Experience has made us all true believers in cybersecurity and solid information security programs. We understand that a security program is not a one-time undertaking. It demands ongoing maintenance and improvement. And that improvement is the result of corrective actions.
Corrective actions are methodical steps taken by an organization to correct errors, close gaps, or resolve other problems that have been found in the organization’s security program, and for which the underlying or root cause has also been identified.
Who Requires Corrective Actions
Various regulations and security frameworks have requirements for corrective actions to improve security or achieve compliance. In this post, we’ll explore the Department of Health and Human Services (HHS) Office for Civil Rights (OCR) requirements for corrective actions to be taken by healthcare providers and business associates who violate the HIPAA Security or Privacy Rules.
We will also review the NIST security framework, and specifically the corrective action guidance presented in the NIST Special Publication 800-100 Information Security Handbook.
NIST Corrective Action Guidance
The NIST SP 800-100 Information Security Handbook is 178 pages organized into 14 chapters with two appendices. It is an extensive set of recommendations from the National Institute of Standards and Technology, designed for managers, to guide them in managing information security in their companies.
Chapters range from information security governance, awareness and training, capital investment, and security planning to risk management, incident response, IT contingency planning, and configuration management.
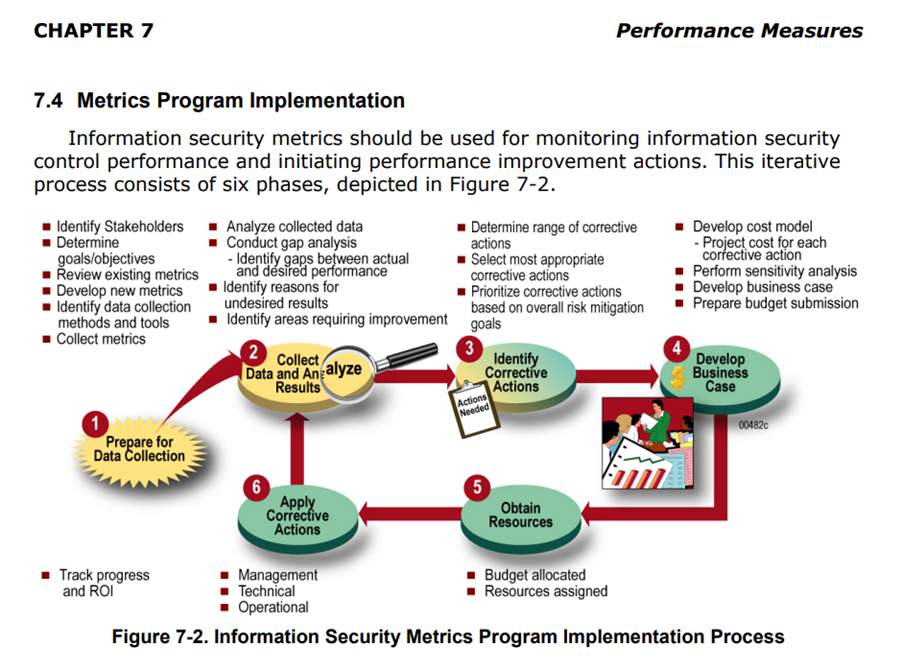
Chapter 7, titled Performance Measures, addresses the role of corrective actions in improving security performance. And more specifically, the use of information security metrics as an aid in identifying and applying corrective actions to improve security performance. To paraphrase the caption in this diagram from the handbook, information security metrics should be used for monitoring the performance of information security controls, and for initiating corrective actions that will improve performance.
The NIST Process of Security Improvement
In the NIST Handbook, security improvement is illustrated as a continuous and iterative process with six phases. Phase 1 involves preparation.
Phase 2 requires the collection of information so that an organization can identify gaps between its desired results and actual results. The gap analysis establishes the foundation for Phase 3, which calls for corrective actions to be identified, chosen, and prioritized to address the gaps found.
Phase 4 is a well-timed reality check. At this point, the organization estimates the costs of each corrective action, prepares a total budget, and develops a business case for the corrective actions.
In Phase 5, the organization allocates the budget and assigns resources for implementation. And in Phase 6, the corrective actions are applied to the systems, processes, policies, procedures, and other elements of the security program. There will be management, technical, and operational actions to be implemented, all of which were prioritized in Phase 3. In addition, during this extended implementation phase, the organization monitors and reports its progress, and tracks the return on investment or ROI.
The NIST Information Security Handbook, Chapter 7, explains that the “iterative nature of the cycle ensures that the progress is monitored, and the corrective actions are affecting system security control implementation in an intended way.” It provides general examples of corrective actions, which may include “changing system configurations; training security staff, system administrator staff, or regular users; purchasing security tools; changing system architecture; establishing new processes and procedures; and updating security policies.”
Clearly, NIST places great importance on an organization’s ability to identify and implement actions that correct errors, close gaps, or resolve other problems in its security program.
However, while in the NIST model corrective actions are strongly recommended, the corrective actions imposed by the HHS OCR are mandatory.
OCR Corrective Action Requirements
 The Office for Civil Rights (OCR) is responsible for enforcing HIPAA requirements, including both the Security Rule and Privacy Rule, and the Privacy Rule’s requirement that patients be able to access their health records in a timely and affordable manner.
The Office for Civil Rights (OCR) is responsible for enforcing HIPAA requirements, including both the Security Rule and Privacy Rule, and the Privacy Rule’s requirement that patients be able to access their health records in a timely and affordable manner.
The OCR is responsible for investigating complaints of HIPAA violations, which may be submitted to the HHS website.
In addition, the OCR has the power to settle HIPAA violations. Settlements usually include fines or financial penalties payable by the violator, along with the mandatory implementation of corrective action plans to address the violations.
In this context, a corrective action plan is an aggressive enforcement action the OCR takes when it finds a HIPAA-covered entity or business associate in violation of HIPAA requirements. The purpose of the plan is to correct the underlying compliance issues that led to the HIPAA violation(s). Typically, violators are monitored for three years to assure their progress in implementing the required corrective actions.
OCR Settlements in 2021
In 2021, the OCR settled 11 Patient Right of Access violations and penalized the violators for a total of $777,150. Since 2019, when it began actively enforcing the HIPAA Privacy Rule’s Patient Right of Access requirement, the OCR has settled 25 such violations.
Also in 2021, the OCR settled two violations of the HIPAA Security Rule, one for a $5.1 million penalty and the other for $25,000.
In the first settlement, a $5.1 million fine was imposed after a 16-month data breach exposed the PHI of more than 9.3 million insured individuals without permission. In addition to paying the hefty fine, the violator was required to implement a series of detailed corrective actions. The actions specifically addressed four key failures in this large insurance firm’s information security program. These included (1) failure to conduct an enterprise-wide risk analysis, (2) failure to implement a risk management plan, (3) failure to conduct an information system activity review, and (4) failure to implement access controls. The OCR continues to monitor the company’s progress toward compliance.
In the second settlement, a fine of $25,000 was imposed on a small medical specialty group. It was accompanied by a detailed set of corrective actions required to address failures in policies, procedures, and employee training, as well as the absence of a risk management plan and security risk assessment. Again, the OCR continues to monitor the organization’s progress in implementing the assigned corrective actions.
Five Examples of OCR Corrective Actions
The corrective actions imposed by the OCR are consistently detailed, comprehensive, and mandatory. Following are examples of the nature of some of the most common corrective actions. (Actual organizations’ names have been replaced with the word Violator.)
- The Violator shall develop, maintain, and/or revise, as necessary, its written access policies and procedures to comply with the Federal standards that govern the privacy of individually identifiable health information (45 C.F.R. Part 160 and Subparts A and E of Part 164, the “Privacy Rule”).
- The Violator shall assess, update, and revise, as necessary, the policies and procedures at least annually or as needed, and shall provide such revised policies and procedures to HHS for review and approval.
- The Violator shall provide to HHS, for review and approval, a copy of the training materials it will use to train its workforce within sixty (60) days of the approval of its policies and procedures.
- The Violator shall provide training for each workforce member within ninety (90) days of HHS approval of the training materials and annually thereafter. The Violator shall also provide such training to each new workforce member within thirty (30) days of their beginning of service.
- During the compliance term, the Violator, upon receiving information that a workforce member may have failed to comply with the policies and procedures developed, shall promptly investigate this matter. If it determines, after review and investigation, that a workforce member has failed to comply with these policies and procedures, the Violator shall notify HHS of this reportable event, in writing, within thirty (30) days.
The OCR has also imposed corrective actions for a wide range of other topics and security failures. These can be found on the HHS OCR website.
Summary
The HHS Office for Civil Rights requires corrective actions by healthcare organizations that violate HIPAA Security and Privacy Rules, to bring them into compliance. Corrective actions are also recommended, for slightly different reasons, by the National Institute of Standards and Technology in its NIST SP 800-100 Information Security Handbook.
Regardless of their purpose, a corrective action plan is a useful aid in prioritizing and implementing corrective actions. Such a plan should be clearly actionable and should assign responsibilities and completion dates for each of the required actions. Having a corrective action plan, and working actively to implement it, is vital to maintaining a solid information security program. As a security best practice, a corrective action plan is good business for your organization and reassurance for your patients, customers, and other stakeholders.









