Medical devices, just like any other Internet of Things (IoT) object, are prone to hackers. These hacks can get dangerous quickly— security risks with medical devices become patient safety issues, as while medical devices carry patient data that needs to be protected according to HIPAA laws, these instruments also perform critical functions that save lives.
Weaknesses that augment the risk of a potential breach include the fact that medical devices tend to be five to six years old by the time they are even put in use at hospitals, after which they are operating for another fifteen years. These devices are the most prone to security breaches, as they are not built with future tech advancements in mind.
On top of this, many hospitals have not updated or patched their software or medical devices until something has already gone wrong. After the WannaCry ransomware attack in May of 2017, Windows released patches for operating systems as old as Windows XP, yet many hospitals are slow to download the patch, and some did not download it at all. Hospitals, along with medical device manufacturers, are testing and deploying the patches across the millions of medical devices.
Due to the increasing connectivity of medical devices, cyberattacks have been steadily increasing over the past few years.
Here are some examples of alarming events that have occurred with medical devices:
- In 2014, researchers alerted the Department of Homeland Security that certain models of the Hospira infusion pump could be digitally manipulated. A year later, the FDA issued an advisory discouraging hospitals from using the pump; however, it is still in use in many medical settings. Even if a security risk is detected, the device is still needed for patient health.
- Years later, in September 2017, eight security vulnerabilities were found in the Medfusion 4000 Wireless Syringe Infusion Pump, the worst of which had a Common Vulnerability Scoring System (CVSS) score of a 9.8 out of 10.
- In 2016, researchers from the University of Leuven in Belgium and the University of Birmingham in England evaluated ten types of implantable cardioverter defibrillators (ICDs) and gained the ability to turn off the devices, deliver fatal shocks, and access protected health information (PHI). Not only could they drain the battery and change the device’s operation, if the researchers had used slightly more advanced or sophisticated equipment, they would have been able to interfere with the devices from hundreds of meters away.
- In late 2016, over 100,000 users of insulin pumps were notified of a security vulnerability where an unauthorized third party could alter a patient’s insulin dosage.
- In May 2017, NSA hacking tools believed to have been stolen by North Korea were used to infect MRI systems in US hospitals. Although this hack did not directly threaten patient safety, the machines ceased functionality for an extended period of time, increasing the need for hospital resources and causing critical delays.
- In August of 2017, the FDA recalled 465,000 implanted cardiac pacemakers due to a vulnerability where unauthorized users could modify the pacemaker’s programming.
After all of these life-threatening hacks, the FDA has provided updated recommendations with a revision of NIST’s 2014 Framework for Improving Critical Infrastructure Cybersecurity.
Cybersecurity risk assessments can facilitate calculating the vulnerability of these medical devices. One form of this is penetration testing, where security engineers target identified or unidentified vulnerabilities in code and report the product response. Other types of risk assessments can include malware testing, binary/byte code analysis, static code analysis, fuzz testing, and security controls testing.
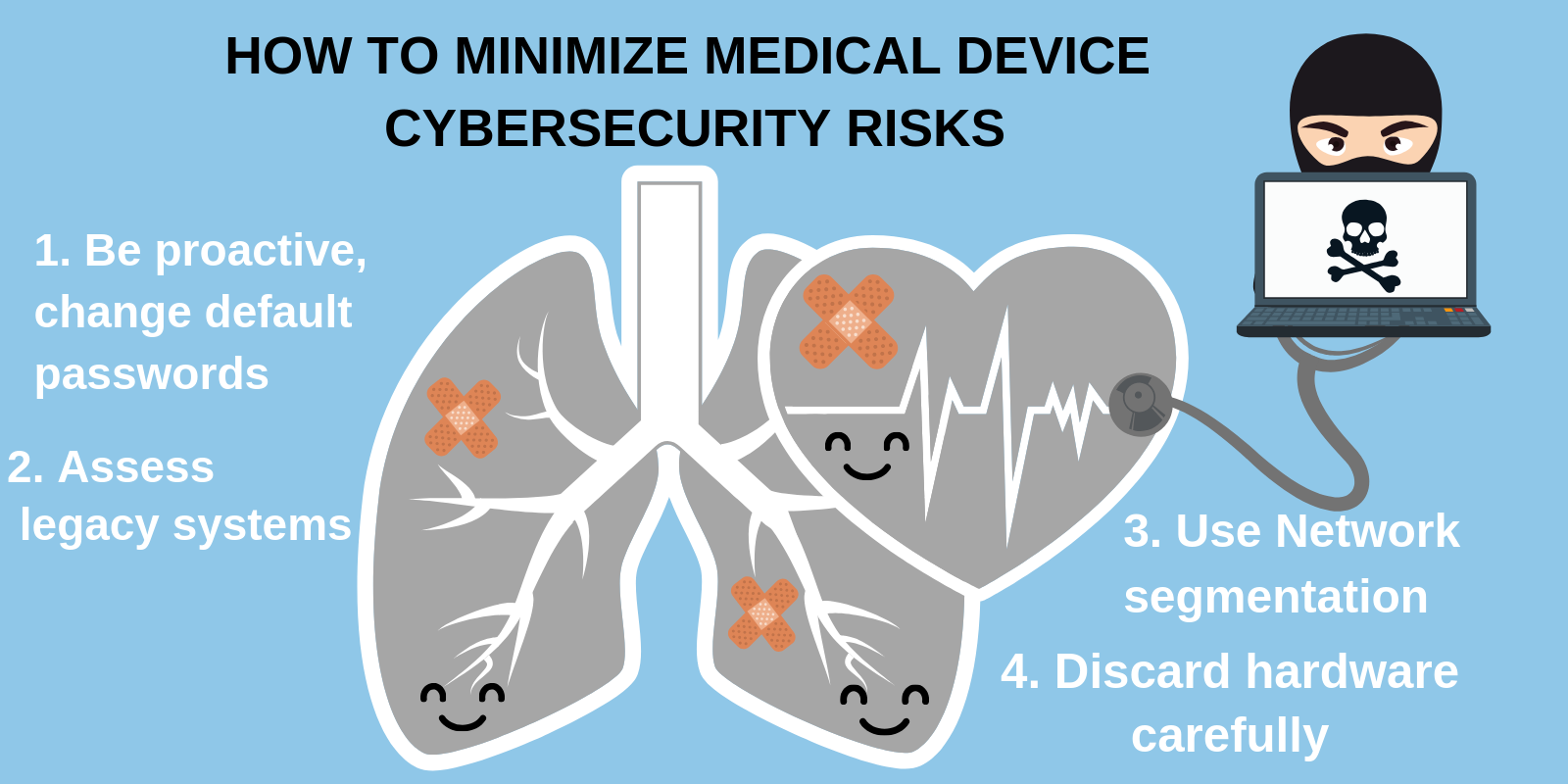
There are four key steps that a healthcare organization using these medical IoT devices can take to protect patient data and the devices themselves:
- Hospitals should use proactive approaches to hacking threats rather than waiting for something to go wrong; always change default passwords and factory settings.
- Healthcare companies should also assess their legacy systems and any outdated hardware; systems that are outdated are not only prone to hackers but do not integrate with newer devices perfectly. This lack of interoperability leads to more security gaps, which creates a cycle of weakness.
- Hospitals should isolate the medical devices that cannot be patched on a separate network so that hackers do not have access to the medical devices, in a process known as network segmentation.
- To discard hardware, the disposal should be done domestically, include complete data destruction, and be coordinated so that data cannot be recreated from abandoned devices.
Medical devices are not removed from the realm of hackable devices and should be treated as such. In fact, they should be treated with even more caution and care. If these devices are infected by hackers, both safety and privacy are at risk. Hospitals have an obligation to ensure the highest degree of security controls within medical devices they use. While the FDA may issue guidelines or recommendations with caution, as they put patient well-being above all, government agencies should still do everything in their power to make cybersecurity recommendations for medical devices enforceable and part of the law.