What is Microsegmentation?
Microsegmentation is a method of heightening network security by logically splitting up workloads and data centers by implementing granular segmentation policies. Typically, organizations invest the majority of their resources in securing their network from external attacks through the use of firewalls or intrusion prevention systems (IPS). However, if a breach occurs in this system, intruders will have access to all of the information in the entire data system. In addition, actors who already have internal access would be able to access the entire data system, while they should only have access to parts of the system relating to their responsibilities.
A prominent example of this danger was the 2019 Quest Diagnostics data breach. Hackers gained access to the website of the American Medical Collection Agency (AMCA) and executed a man in the middle attack. AMCA is the billing collections vendor for Quest Diagnostics, and this breach allowed hackers to access the payment and personal information of 11.9 million Quest Diagnostics patients. If Quest Diagnostics had employed microsegmentation to protect their servers, this data security incident could have limited the misappropriation of data and patient records as it allows for greater internal protection of information by reducing potential server-to-server threats by securely isolating networks from each other. Cyberattacks can lead to actual damage as well. In 2015, hackers attacked an unnamed steel mill in Germany and disrupted control systems to the extent that a blast furnace malfunctioned and caused massive damage. Hackers entered the system using a spear-phishing attack, and due to the lack of internal security, the hackers were able to compromise numerous company systems, including the production network. Microsegmentation could have reduced the intensity of the attack, limiting the hacker’s control to the initially infected system, and thus could have prevented the blast furnace from malfunctioning.
Microsegmentation is different from network segmentation in that microsegmentation is optimal for increasing security for server-to-server traffic, which is found within a data center. Network segmentation is optimal for increasing security for client-to-server traffic, which is the transfer of data between a data center and a network external to the overall data center network. With companies using and processing more and more data, amounts of internal server-to-server traffic are increasing and becoming more vital to the daily functions of all organizations. Securing this traffic is crucial, and microsegmentation is one of the best methods for doing so.
Ultimately, the optimal method of securing a data system is not just network segmentation or microsegmentation, but an effective combination of both. The internal security that microsegmentation provides would be worthless without the perimeter defenses contributed by network segmentation, and vice-versa.
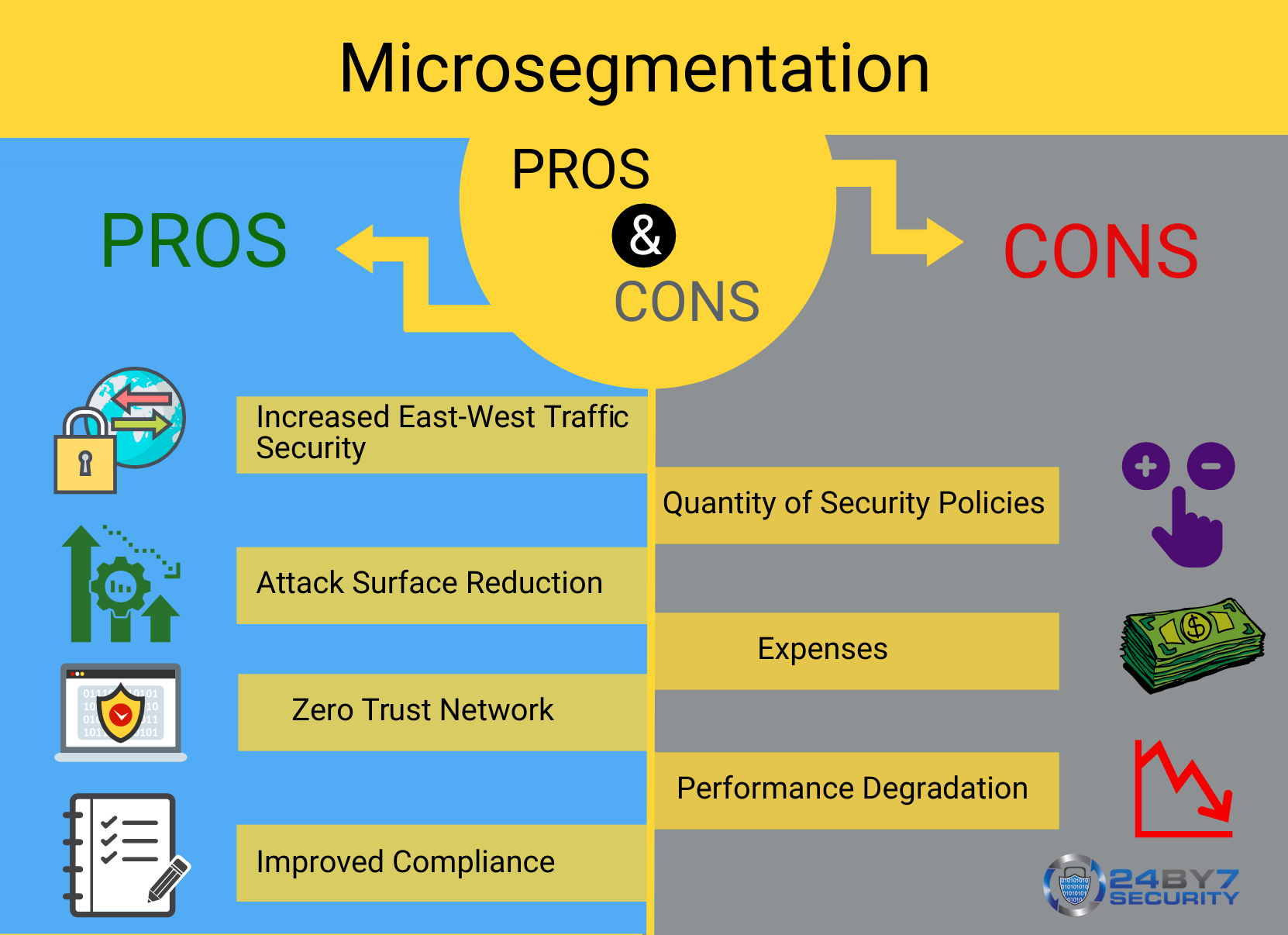
Advantages of Microsegmentation
- Increased East-West Traffic Security: As said before, microsegmentation allows for traffic between servers to be more secure through the implementation of granular segmentation policies and the logical division of workloads. If a breach occurs, its impact will be reduced with microsegmentation.
- Attack Surface Reduction: Additional reliance on cloud computing, combined with general increases in data manipulation, have augmented the attack surface through which hackers can penetrate. Microsegmentation adopts new policies that close any gaps created by data expansion or any existing gaps.
- Zero Trust Network: A zero-trust network operates on the principle that networks should never unquestionably trust anything inside or outside of its confines, and should always verify every system attempting to connect to the network. Microsegmentation is one of the best methods to bring a network closest to zero-trust through the use of extensive isolation measures.
- Improved Compliance: Microsegmentation aids organizations in enhancing their compliance with government regulations since networks processing relevant data are isolated and secured. Regulated data can be isolated, and regulatory conditions can be appropriately applied to the data system’s communications.
Disadvantages of Microsegmentation
- Quantity of Security Policies: A large number of security policies or access control lists (ACL) which govern the segments of data are challenging to manage and maintain. The security policies are granular, and microsegmentation could exponentially increase the number of policies and segments used.
- Expense: Microsegmentation can become very expensive, depending on the number of policies implemented and the number of security inspections conducted. More infrastructure is required to manage additional policies. Security inspections also require more human resources.
- Performance Degradation: Additional gateways created from microsegmentation result in bottlenecks between segments, which reduces the performance of the system.
Implementation of Microsegmentation
The implementation of microsegmentation varies depending on the situation. In organizations where security is of the utmost importance, more zones of control may be implemented to provide for additional protection. In a hospital, for example, certain medical technologies such as X-rays or MRIs contain and process important regulated information that must be kept secure. Thus, each of these machines may be given its own segment to ensure that the data is kept safe, even in the event of a security breach. However, devices that do not hold essential data do not have to be assigned their own segment. Those devices would likely be assigned to segments with several other devices, given that they do not contain regulated data. But, users, not just devices, must be segmented as well, to protect the network from external threats such as phishing emails. Besides, systems should be segmented based on their purposes too — for example, there are hospitals that have networks dedicated to IoT devices. The same principles would apply to other organizations as well. The importance of the data contained and analyzed on a server or device dictates the level and intensity of microsegmentation that should be implemented. Users should have limited access, as well. Also, specific networks should be segmented based on the permissions or purposes of the devices within them.
You can conduct a security risk assessment of your networks and devices to prepare a comprehensive segmentation strategy. Your segmentation strategy should always be driven by the criticality of your assets and the data they manage.
At 24By7Security, we are Cybersecurity & Compliance Specialists with extensive hands on experience helping businesses build a defensive IT Infrastructure against all cyber security threats. We are your first line of defense against a cyber attack. Schedule a consultation with us today.





.png)


