HIPAA Compliance That is Less Than 100% is Not Compliance At All
If we have learned anything in covering hundreds of data breaches in recent years, it is that failure to comply completely with federal and industry regulatory requirements renders organizations substantially less secure and therefore substantially more vulnerable. Partial compliance, or incomplete compliance, is not compliance at all—and the proof is in the data breaches. Especially healthcare data breaches.
No One Wants an OCR Investigation
The process healthcare organizations face in the aftermath of a data breach is agonizing, time-consuming, and expensive. Reporting a data breach to the HHS Office for Civil Rights (OCR), and notifying affected individuals that their personal information has been compromised, is just the beginning.
The OCR will conduct an investigation into the circumstances of the breach, paying particular attention to the inevitable HIPAA violations. They will publish detailed findings on the OCR website, proscribe and monitor remediation actions, and in virtually all cases impose a hefty financial penalty on the organization. In many cases, class action lawsuits will be filed as means of achieving compensation for affected individuals and punishing those responsible. Settlements are often in the tens of millions of dollars and are highly publicized. Damage to a healthcare organization’s reputation is incalculable. And you may as well throw that HIPPA-required Privacy Policy out the window, for all the credibility it retains.
A casual attitude about security will come home to roost, there is no doubt, and non-compliance simply doesn’t pay. The healthcare organizations reporting data breaches in the first half of 2023 will learn that lesson in the coming months as the OCR process kicks into gear.
Update: Data Breaches Reported First Half 2023
The numbers are in for reports filed with the Office for Civil Rights between January 1 and June 30, 2023. Data breach reporting requirements are based on when the breach is discovered. Breaches affecting 500 or more individuals must be reported to the OCR within 60 calendar days of discovery, while those under 500 can be reported before the end of the calendar year.
All must be reported in accordance with the HIPAA Data Breach Notification Rule. Reports filed with the OCR between January 1 and June 30, 2023 will include some breaches that were actually discovered in late 2022, assuming everyone played by the rules.
For the six-month period, reports of security incidents affecting 500 or more individuals totaled 315, with more than three-quarters (76%) citing hacking as the cause. In OCR reporting, hacking covers a lot of ground including ransomware attacks and phishing schemes, and no finer breakdown is available. Breached data was located on network servers in 210 of these incidents (67%), which corresponds pretty closely to the prominence of hacks as a cause. In another 57 incidents (18%) the breached data was located in emails and email systems.
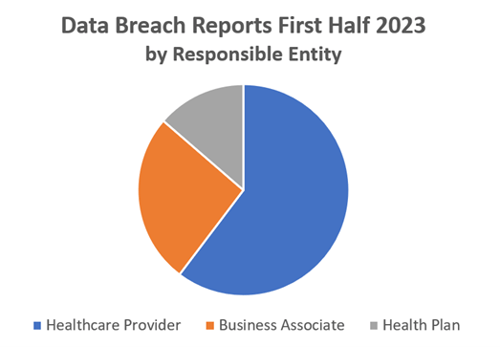
Of the 315 data breaches, the majority were attributed to healthcare providers (60%). While business associates had primary responsibility for 82 incidents (26% of the 315), they were also parties to another 35 incidents. By comparison, health plans or insurers were responsible for just 14% of the reported breaches.
Geographically, California led the nation with 42 breaches reported during the six-month period, followed closely by New York at 36. Massachusetts reported 24 breaches, Texas 21, and Pennsylvania 19. Florida reported 11 breaches.
Data Breaches Can Happen to Any Organization with Incomplete Compliance
As these numbers indicate, data breaches in the healthcare industry run the gamut in terms of geography, type of organization, size of breach, and nature of breach. And data breaches like these can happen to any healthcare organization that has active security vulnerabilities due to being only partially compliant with HIPAA security requirements.
Following are some of the stories behind this year’s data breaches, presented in order of impact size (from 500 to 250,000 individuals). The more massive breaches, such as Managed Care of North America, Cerebral Inc., PharMerica Corporation, and Enzo Clinical Labs, can be reviewed in numerous articles.
Class Action Filed Against Dental Group. On May 12, 2023, Great Expressions Dental Centers in Michigan reported a network hacking incident and began mailing individual notifications to 528 affected individuals. This healthcare provider determined that an unauthorized party had gained system access in February 2023, and may have removed files containing health information including images, personal data, payment information, and prescription and insurance information. In a curious fine point, a notice on their website assures patients that the “electronic medical records system was NOT involved in the incident.” On May 18, a class action lawsuit was filed against ADG LLC, the legal entity doing business as Great Expressions Dental Centers, by a large personal injury firm.
Urgent Care Centers Have Multiple Setbacks. In Georgia, the health data of 2,555 individuals was compromised by unauthorized access to paper and/or film records at Peachtree Immediate Care, according to information reported to the OCR on January 23, 2023. Although research to learn more about this breach bore no fruit, we did learn that Peachtree Immediate Care operates some 60 urgent care clinics for the Emory Healthcare network. And that Peachtree is owned by CRH Healthcare. And that just last month, in June 2023, CRH Healthcare agreed to pay $1.6 million to settle a lawsuit claiming the clinics had charged for non-existent doctor visits during the pandemic. The lawsuit was filed under the federal False Claims Act by the U.S. government and the state of Georgia.

State Agency Employee’s Mistake. On January 11, the Minnesota Department of Human Services, a state-operated health plan, reported an incident of unauthorized access or disclosure through email. A notice on the department’s website explains that the error was committed on November 18, 2022, when a department employee mistakenly emailed copies of billing statements related to 4,307 individuals enrolled in Medical Assistance to an individual client who had requested their own data. According to the notice, the information did not contain any social security numbers, banking information, or credit card numbers, and there is no evidence that this information was actually viewed, downloaded, or misused. The individual who received the billing statements called the department to report the error and agreed to delete the email and its information. On January 11, 2023, a notification was sent to the 4,307 affected individuals.
Law Firm Moves Slowly in Hack Probe. On June 7, 2023, Marshall & Melhorn LLC, a law firm in Toledo, Ohio, reported to the OCR that they had experienced an outage to their network on September 14, 2021 (yes, 2021) caused by a hacker who may have accessed and acquired 9,412 individual’s files. A review to determine the particulars of the hack was completed on March 6, 2023, a year and a half later. The published Notice of Data Event adds that “there is no indication that any data accessed and/or acquired from our system has been misused.” In closing the notice, the firm defends its security program, stating that “Information security is among Marshall Melhorn’s highest priorities, and we have security measures in place to protect information in our care. Upon discovering the incident, we immediately confirmed the security of our systems. As part of our ongoing commitment to the security of information, we reviewed existing security policies and have implemented additional cybersecurity measures to further protect against similar incidents occurring in the future.”
Patient Portal Hacked. On May 12, 2023, a press release on the Illinois.gov news site reported that the State of Illinois Application for Benefits Eligibility System patient portal had been hacked. On the same date, the 50,839 affected individuals, the Office of the Illinois Attorney General, and the OCR were notified of the incident. The portal provides visibility to patient case histories and benefit details including name, address, phone number, date of birth, recipient identification number, individual ID, case ID, social security number, benefits applied for and received, income information, and supporting documentation. Upon discovering suspicious user accounts in the system 90 days earlier, on March 13, 2023, the state installed new software to neutralize the unauthorized activity.
 Confirmed Healthcare Ransomware. A press release posted on the Florida Medical Clinic website on March 10, 2023, noted that suspicious activity was detected in the computer network on January 9, 2023, and confirmed that a ransomware attack had occurred. The forensic investigation determined that certain files containing personal information were accessed, but the electronic health record systems remained secure. “There is no evidence that any of the accessed information has been improperly used,” states the release, adding “Florida Medical Clinic has obtained evidence that all of the stolen files were permanently deleted.” The clinic determined that 94,132 files were exposed, but that 95% contained only an individual’s name and no other personally identifiable information, and only 115 social security numbers were compromised. The press release said the organization is “in the process of notifying patients whose information was involved.”
Confirmed Healthcare Ransomware. A press release posted on the Florida Medical Clinic website on March 10, 2023, noted that suspicious activity was detected in the computer network on January 9, 2023, and confirmed that a ransomware attack had occurred. The forensic investigation determined that certain files containing personal information were accessed, but the electronic health record systems remained secure. “There is no evidence that any of the accessed information has been improperly used,” states the release, adding “Florida Medical Clinic has obtained evidence that all of the stolen files were permanently deleted.” The clinic determined that 94,132 files were exposed, but that 95% contained only an individual’s name and no other personally identifiable information, and only 115 social security numbers were compromised. The press release said the organization is “in the process of notifying patients whose information was involved.”
The Lawyers are Circling. According to a Notice of Data Event posted on the Albany ENT & Allergy Services website, the New York healthcare provider discovered evidence that, between March 23 and April 4, 2023, an unauthorized third party may have accessed systems storing sensitive personal and health information. An extensive review confirmed on May 2 that the exposed records contained certain employee and patient information. On May 25, the healthcare provider reported the breach to the OCR and state and federal authorities and also began notifying the 224,486 patients whose information was compromised. Various attorneys and personal injury firms are monitoring the situation and offering legal services on their websites.
Summary
Regardless of the size or nature of a data breach, or the type and location of the organization responsible for it, all breaches must be reported to the OCR as specified in the HIPAA Data Breach Notification Rule. The Rule includes numerous requirements which all healthcare organizations should be familiar with, including reporting timetables.
Breaches affecting 500 or more individuals are published on the OCR website, while those affecting fewer than 500 are not published. As we have seen, the published breaches tend to attract a lot of unwelcome attention, not only from the OCR but also from personal injury law firms. Healthcare providers, business associates, and health plans can avoid becoming easy targets for cybercriminals—and avoid the high cost of data breaches—by ensuring their HIPAA programs are up to date and in complete compliance with all requirements.









