For businesses, suppliers, and contractors working with the Department of Defense, CMMC 2.0 is a contractual requirement (DoD). These rules must be followed regardless of what services or supplies you supply to the government. What steps is your company taking to address this issue? Are you ready for it?
With the goal post constantly shifting, how can my organization be compliant? The Department of Defense (DoD) announced an update to the CMMC program back in November 2021, dubbed CMMC 2.0. The rule-making process for CMMC 2.0 has been underway now for a lengthy amount of time, and it was expected to take between 9 to 24 months. CMMC 2.0 is now a mandatory contractual obligation for suppliers, organizations, contractors, and sub-contractors providing products and services to the DoD. Every contractor in the defense industrial base must conduct a self-assessment once per year. However, the same is not true for third-party assessments. CMMC 2.0 understands that different types of sensitive information require different degrees of protection. As such, third-party assessment requirements will consequently be based on the type of information DIB companies are working with.
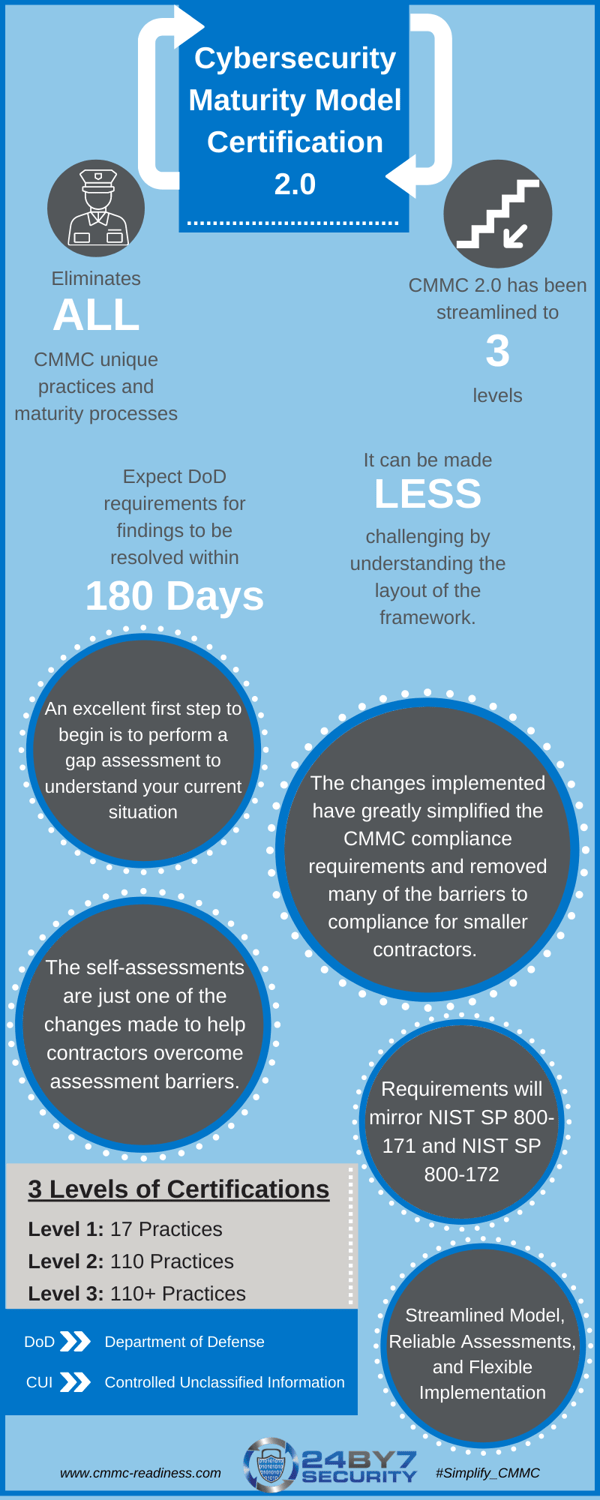
One of the biggest changes done from CMMC 1.0 has been the removal of two levels from the original. CMMC 2.0 will include three (3) levels, as opposed to five (5) in CMMC 1.02. Levels 2 and 4 have been removed from the model. The basic safeguarding controls of FAR 52.204-21 will be included in Level 1, dubbed "foundational." There were no changes in terms of security controls. Those required to be CMMC Level 1 will be able to self-assess their cybersecurity posture (annually) with leadership sign-off and enter their score into the Supplier Performance Risk System once CMMC 2.0 is in place (more on that below) (SPRS).
In this blog post, we'll explore each of the three levels.
Level 1: Foundational
Only companies that focus on the protection of FCI are eligible for Level 1 (Foundational). It's similar to the old CMMC Level 1 system. Level 1 will focus on the protection of FCI and will be based on the 17 rules listed in FAR 52.204-21, Basic Safeguarding of Covered Contractor Information. These controls aim to safeguard covered contractor information systems by restricting access to only authorized users.
3rd party certification will not be required for companies seeking Level 1 criteria. Instead, the contractor must define the people, technology, facilities, and external suppliers who handle, store, or transmit FCI in their environment. Companies will be required to self-certify once a year that they meet the FAR clause 52.204.21 fundamental safeguarding criteria for FCI.
Level 2: Advanced
Companies that deal with CUI at Level 2 (Advanced) are eligible. It's similar to the old CMMC Level 3 system.
All practices and maturity procedures that were unique to CMMC will be deleted under CMMC 2.0 Level 2 (Advanced) criteria, which will reflect NIST SP 800-171. Instead, Level 2 follows the National Institute of Technology and Standards (NIST14 )'s levels and 110 security measures for CUI protection. As a result, the DoD's 20 requirements in the old CMMC Level 3 were deleted, bringing the new Level 2 (Advanced) into complete compliance with NIST SP 800-171.
Every three years, you'll require a third-party review if you're pursuing CMMC level 2. The Department of Defense has reversed its earlier claims that level 2 standards would be bifurcated. This means you'll need to hire accredited C3PAOs (CMMC Third Party Assessment Organizations) or professional CMMC Assessors to assess you.
Level 3: Expert

The goal of Level 3 (Expert) is to reduce the danger of Advanced Persistent Threats (APTs). It is intended for companies that collaborate with CUI on the Department of Defense's highest-priority programs. It's comparable to the CMMC Level 5 in the past. The Department of Defense is still determining the Level 3 (Expert) security criteria, however, it has stated that they will be based on NIST SP 800-171's 110 controls plus a subset of NIST SP 800-172 controls.
Level 3 (Expert) compliance requires companies to achieve the security criteria outlined in NIST SP 800-171, as well as a portion of the requirements outlined in NIST SP 800-172. The Department of Defense is still working out how firms seeking level 3 compliance will be evaluated. These businesses, on the other hand, will need a DIBCAC audit to be in compliance.
At this time, no C3PAO assessments of defense contractors are being conducted. The final assessment process for C3PAOs is slated to begin in the summer of 2022, according to the Department of Defense. Contracts will be eligible to undertake optional assessments with certified C3PAOs at that point.
CMMC 2.0 Maturity Model Certification
In addition to the 3 levels, the CMMC 2.0 is composed of 110+ practices, most of which are part of the NIST SP 800-171 requirements.
The domains are further broken down into capabilities, with only certain capabilities required for each level. Organizations that are looking to achieve Level 3 certification must comply with more than 110 practices.
The following infographic gives a brief outline of how many practices are associated with each level. While navigating the CMMC is a complex process, it's advisable to turn to compliance experts like the team at 24By7Security to go through any of your questions.
24By7Security is a Registered Provider Organization (RPO), certified by the Cyber AB (formerly known as CMMC Accreditation Body), fully qualified, and trained to provide CMMC readiness services and help contractors in the Defense Industrial Base on their path to certification against the CMMC standard.
%20Combo%20Graphic%20Horizontal.png?width=497&name=RP(O)%20Combo%20Graphic%20Horizontal.png)







.png)


