Here’s help making the right decision for your healthcare organization
Whether you operate a large hospital or a small private practice, HIPAA compliance is always one of your top priorities. And one of your top tools for ensuring HIPAA compliance is the HITRUST Cybersecurity Framework.
Overview of HITRUST for Healthcare
HITRUST is a certifiable framework that offers any healthcare entity a thorough, adaptable, effective way to manage risk and comply with HIPAA regulations and other required security standards. HITRUST offers a step-by-step guide to achieving the appropriate level of information security and cybersecurity based on the size and scope of your healthcare organization. It provides a clear path to certifying that you are fully HIPAA compliant. What’s not to love?
Where is HITRUST Required?
 There is no federal regulation that requires HITRUST adoption. However, in 2016 several of the largest health insurance payers and health plans decided that all of their vendors must adopt HITRUST.
There is no federal regulation that requires HITRUST adoption. However, in 2016 several of the largest health insurance payers and health plans decided that all of their vendors must adopt HITRUST.
Since then, most payers as well as a growing number of hospitals and health systems have made HITRUST adoption a requirement for the entire healthcare industry. One reason is that so many healthcare organizations are still not fully HIPAA compliant, and the U.S. Department of Health and Human Services (HHS) Office for Civil Rights (OCR) is cracking down on violators.
Today, adopting the HITRUST Cybersecurity Framework is a requirement for healthcare organizations and business associates who generate, access, store, or exchange Protected Health Information (PHI) or Electronic Protected Health Information (ePHI). The HITRUST Framework integrates the extensive and detailed HIPAA requirements along with other regulations that apply to healthcare providers, such as payments, accounting, and financial standards.
Although there are no requirements for HITRUST adoption outside of the healthcare industry, any organization can benefit from using the HITRUST Framework as a path to compliance with the regulations and standards that apply in their industry.
Adopting the HITRUST Framework requires the healthcare organization to undergo an information security assessment, and there are several types and levels to choose from as described below.
First, Choose a Readiness Assessment or a Validated Assessment
Healthcare organizations can select from two types of HITRUST assessments at the outset of your journey to compliance.
Validated Assessment. A validated assessment requires a HITRUST Authorized External Assessor to evaluate compliance with the applicable HITRUST Cybersecurity Framework requirements. Validated Assessments are certifiable and renewable.
Readiness Assessment. Many organizations opt for a HITRUST Readiness Assessment before they undertake the rigors of a Validated Assessment. A Readiness Assessment can be conducted by an Authorized Readiness Licensee, such as 24By7Security, or facilitated by a HITRUST Authorized External Assessor.
Starting your journey with a Readiness Assessment is the best way to position your healthcare organization for a successful Validated Assessment. It will also help determine whether you have a strong enough business case to support adopting HITRUST for healthcare.
As a HITRUST Readiness Licensee, 24By7Security is authorized to perform consulting and readiness services for healthcare organizations who want to adopt the HITRUST Cybersecurity Framework in order to achieve and demonstrate complete HIPAA compliance. We can assist you in implementing the Framework, conducting remediation activities to address any compliance gaps, and preparing for a successful HITRUST Assessment. Learn more about the HITRUST Readiness Assessment services that are available to you.
Next, Choose the HITRUST Assessment Level that Works Best
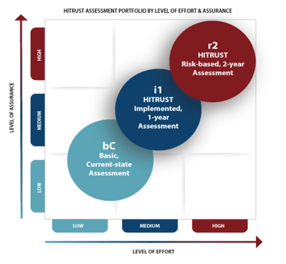
There are three different levels of HITRUST adoption to choose from, depending on needs and other factors in your particular organization. Below is an overview to assist you in deciding which level is right for your organization.
1 - Basic Current-State (bC) Assessment
- This is the lowest level of information security and cybersecurity assurance, and as such it does not produce certifiable results or lead to HIPAA compliance certification.
- This is a standardized self-assessment that emphasizes excellent security hygiene. It uses the HITRUST Assurance Intelligence Engine to identify errors and omissions in compliance.
- This assessment requires only a modest degree of work, which makes it an effective substitute for the Consensus Assessment Initiative Questionnaire (CAIQ) developed by the Cloud Security Alliance.
2 - Implemented 1-Year (i1) Validated Assessment + Certification
 This assessment is an evaluation of best practices, and it works well in moderate risk circumstances. It is a good choice when the Basic Assessment does not offer sufficient assurance, and the most advanced assessment (below) is not reasonable.
This assessment is an evaluation of best practices, and it works well in moderate risk circumstances. It is a good choice when the Basic Assessment does not offer sufficient assurance, and the most advanced assessment (below) is not reasonable.- The One-Year Assessment is threat-adaptive, which means that requirements are periodically added to and removed from the HITRUST Framework to reflect the constantly changing threat landscape.
- This assessment uses a static, non-customized set of 219 required controls, which the assessor will evaluate for each organization.
- The One-Year Assessment can be completed either as a Readiness Assessment or through a third-party assessor organization. The assessment must be verified by HITRUST, who will then issue a certification that is valid for one year.
3 - Risk-based 2-Year (r2) Validated Assessment + Certification
 This assessment is identical to the legacy HITRUST CSF Validated Assessment. It is tailored to the individual healthcare organization and considers a variety of scoping factors in order to determine the size and scale of the assessment.
This assessment is identical to the legacy HITRUST CSF Validated Assessment. It is tailored to the individual healthcare organization and considers a variety of scoping factors in order to determine the size and scale of the assessment.- The Risk-Based Two-Year Assessment is most suitable for high-risk environments or scenarios where a high degree of security assurance is required. A business associate who stores volumes of ePHI for various healthcare providers would be one of many examples.
- This assessment has no equal in the security industry. However, it is a challenging and exhaustive assessment involving several times the level of effort as the One-Year Assessment. One reason is that the assessor must evaluate requirements across three to five cybersecurity maturity levels, including reviewing 1,500 or more pieces of documentation.
- After validating this assessment, HITRUST will issue a certification good for two years.
Depending on which level of HITRUST assessment you choose, different costs and completion times will apply. For more information, watch the webinar entitled “Is HITRUST Right For Me? Your Path to HIPAA Compliance.”
Summary
Healthcare organizations are required to comply with an extensive set of HIPAA regulations. The primary purpose is to safeguard the security and privacy of their patients’ Protected Health Information (PHI and ePHI). The HITRUST Cybersecurity Framework offers healthcare organizations a clear and proven path to HIPAA compliance as well as compliance with other applicable regulations.
HITRUST for healthcare offers the choice of a readiness assessment or a validation assessment. Following this decision, organizations can choose one of three levels of HITRUST assessment based on their individual needs and objectives. Choices include a basic assessment, a one-year validated assessment, and a two-year validated assessment.
Validated assessments provide healthcare organizations with certificates that demonstrate HIPAA compliance. Certificates can be very useful when dealing with the HHS and its HIPAA compliance enforcement agency, the Office for Civil Rights (OCR). They enable providers to display proof of HIPAA compliance to their patients, and business associates to prove their compliance as well. For these and other reasons, HITRUST for healthcare organizations should be considered very seriously, and very soon.









