-depth look at their cybersecurity measures and look at ways to achieve continuous improvement. This is why our roadmap to CMMC contains optimization as the final step of the path, where organizations should continue to evolve and enhance their cybersecurity controls. Darren Deslatte, Vulnerability Operations Leader at Entrust Solutions, has said that preparing for the CMMC certification has helped his company achieve a more robust cybersecurity system. “While it can be tempting for technology companies to grow lax about their cybersecurity protocols, believing they cannot be hacked, this is far from reality. Cybercriminals are continually evolving their hacking techniques, whether they’re thinking up new social engineering techniques, leveraging AI tools to their advantage, or becoming more proficient at hacking mobile devices. That means that our technology experts have to continually evolve our cyber hygiene and defensive measures too”, adds Deslatte.
Since the DoD released the first version of the CMMC model in January 2020, some major DoD contractors got to work right away to prepare themselves for certification. While the path or the steps on the path to certification are reasonably clear, the certifying agencies have not yet been determined. The CMMC Accreditation Body has started the process of identifying and approving the assessors and practitioners who will work towards getting the Defense Industrial Base (DIB) certified. The Accreditation Body has released program details for Certified Third Party Assessor Organizations (C3PAOs), Registered Provider Organizations (RPOs), and for the credentialed roles working with these organizations. RPOs are the organizations that can help suppliers in preparing for the CMMC assessment and certification. C3PAOs are the organizations that will be accredited to conduct the assessment of the supplier and issue a certification.
24By7Security is a Registered Provider Organization (RPO), certified by the Cyber AB (formerly known as the CMMC Accreditation Body), fully qualified and trained to provide CMMC readiness services and help contractors in the Defense Industrial Base on their path to certification against the CMMC standard.
%20Combo%20Graphic%20Horizontal.png?width=273&name=RP(O)%20Combo%20Graphic%20Horizontal.png)
Timelines
- A DoD supplier or contractor should plan for at least a 6-month preparation and certification period.
- The first contract awards to certified suppliers or contractors are expected to take place in the first quarter of 2021.
- The CMMC certification is valid for a 3-year period.
10 Steps in the Path to CMMC
- Gap Assessment
- 1. Choose your desired level of certification.
- 2. Identify a Registered Provider Organization (RPO) to help with gap assessment and other steps listed below. As of late 2020, 24By7Security has been approved as a Registered Practitioner Organization (RPO) by the CMMC Accreditation Body.
- 3. Document your organization’s current state.
- 4. Document gaps between the current state and the desired maturity level.
- Remediation
- 5. Prepare a Plan of Action and Milestones (POAM) and Corrective Action Plan (CAP), prioritizing and planning to address the gaps identified.
- 6. Remediate or fix the gaps identified according to the POAM and CAP.
- Audit and Certification
- 7. Identify a Certified Third Party Assessor Organization (C3PAO) to conduct the audit. As of the date of publication of this blog, the CMMC Accreditation Body is in the process of reviewing applications from organizations seeking to be C3PAOs.
- 8. Undergo the audit that will be performed by the C3PAO.
- 9. Achieve certification after any open items are addressed to the satisfaction of the C3PAO.
- Optimization
- 10. Ongoing process to evolve and improve operations and security controls.
The process of complying with the CMMC is a time-consuming one as the anticipated amount of time end-to-end is likely to be at least six months. The effort of preparing for the CMMC can be managed better if you use the services of a Registered Provider Organization (RPO) to help you through the process. The RPO can even help you with selecting a C3PAO to conduct the final audit. 24By7Security has performed numerous gap and readiness assessments for multiple frameworks and regulations such as NIST 800-171, ISO 27001, SSAE 18/ SOC2, NIST Cybersecurity Framework. We can help you get ready for CMMC in an efficient and cost-effective manner.