Tallahassee Memorial data breach another upset for healthcare; actions your hospital can take now
 Tallahassee Memorial Healthcare is a 772-bed acute care facility serving a 21-county area in northern Florida and southern Georgia. The private, not-for-profit community healthcare system was founded in 1948.
Tallahassee Memorial Healthcare is a 772-bed acute care facility serving a 21-county area in northern Florida and southern Georgia. The private, not-for-profit community healthcare system was founded in 1948.
A suspected ransomware attack brought the venerable organization to its knees the night of Thursday, February 2, 2023. For nearly two weeks after, the hospital relied on paper documentation as its systems remained offline. It was finally brought back online in a controlled fashion on February 15, 2023.
Within days of the attack, the Jacksonville office of the Federal Bureau of Investigation was engaged to aid in the investigation. The hospital created a special webpage to deliver almost daily updates about the security incident, although the source and cause are still undisclosed. Among cybersecurity experts, a ransomware attack is widely suspected due to descriptions of the symptoms.
Ransomware was responsible for the data breach at Lehigh Valley Health Network, also in February 2023. And in October 2022, a ransomware attack caused a month-long network outage at CommonSpirit Health that has cost $150 million to date.
How Ransomware Works
Ransomware is a common healthcare cybercrime that remains popular among cybercriminals for its profitability. Ransomware typically begins with a phishing expedition into an organization, such as a healthcare system. The scheme lures unsuspecting employees into revealing access credentials or other information that the cybercriminals can use to enter the organization’s network or data systems. Once inside, the cybercriminals encrypt the data, rendering it inaccessible and therefore unusable to company employees.
This is the point at which organizations often revert to using manual systems while either (1) attempting to negotiate with the cybercriminals to release their data, or (2) activate the latest data backup performed and stored by the organization. When no useful backup is available, organizations often decide to pay the ransom demanded by the cybercriminals, who then decrypt the data so the organization can restore its systems and return to normal operations. Cybercriminals have been known to request second payments in order to keep the stolen data off the dark web and out of reach of other cybercriminals.
The FBI discourages payments to cybercriminals—but for hospitals without current data backups, there may be no other option.
Data Breach Notification Requirements
Like all healthcare organizations who suffer data breaches, Tallahassee Memorial Healthcare must report details to the HHS Office for Civil Rights. The HIPAA Breach Notification Rule includes the following basic requirements:
- If an organization experiences a data breach that potentially exposes or compromises unsecured (i.e., unencrypted) ePHI, all affected individuals must be notified as soon as possible.
- If the breach affects 500 or more individuals, the HHS OCR must be notified within 60 days of the breach discovery.
- Breaches affecting fewer than 500 can be reported to HHS within the year in which they occur.
Additional details about the Tallahassee Memorial data breach will become available after their report is filed with the OCR and will also be enumerated in the OCR press release.
The High Cost of Healthcare Data Breaches
 According to the 2022 Cost of a Data Breach Report published annually by IBM Security, the average cost of a healthcare data breach now exceeds $10 million, up from $9.2 million in 2021. The healthcare breach average cost is 80% higher than the global average cost. For 12 consecutive years, healthcare has led all other industries in the sheer number of data breaches, according to the report.
According to the 2022 Cost of a Data Breach Report published annually by IBM Security, the average cost of a healthcare data breach now exceeds $10 million, up from $9.2 million in 2021. The healthcare breach average cost is 80% higher than the global average cost. For 12 consecutive years, healthcare has led all other industries in the sheer number of data breaches, according to the report.
Contributing to the overall cost of a data breach are victim and other notifications, system recovery actions, network downtime, operational downtime, reputational damage, rebranding costs, lost business, ransom payments, civil and legal financial settlements, OCR penalties, and other costs.
The HHS Office for Civil Rights is charged with enforcing HIPAA regulations including the Security Rule, Privacy Rule, and Breach Notification Rule. Already in 2023, OCR has concluded a settlement with Banner Health, a Phoenix-based non-profit health system that employs 50,000 across 30 hospitals. Banner Health suffered a hack in 2016 that resulted in disclosure of the electronic protected health information (ePHI) of more than 2.8 million individuals. This year, Banner Health paid $1,250,000 to the OCR and will implement a corrective action plan to resolve their violations in order to protect the security of ePHI.
The corrective action plan specifically addresses these four failures at Banner Health:
- Lack of an analysis to determine risks and vulnerabilities to ePHI across the organization,
- Insufficient monitoring of its health information systems’ activity to protect against a cyberattack,
- Failure to implement an authentication process to safeguard its ePHI, and
- Failure to have security measures in place to protect ePHI from unauthorized access during electronic transmission.
OCR Adamant about Weak Healthcare Compliance
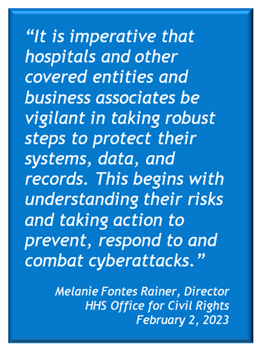 “Hackers continue to threaten the privacy and security of patient information held by healthcare organizations, including our nation’s hospitals,” said OCR Director Melanie Fontes Rainer in a February 2, 2023 press release.
“Hackers continue to threaten the privacy and security of patient information held by healthcare organizations, including our nation’s hospitals,” said OCR Director Melanie Fontes Rainer in a February 2, 2023 press release.
“It is imperative that hospitals and other covered entities and business associates be vigilant in taking robust steps to protect their systems, data, and records. This begins with understanding their risks, and taking action to prevent, respond to and combat such cyberattacks,” she said.
“The Office for Civil Rights provides help and support to healthcare organizations to protect against cybersecurity threats and comply with their obligations under the HIPAA Security Rule. Cybersecurity is on all of us, and we must take steps to protect our healthcare systems from these attacks.”
And if we don’t, clearly the consequences can be enormous—from compromised patient data, to large financial penalties and mandatory corrective actions monitored by the OCR, to reputational damage and loss of revenue.
Curing Our Hospitals – Four Immediate Steps to Better Security
The HIPAA rules addressing security, privacy, and breach notification have detailed requirements that hospitals and other HIPAA-regulated entities must comply with by law. Among these rules, four essential requirements will help you address the most frequent violations. They will take you a long way toward achieving robust cybersecurity and compliance in your organization. When the dust finally settles, the OCR press release will announce which of these essential requirements were unmet and therefore contributed to the Tallahassee Memorial data breach.
Security Risk Assessments. Required by the Security Rule, risk assessments are foundational to the effective security of protected health information, according to the OCR. The explicit requirement is to “conduct an accurate and thorough assessment of the potential risks and vulnerabilities to the confidentiality, integrity, and availability of electronic protected health information held by (your organization).”
The nine required components of a HIPAA-compliant risk assessment are enumerated in the OCR final guidance on risk assessments. A professional risk assessment will identify vulnerabilities and security and privacy gaps and prioritize them by level of risk. Then you’ll need to develop a plan of action to address each gap within a reasonable period of time. Risk assessments must be conducted every one to three years, depending on several factors.
Policies and Procedures. Not surprisingly, requirements for policies and procedures are evident throughout both the Security and Privacy Rule. The Breach Notification Rule requires policies and procedures for notifying the OCR and patients when a data breach has occurred. Even the most thorough, clear, and current policies and procedures are of little value unless employees and management know that they exist, know where to find them, and are trained to follow them. That’s why another essential requirement for HIPAA compliance is regular employee training.
Employee Training. HIPAA training is required as an Administrative Safeguard under the Security Rule and as an Administrative Requirement under the Privacy Rule. The Security Rule, as an example, mandates that a HIPAA-regulated entity meet three basic training requirements, These training requirements include (1) providing appropriate authorization and supervision of workforce members who work with ePHI, (2) training all workforce members regarding security policies and procedures, and (3) applying appropriate sanctions against workforce members who violate them. In other words, after you document your policies and procedures, plan to enforce them.
Be sure to include phishing schemes and other social engineering ploys in your employee training, along with ransomware training, to help employees recognize these common techniques and avoid falling for them.
Incident Response Plan. HIPAA Security Incident Procedures require that you (1) implement policies and procedures to address security incidents, (2) identify and respond to suspected or known security incidents, (3) mitigate the harmful effects of incidents that are known to you, and (4) document security incidents and their outcomes.
Even if there were no such HIPAA requirement, it is simply responsible organizational management to develop an Incident Response Plan that can be activated immediately when a security incident or data breach occurs. Acting in accordance with a documented and tested plan, especially during a tense or chaotic time, ensures that all the necessary steps are taken. Your response will be scrutinized by the OCR for compliance with the Breach Notification Rule.
Of course, there are numerous other HIPAA requirements related to security and privacy for PHI and ePHI. And other regulations govern the protection of personally identifiable information (PII), including payment card information.
Every hospital CISO, CSO, and CIO should be thoroughly familiar with all of the applicable requirements and the status of their organization’s compliance with each. This level of awareness is the hallmark of a healthy organization.
Summary
Right or wrong, large hospitals and health systems make headline news when they experience ransomware attacks, data breaches, and other security incidents. The scale is grand, the impact dramatic, the consequences captivating.
HIPAA compliance is intended to help you prevent incidents like the Tallahassee Memorial data breach. Compliance is a multifaceted undertaking with numerous requirements that must be met and then maintained. Lax maintenance leads to the erosion of security over time, which makes an organization highly vulnerable to hacking, ransomware, and other cybercrime.
For these reasons, the HHS OCR takes its compliance enforcement role very seriously. OCR actively investigates complaints and breach reports, conducts compliance reviews, issues subpoenas, imposes financial penalties, and monitors corrective action plans. Any healthcare organization who fails to comply with HIPAA requirements is rolling the dice. Because the odds are good that your organization will either come under OCR scrutiny, or suffer a ransomware or other cybersecurity attack. And the odds are even better that it will happen soon.