Electronic medical devices begin with design, engineering, and manufacturing. Finished devices are sold to healthcare providers, from hospitals and large private practices to medical centers and diagnostic services providers, who in turn use those electronic devices to assess patient health, monitor and treat disease, and help patients maintain healthy behaviors.
This blog addresses the healthcare provider environment and examines what actions healthcare providers can take to evaluate the security of the various electronic medical devices within their purview.
Device Manufacturers
Manufacturers of electronic medical devices are governed by ISO Standard 14971:2019 to guide them in producing medical devices that are digitally secure. From tiny implantable bio-monitors to massive magnetic resonance imaging machines, today’s electronic medical devices contain computers and can be connected to computer networks periodically or permanently.
The Food and Drug Administration (FDA) works closely with device manufacturers to promote high standards of device quality, efficacy, safety, and security. The FDA also leverages the National Institute of Standards and Technology (NIST) cybersecurity practices for connected electronic devices.
But the security risk, and the responsibility for device security, do not stop there.
Healthcare Providers Who Use Devices
Hospitals, medical centers, large medical practices, providers of diagnostic services, and similar service providers typically purchase or lease electronic medical devices to aid in the evaluation and treatment of patients.
Increasingly, these electronic medical devices are computer-controlled and network-connected. And while these features have made them highly intelligent and enormously useful, they have also made them attractive targets for malicious hackers and data thieves.
That’s because personally identifiable information (PII) and protected health information (PHI) are often digitally entered into these devices or are rendered accessible through their network connections in the hospital, diagnostic center, or other healthcare provider organization.
Rising Healthcare Data Breaches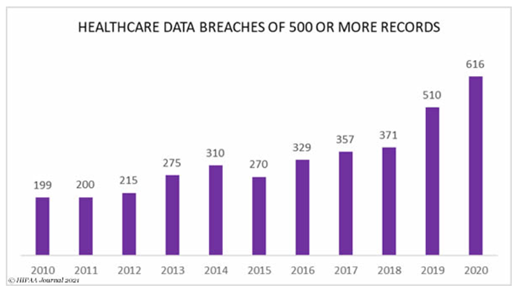
Healthcare providers are especially vulnerable to cybercrime and data breaches due to the sensitive nature of the patient information they maintain. This information is particularly profitable for those who offer it for sale on the black market in cyberspace.
Data breaches in the healthcare industry have been rising steadily over the past decade, with 2020 “the worst year ever for healthcare industry data breaches” according to the HIPAA Journal.
Over 615 data breaches affecting 500 or more records were reported to the HHS Office for Civil Rights, and more than 28.7 million healthcare records were exposed, compromised, or disclosed without authorization.
While it is currently undocumented how many breaches resulted from weak security of electronic medical devices and their network connections, certainly this has contributed to the problem as electronic medical devices continue to proliferate.
When Device Vulnerabilities Are Found
“Anytime a medical device has software and relies on a wireless or wired connection, vigilance is required. The software behind these products, like all technologies, can become vulnerable to cyber threats, especially if the device is older and was not built with cybersecurity in mind.”
That warning introduces the FDA consumer publication entitled Medical Device Cybersecurity: What You Need to Know, current as of October 2020, and recommended reading for healthcare providers.
When the FDA learns of a medical device that poses a cybersecurity threat, they generally share known details with all constituents who may be affected. The four examples below illustrate the FDA’s intention to alert not only device manufacturers to the known risk, but also healthcare providers, and frequently their patients.
- FDA News Release – March 3, 2020: FDA Informs Patients, Providers, and Manufacturers About Potential Cybersecurity Vulnerabilities in Certain Medical Devices with Bluetooth Low Energy
- FDA News Release – October 1, 2019: FDA informs patients, providers, and manufacturers about potential cybersecurity vulnerabilities for connected medical devices and health care networks that use certain communication software
- FDA News Release – June 27, 2019: FDA warns patients and health care providers about potential cybersecurity concerns with certain Medtronic insulin pumps
- FDA In Brief – May 7, 2019: FDA issues alert on potential premature battery depletion of certain Medtronic implantable pacemakers, approves related enhancements to the device
Following is an excerpt from the March 3, 2020 release listed above: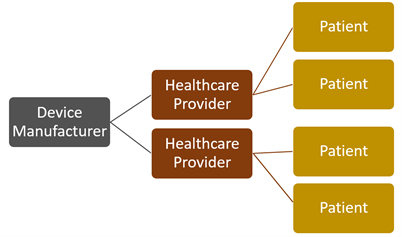
“Today, the U.S. Food and Drug Administration is informing patients, health care providers, and manufacturers about a set of cybersecurity vulnerabilities, referred to as “SweynTooth,” that – if exploited - may introduce risks for certain medical devices. … These cybersecurity vulnerabilities may allow an unauthorized user to wirelessly crash the device, stop it from working, or access device functions normally only available to the authorized user.”
Following is an example of FDA guidance from the October 1, 2019 release listed above:
“Medical device manufacturers should work with operating system vendors to identify available patches and other recommended mitigation methods, work with health care providers to determine any medical devices that could potentially be affected, and discuss ways to reduce associated risks.”
FDA security alerts are intended not only to inform manufacturers, healthcare providers, and patients of known security risks and vulnerabilities but also to encourage them to take action in addressing those risks and vulnerabilities. All may have responsibilities in these scenarios.
Current Security Standards
The healthcare industry is heavily regulated, and several regulations require that security risk assessments be conducted as part of an effective and compliant security program.
In particular, ISO/IEC 27001, the HIPAA Security Rule, the 21st Century Cures Act, and the CMS Interoperability and Patient Access rule require security risk assessments. These assessments also apply to electronic medical devices and their connectivity to networks, the Internet, and software applications.
Security Risk Assessment Scope and Inclusions
A comprehensive security risk assessment for electronic medical devices utilizes a five-point strategy for assessing risk related to people, communications, processes, personally identifiable information (PII) and protected health information (PHI), and a toolkit of various assessment technologies and security tests.
This strategy should also observe the nine-step risk assessment methodology promulgated by the National Institute of Standards and Technology in NIST Special Publication 800-30, which guides the conduct of security risk assessments.
In addition, the security risk assessment may utilize any or all of the accepted tests and best practices in the toolkit in evaluating the networks to which electronic medical devices are connected, the websites to which they may connect, and the software applications that may be installed in or otherwise used by the device. Internal and external vulnerability assessments and penetration testing are particularly useful in this phase.
As with all computer-driven devices, software updates for electronic medical devices must be installed immediately upon receipt by the healthcare provider, if they are not pushed to the device automatically from the manufacturer. Outdated software patches are among the most common security vulnerabilities in connected electronic devices.
Recognizing that the human factor is front and center in the installation, operation, and maintenance of electronic medical devices, social engineering testing should be a component of the security risk assessment. This may encompass evaluating procedures for the secure management of information assets throughout their life cycles. It will also include testing for physical security vulnerabilities, such as doors to MRI rooms and other such diagnostic equipment left unlocked, device sign-ons left open, weak passwords for device access, and a long list of similar device security risks.
This phase may also include testing employees for vulnerability to email scams and phishing attempts, in which hackers manipulate employees into revealing information they can use to gain access to the device and/or the network.
A thorough security risk assessment will verify that risk assessments have been recently completed for business associates and third-party vendors who support the healthcare provider. It will also verify that documented policies and procedures for cybersecurity and regulatory compliance are available and current.
Because a security risk assessment will, in most cases, uncover vulnerabilities relating to the electronic medical device and its network connectivity, a remediation roadmap will be developed as part of the final report. It will include recommendations for remediation measures to be implemented along with a ranking of risk severity and a prioritized plan for remediation based on the level of risk.
Summary
The FDA alerts manufacturers, healthcare providers, and patients when security vulnerabilities are found in electronic medical devices. Remediating those risks is a top priority for manufacturers and often drives healthcare provider involvement downstream.
Healthcare providers who purchase or lease electronic medical devices typically connect them to their networks on a periodic or permanent basis, which can expose not only the devices but also the entire network to malicious hacks and the theft of sensitive patient data.
The security risk assessments required by multiple healthcare regulations must be expanded to encompass all electronic medical devices within the healthcare provider environment. This is the only way hospitals, diagnostic service providers, medical centers, and other healthcare providers can ensure security and privacy for the patient-protected health information that may be accessible through these connected devices.









