Every cybersecurity program or information security program needs a guiding light. A beacon that shows the way. A navigational chart that steers the organization toward its security objectives. A security strategy is that beacon, that chart. Security strategy is the basis of any complete security program. For any company. In any industry. It guides your organization in developing a cohesive security environment and evolving that environment over time. It also enables management to make informed decisions about the company’s security investments.
Elements of a Good Security Strategy
A security strategy ensures that your security program will be complete, without gaps or missing safeguards. Following are the key requirements of a solid security strategy.
- As a progressive plan, your strategy should take a three-year outlook.
- It should include tactical security initiatives supporting the overarching strategy; tactics that may be phased over 90 days, 12 months, 24 months, and up to 36 months or three years.
- Your security strategy should consider known security threats, as well as vulnerabilities reported in your risk assessment and by inhouse IT personnel. It should also account for emerging threats to your organization. Consult your latest data analytics for trends and patterns that may be useful.
- It should specify annual budgetary support for the various security components of your strategy, including all resources required to execute the strategy.
Operating a security program without an overall strategy is like setting off on a two-week vacation without an itinerary or roadmap. Which, while it might seem like an excellent adventure, would be riddled with potential problems including detours, slow-downs, wasted time, unexpected expenses, and dead-ends.
Three Steps to Developing Your Strategy
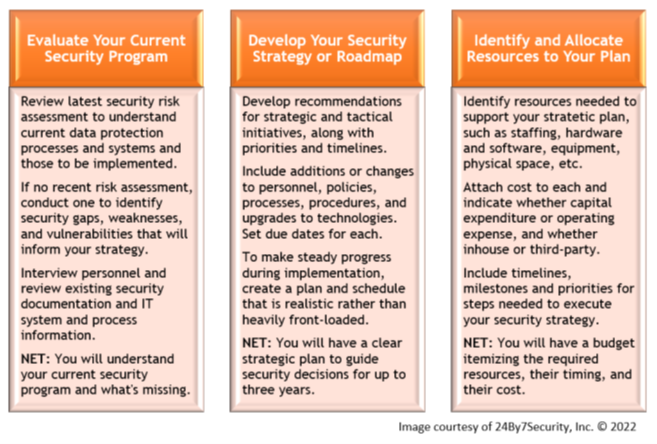
There are three basic steps in developing a security strategy. They consist of evaluating your current security program, developing your strategy or strategic plan, and identifying resources to support and execute the strategy.
1. Evaluate Your Current Security Program
-
Start by revisiting your most recent security risk assessment report. This will help you understand the data protection processes and systems that are currently in place, and those that are scheduled to be implemented in order to address gaps and missing safeguards.
-
If you don’t have a recent assessment report, you’ll need to conduct a security risk assessment to serve as a baseline. The assessment will identify security weaknesses and vulnerabilities, which in turn will inform the strategy so they are remediated in a logical sequence over a reasonable time.
-
This step also includes interviewing appropriate personnel and reviewing existing security documentation and IT system and process information. When you conclude this step, you should have a solid idea of where your current security program stands, what measures it includes, what it is missing, and the relative importance or priority of each.
2. Develop Your Strategy or Roadmap
-
-
Now that you know where you stand, and with the results of a security risk assessment informing your decisions, you can develop recommendations and target dates for strategic and tactical initiatives designed to harden or complete your security program.
-
You’ll need to develop recommendations for adding or modifying personnel, processes, procedures, and upgrades to technologies. And also establish due dates for implementing each recommendation.
-
Remember that your security strategy covers a three-year timeframe, with tactics that may be phased over 90 days, 12 months, 24 months, and up to 36 months. Therefore, be sure to pace yourself and avoid heavily front-loading the schedule. To make steady progress in implementing your strategies and tactics, avoid creating a plan or a schedule that is not realistic.
-
3. Identify and Allocate Your Resources
-
-
No security strategy can be implemented without resources. This third step is based on findings from your review in Step 1, and from developing your strategy in Step 2.
-
Now, you’ll develop recommendations for all of the resources required to support your strategy, including staffing, hardware, software, technology solutions, physical space, policies, procedures, communications, financial resources, and other assets.
-
You will also need to include timelines and milestones, as well as tactical priorities, for the steps involved in executing the security strategy.
-
Is a Security Strategy Required by Regulations?
Many security frameworks, such as NIST and ISO, recommend formulating a security strategy as a foundation for an overall security program. However, security strategic plans are not specifically listed in the mandated requirements of regulations such as HIPAA, GLBA, or SOX, for example.
Regardless of whether it is specifically required by regulations or established frameworks, having a strategic plan for your organization’s security makes sense for many reasons. Here’s why:
- A security strategy guides the development of your security policies.
- The tactical implementation of your strategy is reflected in your security procedures and processes.
- And while a strategic plan itself may not be mandated, the fact is that security policies and procedures are required—by most industry security frameworks and industry regulations.
Can you have effective and complete policies, procedures, and processes without the benefit of an overarching, three-year strategy? We think not.
Where to Go for Help
 The SANS Institute is one resource available to assist you in developing an effective security strategy. Their course, Aligning Security Initiatives with Strategy, provides the tools to help you become a security leader “who can build and execute strategic plans that resonate with other business executives, create an effective information security policy, and develop management and leadership skills to better lead, inspire, and motivate your teams.”
The SANS Institute is one resource available to assist you in developing an effective security strategy. Their course, Aligning Security Initiatives with Strategy, provides the tools to help you become a security leader “who can build and execute strategic plans that resonate with other business executives, create an effective information security policy, and develop management and leadership skills to better lead, inspire, and motivate your teams.”
With cybersecurity more crucial to an organization’s growth and health than ever before, security management enjoys greater visibility, budget, and opportunity—as well as greater responsibility, accountability, and scrutiny. Building a security strategy is not a mountain you want to climb without all the appropriate equipment and resources.
Stanford University offers an online course designed to assist security managers in bringing company executives to a clearer understanding of some of the technical aspects of cybersecurity. The ultimate goal is for security managers to obtain a sufficient budget to effectively address company security. This is not a security strategy course, per se, but may be useful in developing context for your strategy.
Another resource is a Virtual Chief Information Security Officer, readily available to you through the VCISO services provided by 24By7Security. Our experienced VCISOs, engaging with members of your management team, will create a high-level security strategic plan with a three-year outlook. Our VCISO will work on your behalf as an executive-level security strategist to develop and deliver your security strategic plan on time and on target. In addition, employing a qualified VCISO for this project means that your security strategy can be developed at a pre-agreed, one-time cost that you can budget.
Summary
A security strategy will guide the development of security policies, procedures, processes, equipment and software purchases, personnel recruitment and placement, and many other aspects of your overall security program. So, even though a strategic plan may not be a specified requirement of industry security frameworks or regulations, it is a logical and high-value foundation for your security program. Developing a security strategy does not need to be a painful or expensive experience characterized by missteps, obstacles, and rabbit holes. Resources are readily available to help you develop an appropriate and sustainable security strategy for your company. Take the first solid step by leveraging our VCISO expertise. We’ll be with you every step of the way.









