New PCI DSS 4.0 helps hotels, restaurants, cruise lines, and other hospitality providers address payment card security risks
As a hotel chain, cruise line, restaurant franchise, entertainment venue, or other member of the hospitality industry, chances are your organization accepts one or more payment cards from the major brands who govern the payment card industry (e.g., American Express, MasterCard, Visa, and Discover.) For most hospitality providers, compliance with the PCI Data Security Standard is mandatory.
Timeline for Hospitality Industry Compliance with PCI DSS 4.0
The new PCI DSS 4.0 version was released on March 31, 2022, and must be fully adopted in all organizations not later than March 31, 2025. Until March 31, 2025, aside from requirements designated for immediate adoption, most of the new v4.0 requirements are to be treated as best practices.
The previous PCI DSS version (3.2.1) will be retired on March 31, 2024, providing ample time for organizations currently assessing security against the v3.2.1 requirements to complete those assessments. The overall implementation timeline allows three years from the date of the v4.0 release, so there is no excuse for failing to comply with v4.0 by March 31, 2025.
Payment Card Brands Govern Hospitality Industry Compliance
The major payment card companies maintain their own separate compliance enforcement programs. These programs determine which merchants, third-party service providers, banks, and payment processors need to validate their compliance and at what validation level.
The payment brands also establish and collect fines or penalties for non-compliance. In addition, they govern whether you are eligible to complete a Self-Assessment Questionnaire (SAQ) or must complete a Report on Compliance (ROC), and whether an Attestation of Compliance (AOC) is also required.
 So, if the payment card brands are responsible for governance and compliance among their merchants and other payment card industry members, what is the role of the Payment Card Industry Data Security Standard?
So, if the payment card brands are responsible for governance and compliance among their merchants and other payment card industry members, what is the role of the Payment Card Industry Data Security Standard?
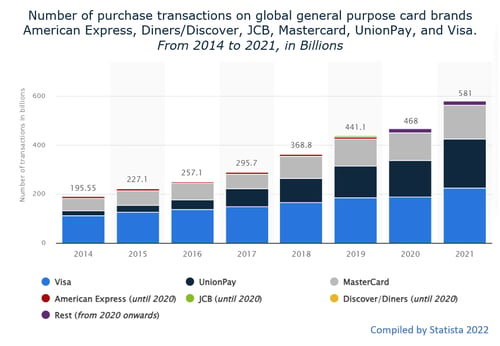
As Americans enthusiastically swipe, insert, tap, and hover their credit cards at check-out counters, and enter their card information into online purchase forms, hundreds of bits of high-value data are sent off into the ether. In 2021, some $581 billion in card transactions was processed, according to Statista.
With every transaction, our names, credit card numbers, expiration dates, security numbers, and other personal cardholder data are scanned and transmitted on a wing and a prayer and, we trust, with an ample measure of electronic security as well.
Protecting Those Transactions: The Purpose of PCI DSS
The Payment Card Industry’s Data Security Standard (PCI DSS) was developed to protect individual payment card data during and after these transactions. PCI DSS guides members of the payment card industry in establishing and maintaining effective security safeguards for that data. This is a vital service, considering the number and scope of exploitable vulnerabilities that exist today in the payment card industry.
Poor security practices, non-compliant security programs, and occasional lapses in security provide abundant opportunities for cybercriminals to steal, use, or sell your customers’ payment card data. Vulnerabilities can appear anywhere in the card-processing ecosystem—including at the merchant level (point of sale), as well as in systems operated by third-party service providers, and by the financial institutions who support merchants and process card transactions.
Vulnerabilities in Devices and Systems
The following devices and systems are frequently found in the hospitality industry. They often have vulnerabilities that are actively exploited by hackers and data thieves, and that can also be exploited by disgruntled or negligent employees.
-
Point-of-sale devices anywhere cards are accepted
-
Cloud-based systems for card data storage, processing, and other functions
-
Mobile devices, personal computers, web and email servers
-
Wireless hotspots in hotels, restaurants, and cruise ships
-
Web shopping and e-commerce applications for online purchases
-
Systems that transmit cardholder data to third-party service providers
-
Remote access connections.
The Top Three Attack Methods in Hospitality
The 2022 Data Breach Investigations Report (DBIR) published by Verizon notes 156 security incidents with at least 69 resulting in confirmed data disclosures in the hospitality industry.
Three attack methods accounted for 90% of all data breaches in the industry. They are (1) email and social engineering scams, (2) attacks on web applications and servers, and (3) exploitations of desktop sharing software.
-
Email Scams
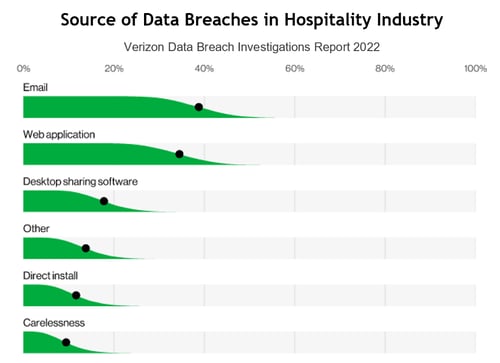 Email attacks leverage phishing, smishing, whaling, free software offers, and similar scams. They target an organization’s employees in efforts to discover access credentials that can lead to unauthorized network intrusion.
Email attacks leverage phishing, smishing, whaling, free software offers, and similar scams. They target an organization’s employees in efforts to discover access credentials that can lead to unauthorized network intrusion.
Phishing and whaling, in particular, are social engineering ploys that often lead to ransomware demands after data in networks or systems has been encrypted by cybercriminals.
Social engineering continues to play a significant role in successful email exploits and ransomware events and is on the rise in the hospitality industry over the past five years, according to the Verizon 2022 DBIR. The report defines social engineering as “a psychological compromise of a person that alters their behavior into taking an action or breaching confidentiality.”
-
Web App Attacks
Basic Web Application Attacks are also on the rise in hospitality. Attacks through web applications typically include SQL injection, cross-site scripting, malware, and distributed denial of service attacks. Most typically, stolen credentials are used to exploit or attack web applications. As in the case of malware, one cybercrime (e.g., credentials theft) serves to enable another, more lucrative cybercrime (e.g., web app attack).
Web application vulnerabilities stem from misconfigured web servers, application design flaws, and failures to validate or sanitize input from forms. In web application attacks, unauthorized individuals are able to gain administrative access rights to the web application itself or to the server. This gives them access to your organizations’ data or systems.
As with web servers, mail servers have become increasingly vulnerable, with 80% of attacks enabled by stolen credentials.
-
Desktop Sharing Software Exploits
Exploitable desktop sharing software can include remote desktop protocol (RDP), certain MS Windows applications, collaboration apps such as Zoom, and other sharing applications. Vulnerabilities arise depending on (1) what parties are involved in the sharing, (2) whether employees are using approved tools or their own software preferences to share desktops or files, and (3) whether all sharers are verified.
These vulnerabilities also provide avenues for third-party attacks. If such an attack is successful, it can introduce malware into the third party’s systems, which can then propagate to that third party’s customers. It is virtually impossible to be too cautious when executing and using desktop sharing software and similar sharing tools.
Tempting Targets Lead to Data Breaches
Few cybercriminals can resist these vulnerable assets and other tempting targets. Numerous security breaches in recent years have compromised hundreds of millions of credit cards and placed cardholders at great risk.
-
Recent breaches compromised the credit card data and other personal information of 16.6 million guests of MGM Resorts, and of 5.2 million Marriott Hotels guests.
-
Prestige Software, a hotel booking application, stored 10 million files without adequate security in a significant failure of compliance with PCI DSS requirements.
-
Carnival Corporation made headlines by paying $6 million to settle multiple lawsuits after a data breach affected 180,000 cruise guests and company employees.
Data held by numerous other hospitality providers has also been compromised in recent years.
Solutions to These and Other Vulnerabilities
It’s not as if we’re helpless in the face of vulnerabilities due to weak or incomplete hospitality industry compliance. Among the solutions that are readily available, it is crucial to (1) conduct regular employee training in security awareness, including phishing and ransomware elements, (2) implement comprehensive access controls across the organization, including password protections and multifactor authentication, and (3) pay much closer attention to properly configuring your enterprise assets and software for optimum security.
These specific actions can help resolve these specific vulnerabilities. However, it’s important to secure your entire organization’s networks and systems and the data therein. And the most effective way to do that is to comply with the latest version of the PCI Data Security Standard, PCI DSS 4.0, as quickly and thoroughly as possible. The 4.0 update reflects known and emerging threats, new advances in cybersecurity tools, and more stringent security requirements that constitute the latest payment card industry guidance.
Summary
As Americans enthusiastically swipe, insert, tap, and hover their credit cards at check-out counters, and enter card information into online purchase forms, hundreds of bits of high-value data are launched into space. $581 billion in card transactions was processed in 2021 alone. These transactions present tempting targets for cybercriminals, and the known vulnerabilities that exist in hospitality systems lay out the welcome mat.
The new PCI DSS 4.0 was released one year ago, and must be fully implemented by payment card industry members not later than March 31, 2025. Hospitality organizations have two years to meet the new requirements and complete their next risk assessments against the new standard. Far more than compliance is at stake here. Effective cybersecurity is an even greater gain.
The PCI Data Security Council has certified certain security firms, including 24By7Security, to serve as Qualified Security Assessors. QSAs are authorized to assist you in assessing the security of your cardholder data environments, reporting on your compliance status and remediation plans to your merchant banks and card processing brands, and assisting you with remediation implementation. Feel free to reach out for assistance at any time.










