There are a number of resources in the U.S. who collect data about cybercrime, and the FBI’s Internet Cybercrime Complaint Center is one of them. The Internet Crime Complaint Center (IC3) is an excellent source of information about trending cybercrimes and statistical data about cybercrimes perpetrated in the United States.
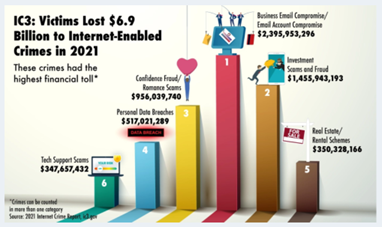
For example, cybercrimes reported to the IC3 cost victims almost $7 Billion in 2021. The costliest type of cybercrime, at almost $2.4 Billion, is known as Business Email Compromise (BEC) or Email Account Compromise. The second costliest cybercrime in 2021 was investment scams and fraud, at more than $1.4 Billion.
Many of these cybercrimes rely on phishing schemes and similar social engineering techniques to dupe individuals into inadvertently assisting the cybercriminals.
Business Email Compromises: How They Work
Business email compromises are a cybercrime that targets organizations who regularly conduct wire transfers as part of their business. First, the scammer gains access to an email account belonging to an employee—often located in the finance department—in order to learn about the vendors used by the organization. Access may have been made possible through hacking, or a phishing or spear-phishing ploy, or other social engineering techniques.
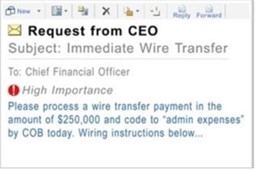 Then, the scammer sends the target employee a phony email requesting that a wire transfer payment be sent to one of those vendors. All too often, the employee is tricked into wiring the money to an account that has been set up and is controlled by the criminal. Whether this scheme works in any given case depends on how sophisticated the phony email looks, and how busy or distracted the target employee is at the time.
Then, the scammer sends the target employee a phony email requesting that a wire transfer payment be sent to one of those vendors. All too often, the employee is tricked into wiring the money to an account that has been set up and is controlled by the criminal. Whether this scheme works in any given case depends on how sophisticated the phony email looks, and how busy or distracted the target employee is at the time.
This cybercrime is also sometimes known as CEO fraud because scammers often spoof the name and email address of the employee’s CEO or some other C-level executive. Many organizations display their C-suite on the Leadership page of the website, complete with executive biographies and photos. This makes it easy for a scammer to research an executive in order to spoof him or her more realistically. It’s no wonder that a general employee, upon seeing an urgent email from an executive, would act quickly to fulfill the request.
How to Spot a Business Email Compromise Scheme, and What to Do
Often, business email compromise schemes can be identified before any damage is done, provided employees know what to look for. Following are some tips you can share with your employees, courtesy of the FBI and IC3.
- Employees should be suspicious anytime they receive an email or phone call requesting their account username and/or password.
- They should pay careful attention to the email address that is sending the request. Emails can be spoofed to trick employees. Cybercriminals cannot use the organization’s actual domain because they need any replies to come directly to them. Addresses that have slight variations from the real domain are easy clues for employees who are alert enough to spot them. For example, steve.smith@fedexp.com is a spoof or fake of the real steve.smith@fedex.com.
- Another giveaway is an unusual request concerning the wire transfer, such as instructions to bypass normal payment procedures due to urgency, or to communicate only by email, as two examples.
- If anything seems the least bit off about any email requesting a wire transfer, the employee should double-check the source of the email address. Simply hover the cursor over the email address in the email header to identify the sending source. As an example, in the email header (or From field) the sender appears to be steve.smith@fedex.com. Hovering over the email address reveals a source email of 123abc@fakee-mail.com, for example, which is obviously not a legitimate source.
These employee awareness tactics will help avoid business email compromises in most cases. And there are additional email safeguards you can implement to better protect your organization and employees.
However, in the event that your organization is victimized, it’s important to act quickly. Contact your financial institution immediately and request that they contact the financial institution where the transfer was sent, to advise them of the scam. Then, contact your local FBI field office to report the crime, and file a complaint with the Internet Crime Complaint Center (IC3).
Remember, business email compromises were the #1 cybercrime reported in 2021 and cost nearly $2.4 Billion. Don’t take them lightly.
Top Cybercrimes in Florida in 2021
Much of the data collected by the IC3 can be sorted by various parameters, including state. In 2021, for example, Florida had 1,546 victims of business email compromises. BEC was #8 on the top ten list of cybercrimes in Florida, as reported to the IC3—but was #1 in terms of cost to victims, at more than $192 Million for the year.
Among the more prevalent cybercrimes in Florida were identity theft (with 8,225 victims reported), non-payment or non-delivery scams (6,194), personal data breaches (4,132), cyber extortion, which includes ransomware (2,541), and phony tech support scams (2,110).
Who hasn’t had a call from a concerned voice (foreign), claiming to be Steve or Dave or Mike (not), informing you that your computer has been compromised (it hasn’t) but they can easily fix it for you? (We all have, no doubt.) Simply share your screen or grant Dave access and he’ll take care of it. (And will he ever!)
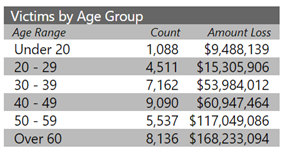
In addition to other demographics, the Internet Cybercrime Complaint Center also tracks financial losses by age group. In Florida, the greatest losses were sustained by victims over 60 years of age, who collectively lost more than $168 Million to cybercrime last year. Victims aged 40 to 49 suffered slightly more crimes, but their losses were only about one-third of those of the over-60 victims.
Top Robocall Complaints in 2021
2021 was also a banner year for certain robocalls. For the second consecutive year, the top robocall complaint filed with the Federal Communications Commission was the ubiquitous Auto Warranty Renewal call. These calls often include details about your particular car so that they seem more legitimate.
Most consumers reported that the unwelcome warranty calls include an automated or prerecorded message instructing them to press a certain number to speak with a live operator about their warranty, or to press a certain key to remove themselves from the call list.
With robocalls that offer these options, Don’t Press That Key! As much as you want to believe that good will come of it, pressing that key will simply lead to more robocalls because you have just verified to the robocall center that your phone number is valid and active. And that makes you an attractive target for future robocall scams.
Other common robocall scams in 2021 included calls phishing for social security numbers or credit card numbers. Calls offering fake insurance and phony healthcare benefits. And calls advising that you have been named in a (fake) lawsuit, or that criminal charges (fake) have been brought against you. These scams and others rely on creating fear, uncertainty, and doubt in the minds of their targets—so keep your guard up and put your phone down.
How to Handle Robocalls
Most robocalls target residential landlines and cell phones, although a few scams also target small businesses. The FCC has provided the following guidance for protecting yourself from annoying, and potentially dangerous, robocalls.
- Do not answer calls from unknown numbers. If you do so by mistake, hang up immediately.
- Never give out personal or financial information to someone who calls you.
- Be suspicious and cautious if you are pressured to reveal information or send money fast. Hang up.
 If you answer the phone and the caller—or a recording—asks you to hit a button to stop getting the calls, hang up. Scammers often use this trick to identify attractive targets.
If you answer the phone and the caller—or a recording—asks you to hit a button to stop getting the calls, hang up. Scammers often use this trick to identify attractive targets.- Do not respond to any questions, especially those that can be answered with a simple “Yes.” The scammer may be recording you and can use that verbal “yes” later to pretend you agreed to something you did not.
- If you get an inquiry from someone who says they represent a company or a government agency, hang up and verify the authenticity of the request by calling the phone number on your account statement or on the company’s or agency’s website. Legitimate sources generally send a written statement in the mail before calling you, particularly to ask for a payment.
- Talk to your phone company about call blocking tools they may have and check into apps that can be installed on your mobile device to block unwanted calls.
- To block telemarketing calls to your landline or cell phone, register your number on the Do Not Call List at https://www.donotcall.gov. Legitimate telemarketers consult the list to avoid calling those phone numbers, although they seem to be grossly outnumbered by scammy telemarketers who don’t bother checking the list.
Summary
There are a number of resources in the U.S. who collect data about cybercrime, and the FBI’s Internet Cybercrime Complaint Center (IC3) is one of them. Of all the cyber crimes reported to IC3 in 2021, business email compromises, or compromises of email accounts, topped the list in terms of the financial cost. Business email compromise schemes target organizations who routinely conduct wire transfers as part of their business.
Business email compromises cost victims close to $2.4 Billion in 2021, which is more than one-third of the total cost of all cybercrimes reported to the IC3 in 2021. Organizations who frequently wire payments to vendors, for example, should be aware of the popularity of this cybercrime and the precautions they can take to reduce their likelihood of being victimized. Training employees to be aware of email and phone phishing schemes, and how to identify them, is a good place to start.









