Yes, they all ask for a risk assessment. If you, as a healthcare covered entity or a healthcare business associate, ever get audited by the Office for Civil Rights (OCR), or if you have already had the pleasure of being audited, you will know that one of the first things OCR will ask you for is a documented risk assessment or risk analysis (these terms are used interchangeably in this post). A documented risk assessment is also a requirement for meaningful use certification and reimbursement. If you run a compliant HIPAA Security Risk Analysis (SRA) to satisfy the Risk Analysis Requirements under the OCR-HITECH Act, it will satisfy the requirement for Meaningful Use Security Risk Assessment (SRA).
A risk assessment is the backbone of any organization’s HIPAA compliance program. During the September 2017 annual OCR/ NIST HIPAA Security conference, several speakers reinforced the need for a thorough risk analysis to establish the baseline for your security and compliance program. Russ Branzell, President and CEO of CHIME, indicated that one of the top priorities for healthcare security should be to implement a continuous program of risk assessment and management. Representatives from the National Institute of Standards and Technology (NIST) talked about how the NIST Cybersecurity Framework can help guide entities in performing a comprehensive risk assessment. Iliana Peters from OCR emphasized that evidence of a documented risk assessment is key to be able to discuss options with OCR in the event of a breach. She also explained that there is no model risk analysis. Every enterprise is different. A risk analysis for a small dentist’s practice is going to look different from one for a large health plan. The most important first step is to know where your data is.
A risk assessment or risk analysis helps you understand what your organization’s security level is – it sets a baseline. Once you have the baseline, you would work on remediation action items step by step. You would also repeat the risk assessment, at a minimum, on an annual basis to measure your progress and re-evaluate your security posture. In the panel on medical devices, panelists also reminded us that risk analysis and risk management should apply to all assets – including medical devices and the internet of things. Any asset that contains ePHI, systems and devices should be part of the risk assessment. Look at confidentiality, integrity and availability of data – and how it may be impacted if a device is breached and data is altered or stolen. Device penetration testing should be part of the development effort for the device. We need to understand what the clinical vulnerabilities are in the devices - what are the implications to patient care?
The conference had a panel discussion on reducing risk for small providers. Panelists highlighted that small practices must conduct comprehensive HIPAA security risk assessments. The lack of an assessment is the leading cause of failing a CMS meaningful use audit. If the practice does not have available resources, they could contract with a qualified consultant to conduct the risk assessment and help create a health Cybersecurity culture in the practice.
Marylynn Stowers and Jonathan Litchman from the Providence Group effectively summarized the concept with the words “ASSESS, MONITOR, RESPOND” – this is all part of your risk framework. A risk framework establishes the context and sets perspective on how the organization is going to manage risk. A good risk framework produces a comprehensive risk management strategy.
Linda Sanches from OCR concluded the conference with an update on OCR’s Phase 2 HIPAA desk audits, which revealed how poorly entities did on some key areas of compliance. Read our blog post on OCR Phase 2 HIPAA desk audits for more details.
Cybersecurity issues can impact patient care; in fact they have the potential to cause catastrophic patient care problems. Stay ahead of the game by conducting your annual risk assessment and working on your remediation plan.
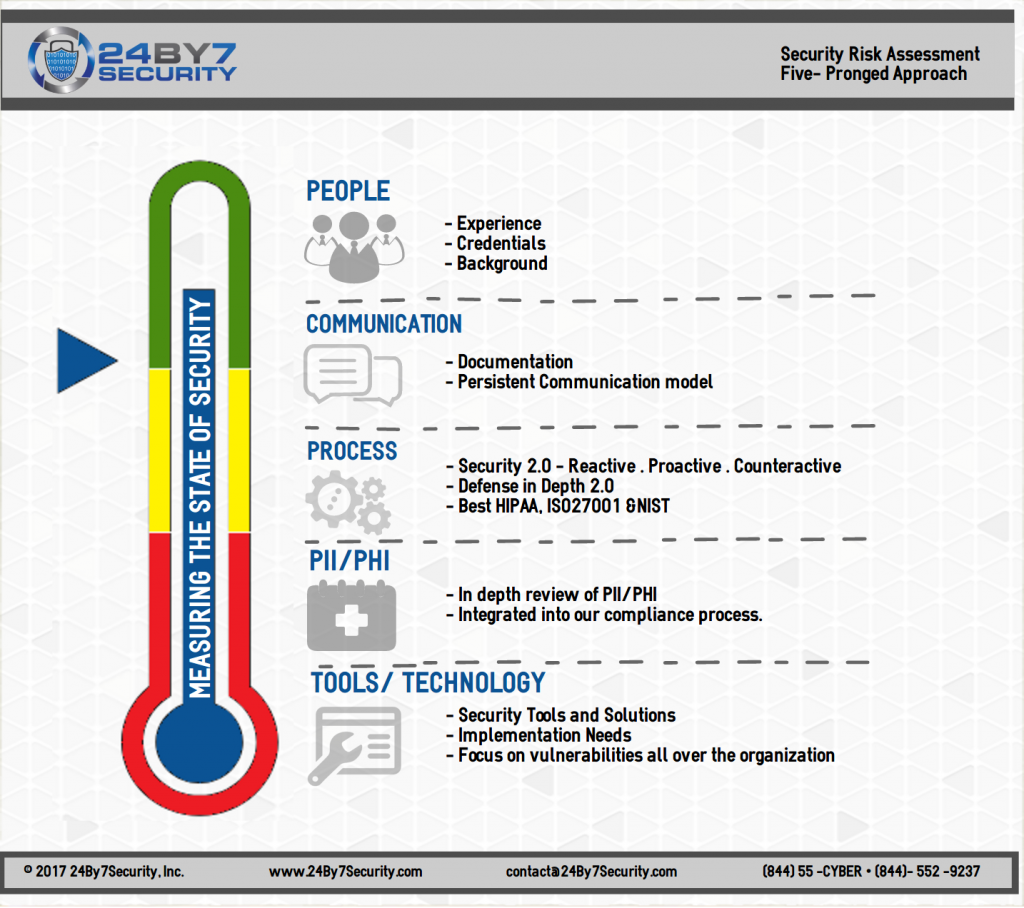
They all ask for a risk assessment. 24By7Security has a five-pronged approach for conducting a risk assessment. This approach comprises of People, Communication, Process, PII/ PHI, and Tools, as outlined in the attached infographic. It is a 360-degree view towards measuring the state of security for your enterprise. For more details please visit our Security Risk Assessment page.
By Rema N. Deo.