Last year, 3,950 confirmed data breaches affected virtually all industries in the U.S., according to at least one source. It took organizations an average of 228 days – more than seven months – to realize they had been breached. And then an average of 80 days, or almost three months, to contain the breach. Pretty grim security statistics for a pretty grim year all around.
2020 was a record year for data breaches in the U.S., as well as a record year for data breaches in the healthcare industry.
Most Expensive Data Breaches, by Industry
In 2020, five industries accounted for the most expensive costs per data breach, according to the 2020 Cost of a Data Breach Report published annually by IBM and the Ponemon Institute.

- Healthcare - $7.1 million per data breach in 2020
- Energy - $6.4 million
- Financial - $5.9 million
- Pharmaceutical - $5.1 million
- Technology - $5 million
The following costs are figured into the overall cost of a data breach, for purposes of the IBM Ponemon report:
- Data breach detection and response activities
- Legal fees, fines, and settlement costs
- Cost of victim notification
- Lost revenue
- Public relations, marketing, and sales efforts to regain customer trust
- Cost of increased customer support
The report also examined the types of data that were involved in breaches in 2020. Some 80% of all data breaches involved customer personally identifiable information (PII), which cost an average of $150 per lost or stolen record. Customer PII was compromised more often than intellectual property, sanitized customer records, or employee PII.
HIPAA Enforcement is on the Rise
For the past five years, healthcare has led all others as the industry with the most expensive data breaches.
This is likely due to increasingly close scrutiny by the Department of Health and Human Services (HHS) Office for Civil Rights (OCR). The OCR is responsible for enforcing compliance with HIPAA regulations. It also imposes financial penalties on healthcare entities whose violations lead to the potential or actual disclosure, abuse, or theft of protected health information (PHI). And the OCR has grown considerable teeth in recent years.
In 2020, the OCR conducted 19 HIPAA compliance investigations that resulted in larger financial penalties than in any previous year, according to a comprehensive report in the HIPAA Journal. These 19 cases, which targeted both healthcare providers and business associates, resulted in the payment of more than $13.5 million in penalties by the violators. That’s an average of $710,500 per case, which is not a small change.
Additionally, 11 financial settlements in 2020 were the result of violations of HIPAA Right of Access rules, where individuals were not provided with timely access to their medical records. The penalties ranged from $15,000 to $160,000 per case and were attributable to either long delays or outright refusals to provide records.
The OCR has been pursuing a specific initiative to discover and resolve Right of Access violations since late 2019.
Healthcare providers and business associates would be well-advised to take these OCR initiatives very seriously.
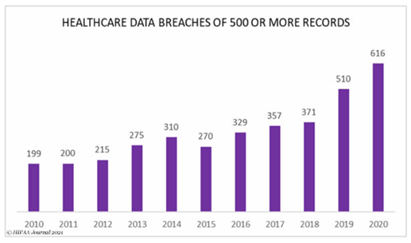
Healthcare Data Breaches Spiked in 2019 and 2020
In 2020, a total of 642 data breaches occurred in the healthcare industry.
96% of this number, or 616 breaches, encompassed 500 or more records. These breaches resulted in the exposure, compromise, or disclosure without authorization of more than 28.7 million healthcare records.
The number of healthcare industry data breaches that affected at least 500 records rose 21% in 2020 over the prior year. It took an even greater leap in 2019, rising 37% from 2018.
What these two spikes tell us is that the pandemic, which obviously had nothing to do with the spike in 2019, most likely had nothing to do with the lesser spike in 2020. More likely at work here is the increasingly proactive OCR oversight of the healthcare industry, and the persistent failure of some healthcare entities to take information security seriously.
Filtering the data further, we find that almost ten percent (63) of the 642 total healthcare data breaches last year affected 100,000 or more healthcare records, as reported by HIPAA-covered entities and business associates to the OCR.
Further still, the 20 largest healthcare data breaches last year affected well over 100,000 records, ranging from Trinity Health at 3.3 million individual health records to Northeast Radiology at 298,500 records. Of these top 20, three violators were health plans, six were business associates, and 11 were healthcare providers.
But the bad news doesn’t stop at the number of records breached or the high cost of financial penalties.
The average time to discover a data breach was 228 days across all industries or more than seven months. And in healthcare that average was 44% longer, at 329 days, or almost 11 months.
The length of time it takes to discover a breach is known to drive up the cost of the breach. One of the factors that may contribute to an organization’s inability to detect data breaches more quickly is inadequate or infrequent penetration testing and vulnerability testing.
Causes of All 2020 Data Breaches
Across all industries, the majority of 2020 data breaches were caused by hackers and malicious attacks, and the majority of those were motivated by financial greed.
IT system issues accounted for one-quarter of the breaches, and human error accounted for almost a quarter, according to the IBM Ponemon report.
- 53% caused by hackers and malicious attacks
- 25% caused by IT system issues
- 23% caused by human error
It is interesting to note that the most common malicious attacks derived from stolen login credentials, disfiguration of cloud servers and storage, vulnerabilities in third-party software, and the highly popular phishing scams.
Common IT issues include outdated software and unapplied patches, misconfigured systems, coding errors, weak access controls, and a lack of enforcement of strong password policies. Insecure websites are also being exploited.
Causes of 2020 Data Breaches in Healthcare
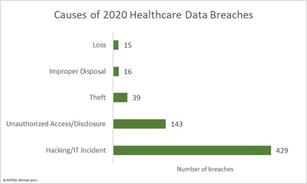
Data are collected and reported slightly differently in healthcare, making an apples-to-apples comparison with total data breach numbers difficult.
In healthcare, hacking and IT issues topped the list of data breaches, accounting for more than 66% of all healthcare data breaches in 2020, versus 78% overall.
Most IT issues involved the exploitation of system vulnerabilities, while phishing, malware, and ransomware contributed significantly to hacks and attacks.
Frequently, ransomware attacks begin with phishing or spear-phishing campaigns that enable attackers to take control of data, encrypt it, and hold it for ransom until the organization pays the cybercriminal(s) in bitcoin or cryptocurrency. The payment of lucrative ransoms occurs often enough that ransomware continues to rise across the globe.
Roughly one-quarter of healthcare data breaches in 2020 stemmed from unauthorized access and disclosure of protected health information (PHI). Year after year, the healthcare industry suffers breaches caused by its own employees, including:
- Disgruntled employees accessing records for personal gain or malicious motives
- Curious employees snooping into private records
- Unwitting employees disclosing PHI to the wrong people
- Employees committing other human errors that compromise PHI.
The remaining healthcare data breaches of 2020 were caused by the theft, loss, and improper disposal of health records. No doubt some of these incidents could also be attributed to human error.
The effect of human error and negligence in healthcare is just slightly higher than the percentage of human error contributing to data breaches across all industries. Employee training, retraining, and testing are vital in keeping this percentage under control and attempting to reduce it over time.
Poster Child for HIPAA Enforcement
The largest penalty imposed by the OCR in 2020 was $6.85 million for multiple HIPAA violations that led to a spectacular data breach at Premera Blue Cross. Hackers obtained the PHI of more than 10.4 million insured individuals.
Premera was cited for (1) failing to conduct a comprehensive risk analysis, (2) failure to reduce risks to the confidentiality, integrity, and availability of PHI to a reasonable and appropriate level, and (3) failure to implement adequate hardware and software controls. As with most OCR citations, Premera was also required to adopt a corrective action plan to address all violations, which is subject to monitoring by the OCR.
The health plan also paid an astounding $84 million to settle a multi-state legal action and a class-action lawsuit on behalf of victims of the data breach.
Summary
The year 2020 saw record-breaking numbers of data breaches in the U.S., with healthcare topping the list of the most expensive breaches for the fifth consecutive year. Hacking, malicious attacks, malware, ransomware, and phishing were responsible for the majority of 2020 data breaches, although human error, malice, and negligence caused a quarter of all breaches.
The top weapon in the defense against these and other threats is knowledge. It is vital that an organization knows exactly where it is vulnerable, knows where security safeguards are inadequate or missing altogether and know how to implement the necessary measures.
Because a risk assessment is the surest way to identify vulnerabilities and devise an intelligent plan for implementing all necessary security safeguards, the HHS Office for Civil Rights frequently penalizes healthcare entities for failure to conduct comprehensive risk assessments. That such assessments should be so often postponed or overlooked by healthcare providers is inexplicable.









