What we can learn from these three cybercrimes?
We don’t need to state the obvious – that 2020 was a year of anomaly – but perhaps we should remind you that when the going gets tough, the hackers get going. Cybercrime loves a good disaster or compelling emergency that shifts everyone’s emphasis away from data security.
When our businesses are focused on survival, income, and hope … it’s easy for our usual cybersecurity concerns to take a back seat. However, cybercriminals proved more innovative and aggressive than ever in 2020.
This article presents our top three picks for the strangest breaches in an even stranger year.
Pick #1 – Who Hacked the WHO and Why?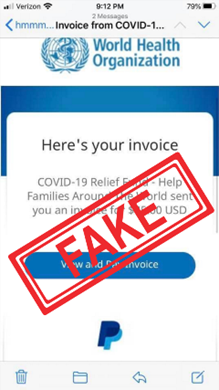
The Hack
The pandemic hadn’t been in the news two weeks before the World Health Organization was forced to fend off hacking attempts and phishing schemes while trying desperately to organize a global response to the pandemic. While it doesn’t appear that the attacks were aimed at bringing the WHO down, the opportunistic phishing and spear-phishing antics did disrupt the organization as it attempted to solicit legitimate monetary donations to help in the response.
According to the World Health Organization, a leader in the global charge against COVID-19, the cybercriminals conducted phishing campaigns fraudulently soliciting funds to help in the fight against COVID-19.
Among their cyber ploys were requests to provide usernames and passwords, to click on phony “Donate Here” links, and to open malicious attachments, including invoices for monetary donations.
Cybercriminals also solicited participation in sweepstakes, lotteries, prize drawings and other contests in attempts to steal donations. Any of these ploys enable them to install malware on personal computers and smartphones and steal sensitive individual information or money.
The Facts
The WHO’s only call for donations is the COVID-19 Solidarity Response Fund; any other appeal for funding or donations that appears to be from WHO is a scam, according to the organization.
WHO suggests always checking to make sure any link to them starts with ‘https://www.who.int’ or, even better, donors should navigate directly to the WHO website by typing ‘https://www.who.int’ into your browser.
This is always good policy and helps avoid the consequences of clicking on malicious links. Says WHO: “All donations are welcome.”
We wonder, fleetingly, what might happen if these criminal opportunists channeled that profiteering energy and skill into a legitimate, productive initiative aimed at the greater good?
Pick #2 – Irony Among the Icons
It was more than a little ironic when three well-known, publicly-traded network security software companies became the victims of security breaches in December. All three firms provide services and software globally to organizations across numerous industries, including government agencies.
The Hacks
SolarWinds, an Austin, TX-based firm, provides software to help businesses manage their networks, systems, and IT infrastructures. As early as March 2020, SolarWinds software was compromised by cybercriminals, who secretly injected malicious code into SolarWinds’ Orion information technology and network monitoring and management software updates being shipped to SolarWinds customers.
In this attack, it appears the Security Assertion Markup Language (SAML) Signing Certificate was compromised through the use of falsified Active Directory privileges, which then allowed unauthorized tokens to be created and effectively used to access and exploit email and other resources in order to steal data using APIs. The Cybersecurity and Infrastructure Security Agency (CISA) also suggested that other access vectors were being used in addition to the SolarWinds Orion platform. This hack has had implications for SolarWinds customers all over the world.
In early December, the National Security Administration (NSA) indicated that a vulnerability in VMware Access and VMware Identity Manager software was being exploited by Russian state-sponsored cybercriminals. VMWare, a $9 billion software firm headquartered in Palo Alto, CA, provides cloud computing and virtualization software and services globally. The exploit enabled cybercriminals to abuse federated authentication and access protected data.
 The NSA explained that the hacking “led to the installation of a web shell and follow-on malicious activity, where credentials in the form of SAML authentication assertions were generated and sent to Microsoft Active Directory Federation Services (ADFS), which in turn granted the access to protected data.”
The NSA explained that the hacking “led to the installation of a web shell and follow-on malicious activity, where credentials in the form of SAML authentication assertions were generated and sent to Microsoft Active Directory Federation Services (ADFS), which in turn granted the access to protected data.”
FireEye, a $900 million global cybersecurity firm based in Milpitas, CA, provides hardware, software, and services to help protect organizations against malicious software, analyze IT security risks, and investigate cybersecurity attacks.
In December, FireEye reported that attackers had broken into its networks and stolen hundreds of proprietary software tools. The software is used by FireEye customers to secure their networks.
FireEye was able to trace this software theft back to the malicious code injection attack on SolarWinds software.
The Facts
These cybercriminals launched their exploits after first gaining access to their victims’ on-premise networks. In-house IT teams across industries should review all network security tools and procedures, paying particular attention to privileged access parameters and administrator credentials used to access both cloud and on-premise assets.
Email appears to have played a key role in these exploits, and security should be shored up around that organizational platform as well. More on email exploits shortly.
Pick #3 – High Stakes in the Vaccine Game
The rewards are unprecedented for companies who introduce the first COVID-19 vaccines to the global market. Competition is fierce, not only for manufacturers and distributors, but also for nation-states vying for a strategic advantage. In the cut-throat pharmaceuticals industry, intellectual property related to cures and medicines is highly prized—to the point of being worth stealing for a variety of reasons.
As early as July 2020, the U.S. Department of Homeland Security announced that an espionage group was targeting pandemic-related medical research being conducted in the U.S., Canada, and Britain. The group is believed to have ties to Russia.
The Hack
Against this backdrop, it was no surprise when Dr. Reddy’s Laboratories, an India-based manufacturer of COVID-19 vaccine as well as generic drugs, was forced to close plants in Brazil, India, Russia, the U.K., and the U.S. The closure occurred in October 2020 following a cyberattack on the firm’s data servers. According to a news report by India’s Economic Times, the servers house proprietary pharmaceutical data as well as sensitive data related to clinical trials, patients, and clients.
 The India-based company is the contractor for Russia’s “Sputnik V” COVID-19 vaccine, which was about to enter Phase 2 human trials. The Drug Control General of India (DCGI) gave the go-ahead for Phase 2 trials on October 19th, and within days the data servers had been hacked. In addition to shutting down plants, the drug-maker has isolated all data center services while remediating the breach.
The India-based company is the contractor for Russia’s “Sputnik V” COVID-19 vaccine, which was about to enter Phase 2 human trials. The Drug Control General of India (DCGI) gave the go-ahead for Phase 2 trials on October 19th, and within days the data servers had been hacked. In addition to shutting down plants, the drug-maker has isolated all data center services while remediating the breach.
Dr. Reddy’s is not an isolated incident. In early December, pharmaceuticals manufacturer Pfizer and its partner BioNTech disclosed that their data had been hacked. Information supporting the regulatory submission for emergency-use approval of their COVID-19 vaccine had been hacked on a European Medicines Agency (EMA) data server.
The Facts
Aside from the talented chemists who develop drugs and medicines, the intellectual property they create is a pharmaceutical company’s most valuable resource. In the no-holds-barred COVID vaccine game, all pharmaceutical companies are cautioned to double-down on their IT and cybersecurity programs in order to ensure their prized assets are exceedingly well-protected. The stakes couldn’t be higher.
Opportunistic Nuisance Threats
Since March of 2020, when the pandemic began to dominate headlines on a daily basis, the opportunities to profit from cybercrime have become so tempting that a host of proven attack vectors have been repurposed for these unique times.
Phony Amazon webpages offer a variety of personal protective equipment for sale, and new sites pop up as quickly as others take the money and fold. Buyers who have fallen prey to these bogus offers can kiss their current credit card data goodbye. Websites related in various ways to the pandemic have mushroomed, with 2% to 10% of them estimated to be fake sites with malicious purposes. Don’t be hasty in researching the PPE you need, and if it sounds too good to be true – what’s that adage?
With hundreds of thousands of employees working from home in the U.S. alone, an unprecedented number of unsecured home computers provide tempting targets for cybercriminals. By conducting brute force attacks on unsecured RDP (remote desktop protocol) machines, hackers can take control of them, tie them into botnets, and use them to spew malicious emails with criminal intent – often with the computer user none the wiser. These attacks can also have more serious effects and consequences.
Similarly, it was months before overnight phenom Zoom realized that skyrocketing demand was compromising its online meetings and their participants. Cybercrimes launched by innumerable links containing the word zoom increased a thousand-fold in 2020.
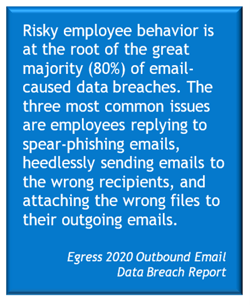
Employee email communications were also more vulnerable in 2020. In September, a 2020 Outbound Email Data Breach Report was published by Egress, whose mission is to “prevent human error and protect against malicious or reckless behavior on email” using a unique human layer security platform.
IT leaders across major industries were surveyed, with 93% reporting they had experienced data breaches through outbound email in the past year. 94% reported an increase in email traffic since COVID-19, and more than two-thirds (70%) believe that remote work contributed to the rise in email data breaches in 2020.
Risky employee behavior was at the root of 80% of the breaches, according to the report, with the three most common issues being employees replying to spear-phishing emails, sending emails to the wrong recipients, and attaching the wrong files to emails. Distractions and stress associated with working from home contributed to the most serious email data breaches in 2020.
Summary
The year 2020 will be remembered as an historic anomaly of epic proportions, much as the Spanish Flu pandemic was an anomaly of the 20th century and the Cholera pandemic of the 19th century. Three unusual cybersecurity breaches took advantage of the unique opportunities afforded by the COVID-19 pandemic.
Cyberattacks on the World Health Organization siphoned off monetary donations and disrupted the organization’s important focus. Attacks on big pharma aimed to steal intellectual property, from vaccine formulas to clinical trial and patient data, and also disrupted organizational focus. And attacks on global security software firms shook our collective faith in commercial cybersecurity protections at a time when we were more vulnerable than usual.
In addition to crimes of profiteering, nuisance attacks spurred by the pandemic disrupted some of our best attempts to conduct business by working from home, meeting online, and maintaining active email communications with coworkers, clients, suppliers, and prospects.
The moral of all of these stories is that we must remain vigilant and proactive about our security. We must maintain situational awareness as we continue to browse, buy, and conduct business online. And we must invest in ongoing improvements to our cybersecurity systems to avoid becoming the low-hanging fruit that is so tempting to cybercriminals.