2023 a record year with healthcare breaches reported every day
As part of Health and Human Services (HHS), the Office for Civil Rights (OCR) is responsible for enforcing the Health Insurance Portability and Accountability Act (HIPAA) and imposing financial penalties and corrective action plans upon HIPAA violators. In accordance with the HITECH Act, section 13402(e)(4), HHS OCR is required to publish a list of breaches of unsecured protected health information that affect 500 or more individuals, which in turn requires healthcare-covered entities to report such breaches to the OCR. Reports must be submitted within 60 days of the data breach discovery.
2023 a Record Year for Data Breaches
The great majority of healthcare data breaches have their origins in multiple violations of the HIPAA Security Rule. In 2023 healthcare data breaches reported to the OCR totaled 548 and potentially affected almost 122 million individuals by compromising their protected health information. These numbers set a recent record for healthcare data breaches.
By contrast, just the year before, in 2022, less than half that number of data breaches (249) were reported to the OCR, affecting one-fourth of that number of individuals (30.9 million).
Data breaches are reported to the OCR by hospitals and other healthcare providers, health plans/insurers, and business associates. Healthcare providers consistently report the lion’s share of data breaches, and 2023 was no exception. In 2023, 366 of the total 548 breaches (67%) were reported by healthcare providers. Business associates reported 106 (19%) and health plans 76 data breaches (14%).
High-Impact Breaches Dominate 2023
Of the 548 breaches reported to the OCR last year, 22 breaches each affected more than one million individuals. In all, more than 91 million individuals were impacted across those 22 breaches. 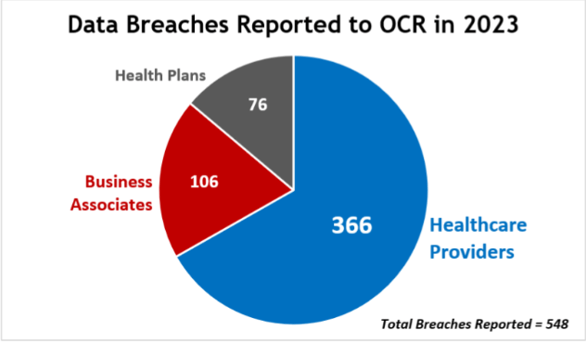
In terms of number of breaches, this is less than 5% of all reported breaches in 2023. However, in terms of impact, these 22 breaches represent 75% of all affected individuals in 2023. In other words, 5% of breaches resulted in 75% of victims.
Here are some other surprising facts:
- Although 67% of last year’s total breaches were reported by healthcare providers, of the high-impact breaches only one quarter (27%) were incurred by healthcare providers.
- More than half of the high-volume data breaches (54%) were reported by business associates—typically vendors, suppliers, and other third parties in the healthcare supply chain. Only six high-volume breaches were reported by healthcare providers, and only four by health plans.
- All but two of the 22 high-impact data breaches were attributed to hacking, with most involving network servers. Unauthorized access or disclosure was cited as the cause of the other two high-impact breaches.
Hackers appreciate the low-hanging fruit of the digital data orchard because it is so easily plucked. Their appreciation is even greater, however, for every golden opportunity that enables them to steal enormous volumes of data from a single organization in a single hack. And that’s what happened in these 22 high-impact breaches.
Following are a few stories of the high-volume 2023 data breaches. In many cases class action lawsuits are pending. In addition, chances are that when the OCR investigates it will discover multiple HIPAA violations, for which it will impose financial penalties and corrective action plans.
$60 Billion in Revenue Can’t Buy Cybersecurity
Topping the list of 22 high-volume breaches reported in 2023, the HCA Healthcare (HCA) data breach affected 11.2 million potential victims. This healthcare business associate is headquartered in Nashville and operates 182 hospitals and another 2,300 sites of care in 20 states.
In early July, HCA discovered that certain patient information had been posted on an online platform by an unauthorized party. The data included patient name, address, email, phone number, date of birth, gender, date of service, location, and date of next appointment. While the posted data breach notice assures victims that “HCA cares deeply about the patients it serves and takes this incident very seriously,” their message fell short of an apology. HCA recorded $60 billion in revenue in 2022 and stock recently traded at over $300 per share (NYSE: HCA).
Large Transcription Service Records Massive Hack
Perry Johnson and Associates, Inc. (PJ&A) ranked second among business associates in the million-plus category, reporting a breach in November 2023 that affected 8,952,212 individuals. Based in Nevada, PJ&A is the largest privately-owned provider of transcription services in the U.S., serving the healthcare, legal, and government sectors. Although the company’s website touts its HIPAA compliance and round-the-clock IT support, those assets were apparently insufficient to prevent an unauthorized party from acquiring massive volumes of personal health information from the PJ&A network between March 27 and May 2, 2023.
Managed Dental Care Hack Affects 8.8 Million
Managed Care of North America (MCNA) gets the bronze medal for a data breach affecting 8,861,076 individuals, reported in May 2023. MCNA offers dental plans for private employers, individuals, and families throughout the U.S., and was acquired in 2020 by UnitedHealth Group Inc. (NYSE: UNH). UnitedHealth Group has an aggressive acquisition history, and in 2022 posted revenues of $364 billion.
The MCNA hack occurred between February 26 and March 7, 2023, when an unauthorized third party accessed files, tampered with services, and infected computer systems with malicious code. Compromised data may have included full name, date of birth, address, telephone and email, Social Security number, driver’s license or government-issued ID number, health insurance information, and other personally identifiable information.
Blurred Lines Complicate Breach Notices
 Regal Medical Group reported a hacking incident in February 2023 affecting 3,388,856 individuals. The breach notice published by Regal demonstrates the blurred lines and maze-like interconnectivity that have become characteristic of the healthcare industry due to mergers and acquisitions.
Regal Medical Group reported a hacking incident in February 2023 affecting 3,388,856 individuals. The breach notice published by Regal demonstrates the blurred lines and maze-like interconnectivity that have become characteristic of the healthcare industry due to mergers and acquisitions.
The breach notice describes a ransomware attack that may have affected “the personal information of patients of Regal Medical Group, Lakeside Medical Organization, Affiliated Doctors of Orange County and West Covina IPA Inc., A Medical Group d/b/a/ Covina Medical Group, Heritage Provider Network, Quality Care Surgery Center d/b/a Community Surgery Center of Glendale, Sun Eun Enterprise Inc. d/b/a Pacific Family Hospice, and Valley’s Best Hospice Inc.”
Large Institutional Pharmacy Needs RX for Cybersecurity
Ranking highest among healthcare providers with a data breach that affected 5.8 million individuals, PharMerica Corporation supplies pharmacy services to more than 3,100 facilities in all 50 states through 180 local pharmacies. PharMerica learned that an unknown third party accessed its computer systems from March 12-13, 2023 and that certain personal information may have been acquired, including individual names, dates of birth, Social Security numbers, medication lists, and health insurance information. Ransomware group Money Message has claimed responsibility for the attack.
PharMerica is a Fortune 1000 company headquartered in Kentucky and is the second-largest institutional pharmacy, with revenues of $1.9 billion. Lawsuits have been filed against PharMerica and its subsidiary, Amerita Specialty Infusion Services, as a result of the breach.
Parent companies are listed as BrightSpring Health Services, Inc., Cencora, and Kohlberg Kravis Roberts, a global investment firm.
2024 on Pace to Break 2023 Record
In January of 2024, 57 data breaches affecting 500 or more individuals were reported to the OCR. If this volume is sustained, 2024 is on pace to exceed 2023 in reported data breaches. 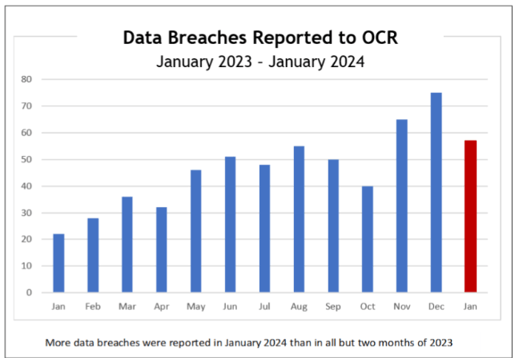
According to reports for 2023 and 2024, January 2024 has already seen more data breaches reported than all but two months of 2023.
With 2023 setting a recent record for reported breaches, 2024 could conceivably set a new record if the current volume is sustained.
Are healthcare providers, their business associates, and health plans prepared for more frequent data breaches this year? Those who are not fully HIPAA compliant could be at high risk of hacking, ransomware, and unauthorized disclosure of personal health information, as well as investigation by the OCR.
Reduce Your Risk of a Data Breach
Adopting the HITRUST Framework is an excellent way to demonstrate your commitment to robust information security and sound risk management throughout your organization. There are several other compelling reasons to use the HITRUST CSF, as outlined below:
- The HITRUST CSF incorporates the requirements of a host of regulations, providing a single source for healthcare organizations to refer to in achieving and maintaining all necessary compliance.
- In addition to enabling compliance with HIPAA, adopting the HITRUST CSF facilitates compliance with ISO standards, the NIST Security Framework, the Data Security Standard maintained by the Payment Card Industry (PCI-DSS), and the General Data Protection Regulation (GDPR) that governs business conducted in the European Union.
- Healthcare entities don’t have to go it alone. 24By7Security and other HITRUST Authorized Readiness Licensees are approved to help organizations prepare for the successful adoption of the HITRUST CSF and successful completion of the appropriate HITRUST Assessment.
Healthcare entities who adopt the Framework are in good company. Eight out of 10 top cloud service providers use the HITRUST Framework, along with 75% of Fortune 20 companies, and thousands of other organizations.
Summary
2023 was a banner year for data breaches reported to the HHS OCR by healthcare providers, business associates, and health plans. Breaches affecting 500 or more individuals must be reported to the OCR within 60 days of discovery and must include specific information. Breach reports generally lead to OCR investigations and findings of multiple HIPAA violations, which usually result in mandatory financial settlements and corrective action plans.
It is essential for healthcare organizations to be well prepared for cyberattacks, hacking, ransomware, unauthorized disclosures, and other threats to the security and privacy of the personal health information they collect and maintain. Becoming fully HIPAA compliant is fundamental to effective cybersecurity.



.png)





