During the OCR/ NIST Safeguarding Health Information: Building Assurance through HIPAA Security conference in September 2017, Linda Sanchez from the Office for Civil Rights (OCR) provided an update on the results of the OCR Phase 2 HIPAA desk audits conducted. She informed us that the goals of these OCR Phase 2 desk audits were to support improved compliance from the industry, identify best practices, uncover risks and vulnerabilities, detect areas needing technical assistance from OCR, and to encourage consistent attention to compliance. These OCR Phase 2 HIPAA desk audits were intended to be non-punitive, but OCR reserves the right to open up the compliance review to punitive actions if needed.
The first round consisted of on-site reviews of about 115 entities. The second round comprised of desk audits on a smaller scale. Desk audits of covered entities are complete, while desk audits of business associates are underway as of the date of the conference. Business associates were selected from a pool of 20000 business associates identified by audited covered entities.
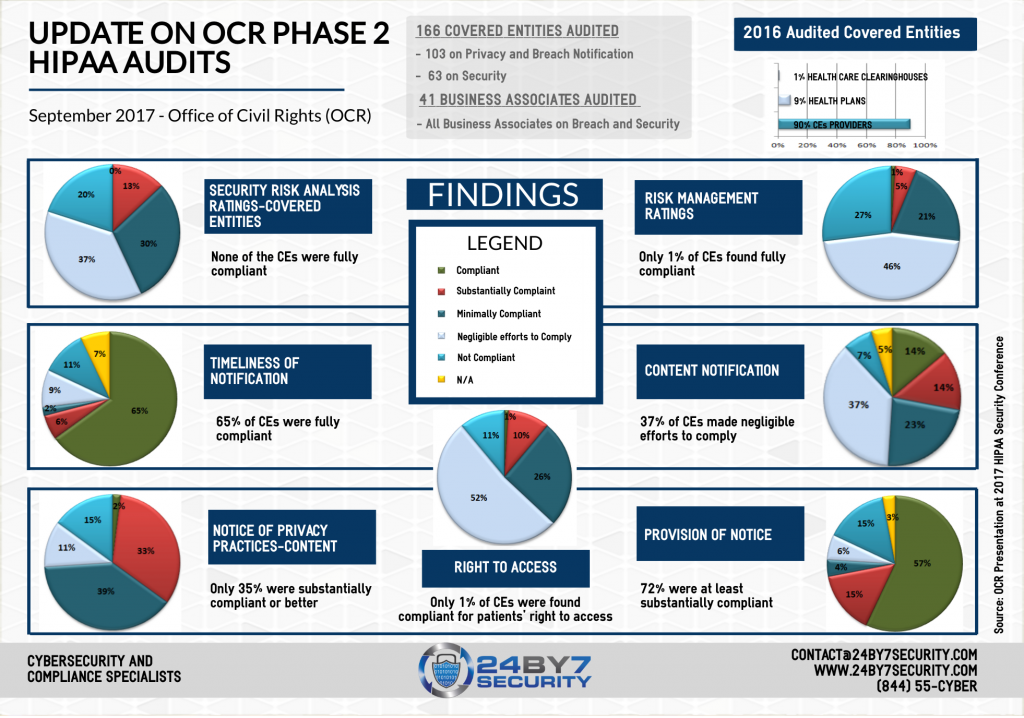
Out of the 166 covered entities audited, 103 were audited for privacy and breach notification while security was the focus for the other 63. 41 business associates were selected to be audited on both security and breach notification. Most of the audited covered entities were small physician practices from all over the country. As Health and Human Services (HHS) Director, Roger Severino said at the same conference, “OCR recognizes small providers as integral to our healthcare system”. They have the same HIPAA responsibilities as larger institutions. He also said that “providers should not assume that just because they are small, OCR is not looking. “
Some key components of the OCR HIPAA audit included the following points:
- Does the provider’s website have a notice of privacy practices on it, or did the website link to it
- Breach notification content and timeliness
- Patients’ right of access to information, and did the Notice of Privacy Practices cover this point
- How is the entity’s overall risk management program, including policies and procedures, risk assessments, documentation of risks, risk remediation
- Copies of the current and prior risk assessment were requested and reviewed
- Evidence was requested for all the controls being audited, and in some cases, evidence was requested for up to 6 years prior.
The most major issues found were related to risk analysis, the overall risk management process, and patients’ right to privacy. Very few entities were found fully compliant in these areas. About half of the covered entities that were audited for security rule compliance, were found to actually be seriously non-compliant. Entities who did not provide proper evidence or who were found non-compliant may remain in the compliance review pool for future actions. The goal of OCR is to have on-site audits follow these desk audits.
During the 2-day conference, multiple speakers from various Federal agencies stressed how important it is for covered entities and business associates to conduct an annual HIPAA risk assessment or risk analysis. This step is the first major step of any risk management program and many entities tend to overlook it. Covered entities and business associates must recognize that Cybersecurity issues can impact patient care. Risk analysis provides an entity with a baseline on its security posture and results in action items to mitigate or remediate risks found in the assessment. Conducting an annual risk assessment is not only a compliance requirement but is also the first step in any risk management program. Please visit our services page to read more about 24By7Security risk assessments. Click here to see OCR's presentation on this subject.
By Rema N. Deo.



.png)


