Phishing Emails Sent by QakBot Used Malicious Links to Install Ransomware in 700,000 Victim Computers
QakBot has been wreaking cyber havoc since at least 2008 when it emerged as a major tool of cybercriminals targeting the financial industry. As a banking Trojan, QakBot was able to steal credentials in order to access bank accounts, primarily using phishing emails to deliver malicious links and attachments. When clicked by unsuspecting users, the links installed malware on the victim's computers which then infiltrated the entire victim network.
The QakBot malware botnet is a textbook example of an evolutionary phishing campaign delivering malware, including ransomware, to extort financial payoffs from victim organizations. Sometimes known as Qbot or Pinkslipbot, QakBot has long been a favorite of numerous ransomware groups including REvil, Conti, ProLock, and Egregor to name a few.
QakBot conducted its criminal activity for 15 years, extorting at least $8.6 million in illicit cryptocurrency profits from victims and resulting in hundreds of millions of dollars in damages worldwide.
QakBot Malware Botnet Disabled by U.S. DOJ and Partners
Some of the best hackers in the world operate for good rather than evil, helping cybercrime-fighting organizations do their jobs more effectively. Very recently, a powerful collaboration among law enforcement and cybersecurity experts in seven countries resulted in the landmark dissolution of the QakBot botnet.
On August 29, 2023, the U.S. Department of Justice announced the successful completion of “a multinational operation involving actions in the United States, France, Germany, the Netherlands, United Kingdom, Romania, and Latvia to disrupt the botnet and malware known as QakBot and take down its infrastructure. The QakBot malicious code is being deleted from victim computers, preventing it from doing any more harm.”
Score another one for the good guys!
Within the Department of Justice, the Federal Bureau of Investigation is the lead federal agency responsible for investigating cyberattacks. Their role includes collecting and sharing intelligence, engaging with victims of cybercrime, working to identify malicious and fraudulent cyber activities, and prosecuting those who commit them. The FBI also publishes alerts about ransomware attacks and other types of cybercrime that may be ramping up, in order to help U.S. businesses harden their security defenses.
According to the DOJ press release, the QakBot takedown constitutes “the largest U.S.-led financial and technical disruption of a botnet infrastructure leveraged by cybercriminals to commit ransomware, financial fraud, and other cyber-enabled criminal activity.”
How the QakBot Takedown Occurred
From its origins as a banking Trojan, QakBot had evolved over the years into a “multi-purpose botnet and malware variant” that provided cybercriminals and ransomware gangs with an extensive array of capabilities, according to a bulletin from the Cybersecurity and Infrastructure Security Agency (CISA), which works frequently with the FBI.
These additional QakBot functions included “performing reconnaissance, engaging in lateral movement, gathering and exfiltrating data, and delivering other malicious payloads, including ransomware, on affected devices.”
In summarizing the recent takedown, Department of Justice Attorney General Merrick Garland credited the DOJ’s international partners with invaluable assistance, including:
- Hacking the QakBot malware botnet infrastructure,
- Moving aggressively to uninstall the malware from victim computers in the U.S. and globally, and
- Seizing $8.6 million USD in cryptocurrency ransoms extorted from victims.
As part of the takedown, the FBI was able to gain access to QakBot infrastructure and identify more than 700,000 computers worldwide, including some 200,000 in the U.S., that appeared to have been infected. QakBot botnet traffic was then redirected to servers controlled by the FBI.
The servers instructed infected computers to download a specific file. The file had been created by law enforcement for the express purpose of uninstalling QakBot malware. The uninstaller program was designed to release the victim's computer from the botnet, thereby preventing any further installation of malware through QakBot.
In the DOJ press release, FBI Director Christopher Wray credited the FBI with leading a joint, worldwide “sequenced operation that crippled one of the longest-running cybercriminal botnets.”
“With our federal and international partners, we will continue to systematically target every part of cybercriminal organizations, their facilitators, and their money,” he added, “including by disrupting and dismantling their ability to use illicit infrastructure to attack us.”
Actions and Resources for Victims of QakBot Malware
Several organizations are assisting the FBI in notifying QakBot victims of the botnet takedown and potential remediation and restitution actions. These include the Cybersecurity and Infrastructure Security Agency (CISA), Microsoft Digital Crimes Unit, National Cyber Forensics and Training Alliance, and Have I Been Pwned, among others.
The FBI and the Dutch National Police have identified numerous account credentials compromised by QakBot, and the FBI has provided those credentials to the website Have I Been Pwned. This website is a free resource enabling individuals to quickly determine whether their access credentials have been compromised.
In addition to these specific resources, the FBI and CISA frequently collaborate to publish advisories regarding persistent threats and trends in cybercriminal activity.
The current CISA bulletin provides information about the QakBot infrastructure and offers potential victims several indicators of compromise, as excerpted below.
Modular Structure a Key to QakBot Success
 The flexible infrastructure of the QakBot malware botnet enabled various malicious features, including process and web injection, victim network enumeration and credential stealing, and the delivery of follow-on payloads such as Cobalt Strike, Brute Ratel, and other malware.
The flexible infrastructure of the QakBot malware botnet enabled various malicious features, including process and web injection, victim network enumeration and credential stealing, and the delivery of follow-on payloads such as Cobalt Strike, Brute Ratel, and other malware.
QakBot infections are particularly known to precede the deployment of human-operated ransomware, including Conti, ProLock, Egregor, REvil, MegaCortex, Black Basta, Royal, and PwndLocker.
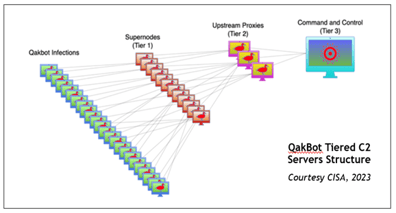
Historically, QakBot’s C2 infrastructure relied heavily on using hosting providers, who lease servers to malicious threat actors, ignore abuse complaints, and do not cooperate with law enforcement. At any given time, thousands of victim computers running Microsoft Windows were infected with QakBot, which was controlled through three tiers of C2 servers. Tier 1 supernodes relayed communications to the Tier 2 C2 servers, serving as proxies to conceal the main C2 server, while the Tier 3 server controlled all of the bots.
The first tier of C2 servers includes a subset of thousands of bots selected by QakBot administrators, which are promoted to Tier 1 supernodes by downloading an additional software module. As of mid-June 2023, 853 active supernodes had been identified in 63 countries. Supernodes have been observed to change frequently, which further assists QakBot in evading detection.
Indicators of Compromise by QakBot Malware Botnet
According to the CISA bulletin, the FBI observed the following tactics, techniques, and procedures (TTP) in association with QakBot infections:
- QakBot sets up persistence via the Registry Run Key as needed. It will delete this key when running and set it back up before the computer restarts. HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run\<random_string>
- QakBot will also write its binary back to disk to maintain persistence in the following folder. C:\Users\<user>\AppData\Roaming\Microsoft\<random_string>\
- QakBot will write an encrypted registry configuration detailing information about the bot to the following registry key. HKEY_CURRENT_USER\Software\Microsoft\<random_string>
The CISA bulletin also lists IP addresses identified as having obtained access to victim computers and encourages organizations to review any connections with those addresses, which could potentially indicate a QakBot and/or follow-on malware infection. The information and resources are available now to organizations and their cybersecurity teams.
Summary
For 15 years the notorious QakBot malware botnet has operated with impunity. It is responsible for infecting at least 700,000 computers worldwide, extorting millions of dollars in ransom payments from hapless victims, and creating hundreds of millions of dollars in damages in the U.S. and internationally. Law enforcement and cybersecurity teams working in concert across seven countries were successful in disrupting the botnet this summer and taking down its infrastructure to prevent further criminal activity from QakBot.
Detailed information and resources are available now to assist potential QakBot victims in verifying compromised computers and remediating damages. Our white hats are off to the teams in these seven countries who worked together, across borders and cultures, to bring down this malicious ransomware botnet and make the internet just a little bit safer for all of us.
Do your part by training employees to recognize phishing schemes, which frequently lead to malware installations on company networks and the extortion of ransoms that support ongoing cybercriminal activity.



.png)






