Cyber Hygiene 101
You have just found out that your organization’s computers have been hacked. Was your computer the entry point for the hackers? Do you want to be known as the weakest link? Of course not. However, in today’s organizations that are highly connected, the weakest links often remain the people. Practicing basic cyber hygiene is one of the first steps to protect yourself and your organization against cyber attacks. Employees’ cyber hygiene is mandatory and done in conjunction with several other actions performed by your IT departments to keep your data secure and private.
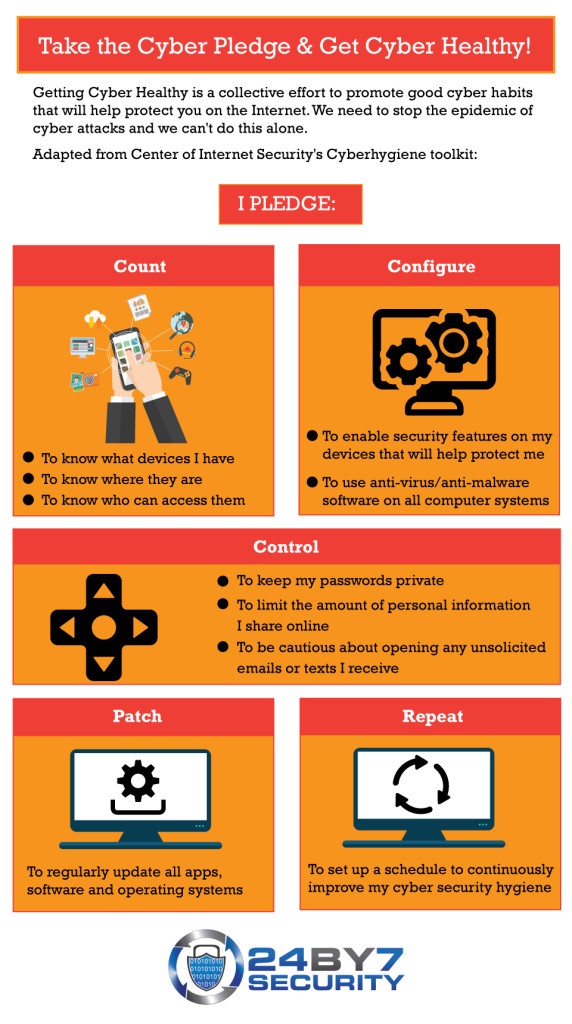
The Center of Internet Security has developed a Cyber hygiene toolkit which clearly outlines what can be done to promote good cyber habits.
Count:
- Always know what devices you have and where they are.
- Be careful of how many people can access each of your devices. Keep them password protected and limit the number of users who have rights to login to each device.
Configure:
- Install anti-virus or anti-malware software on all computer systems.
- Be sure to download all updates from anti-virus software – if not, they will not properly detect and clean viruses and malware.
- Enable security features on your devices and accounts, for example, tracking features, two-factor authentication especially on bank accounts and email, encrypt your phone if it has the feature, lock your screen, set up logon passwords. Most of these features are very easy to set up.
Control:
- Having a password is good only if it is a strong password and if it is truly private. Do not share your passwords or keep them written in plain text.
- Be careful of how much information you share online. For example, if you announce on social media that you are embarking on a 2-week vacation to Europe with your family, it is almost like handing out an invitation to steal.
- Watch out for phishing emails. They have become so sophisticated these days that it is often very difficult to distinguish between a real email and a phishing message. Check the source – i.e. where the email is coming from, do not click on any links in emails unless you are sure that they are directed to the right place.
Patch:
- Update, update, update!
- When a company brings out a software update for their product, especially one which is meant to address security vulnerabilities, do update your apps at the earliest.
Repeat:
- Repeat all steps mentioned above, to continuously improve your cyber hygiene and get cyber healthy!
Click here to watch a brief video on Cyber hygiene and to take the Cyber pledge!
To learn more about strong passwords and how to remember them, click here.
By Rema Deo.