Segmentation is essential to any network. It is one of the most fundamental things any engineer can implement, and it can be very effective.
Segmenting your organization’s network is an effective defense in depth method for containing damage from a successful cyberattack, especially ransomware. By segmenting a single network into multiple sub-networks, you can prevent a successful attack from immediately accessing your entire network.
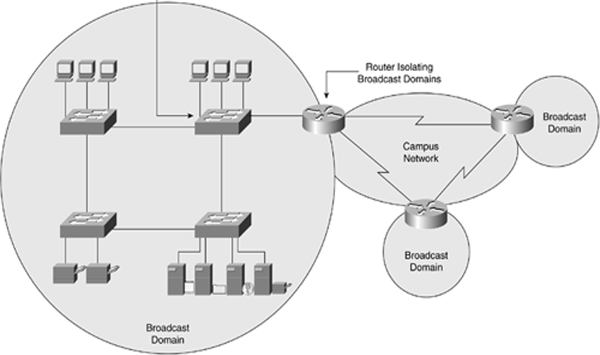
Network segmentation is usually done through some networking device like a router, switch, or a bridge. Each device segments a network differently using collision domains and broadcast domains. A collision domain is a single network connection where a collision will occur if two stations attach to the system and transmit at the same time. A broadcast domain is an area where any broadcasted traffic can be sent to all devices on the same subnet. (Usually separated by routers).
Flat Network
Picture from: etutorials.org
A “flat” network is going to look like the image pictured above. The router, the one with the four arrows on the top, is the one separating the broadcast domains. Look at the left broadcast domain: all servers, networking device’s/resources are all being contained within one broadcast domain. This is a horrible idea! A hacker would be able to access any of the computers within this domain, and they would have easy access to every resource! You just gave that person the keys to the kingdom, and you had no idea. Proper network segmentation could have mitigated this risk. Having different subnets is simple but effective at the same time. A router dedicated to just your essential resources will not be a bad idea, especially if you manage any type of critical infrastructure. Another great thing that proper network segmentation can add is improved monitoring. When looking at the IP ranges, you can quickly tell where traffic is coming from or where you can have any potential problems.
Segmented Network
 Picture from: www.ckd3.com
Picture from: www.ckd3.com
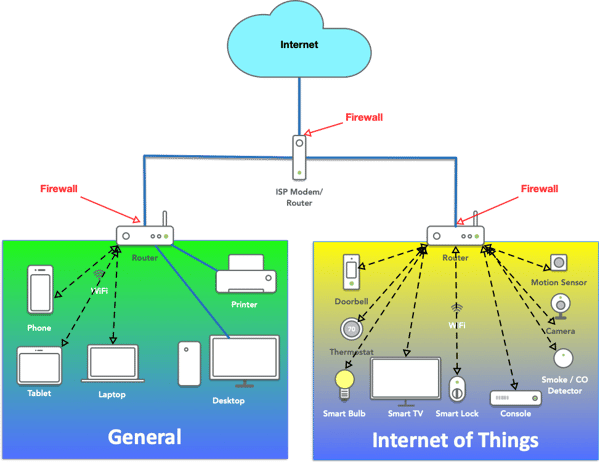
If you compare the last picture to this picture, you can quickly tell there are more broadcast domains. A router is separating the networks here. Employees or guests can log into the proper network. All traffic is going out of the same router to the internet. This is a typical setup in a McDonald’s, Coffee Shop, School, etc. It is simple yet effective in giving everyone internet access while keeping assets safe. Of course, a network this simple can still be hacked, but it will cost a hacker more resources to access all the assets.
Segmentation should also be used for Internet of Things connected devices (smart TVs and refrigerators; fitness devices, smart watches, and other wearables; copy machines, and medical sensors to list a few) because they are often easily hacked.
Beyond security, there are other benefits of segmentation:
- Performance: Since sub-networks are much smaller than the whole network, there are fewer hosts and therefore fewer visitors to each sub-network, resulting in improved performance and reduced traffic congestion.
- Access Control: Stronger access control limits access to specific sub-networks only to people who need it. Sub-networks could be created for specific types of systems handling data of different sensitivity levels.
Conclusion
In conclusion, any proper network needs segmentation. It is easily implemented, can protect your assets, and improve monitoring. It can be done cost-effectively. Threats are rising more than ever, and it is not going to get any better. Any little improvement to that network will be vital in future development. Network segmentation should be used and needs to be implemented on every home and business network to improve system security.
24By7Security specializes in conducting comprehensive Security Risk Assessments, during which we review the network topology. We can provide recommendations on how to improve your network security using various techniques including segmentation and/ or microsegmentation.






-1.jpg)



