Non-compliance remains a serious problem, as these breaches and statistics confirm
 Americans are in love with credit, and with their credit cards. We use credit cards to pay for everything from a venti latte to a Maserati. No purchase is too trivial or too grand for our hard-working plastic.
Americans are in love with credit, and with their credit cards. We use credit cards to pay for everything from a venti latte to a Maserati. No purchase is too trivial or too grand for our hard-working plastic.
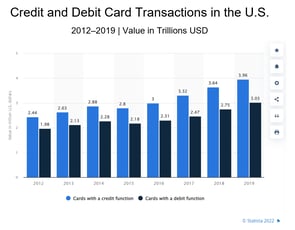
In 2019, the value of credit card transactions in the U.S. topped $3.96 trillion USD. Yes, trillion. And it has been climbing steadily from $2.8 trillion since 2015. When the numbers for 2020 become available, we are likely to see a spike in transactions due to our at-home isolation during the pandemic.
With every transaction, our names, credit card numbers, expiration dates, security numbers, and other personal cardholder data are scanned and transmitted by electronic devices and web applications that vary wildly in terms of technology and security.
Security Breaches Result from Non-Compliance with PCI DSS
The Payment Card Industry’s Data Security Standard (PCI DSS), with its 12 security requirements based on six fundamental security principles, is designed to guide merchants, payment processors, and third-party service providers in maintaining security safeguards that effectively protect our payment card data during and after these transactions.
However, some eye-popping data breaches demonstrate that non-compliance is a very real problem. Take these two examples.
Payment Data Stolen During Check-Out
For three months in 2020, hackers stole data from e-commerce websites used by international recording company Warner Music Group. Hackers exfiltrated data from the customers’ checkout pages, including their names, email addresses, telephone numbers, billing and shipping addresses, and payment card details (card numbers, security codes, and expiration dates). This security breach constituted a significant threat to WMG customers. That’s because their financial information could then be used to make fraudulent purchases. And their personal data could be used to conduct phishing attacks against them. Multiple lawsuits were filed and are pending, and this is certain to be a very costly data breach for WMG.
Massive Data Breach Affected 143 Million Americans
In 2017, consumer credit reporting agency Equifax experienced one of the greatest hacks on record. Over 45% of the U.S. population was affected by the theft of individual social security numbers, birth dates, addresses, driver’s license numbers, and credit card numbers. Equifax ultimately settled the breach for $425 million, and victims are still filing claims for expenses resulting from related identity theft or credit card fraud.
These Other Breaches Cost Companies $366.5 Million

Other stunning breaches included the leak of 40 million credit card numbers from Target in 2013, which cost Target nearly $18.5 million in settlements in the U.S. along with more than $202 million in legal fees.
Adobe lost three million credit card records in the same year and was fined $1 million to settle in 15 states along with an undisclosed sum to settle Customer Records Act violations.
Heartland Payment Systems, the card payment processor for 175,000 merchants, was breached in 2009. In addition to paying $145 million in compensatory damages, Heartland was restricted from processing payments for 14 months after the breach.
The details around these stunning data breaches reveal a variety of weak or absent security measures, despite the fact that each company should have been fully compliant with the PCI DSS.
Disturbing Statistics
Payment data remains the most attractive and lucrative commodity sought by bad actors. And web applications, such as e-commerce, payment, and shopping cart apps, have now overtaken point-of-sale devices as the main attack vector for retail data breaches.
The 2020 Verizon Payment Security Report reveals that the three least compliant industries are retail, financial services, and hospitality—and yet these industries are heavily engaged in payment card transactions. With only 7% of an organization’s information technology budget spent on security, it’s no wonder non-compliance is such a problem.
And it’s getting worse. There has actually been a 27.5 percentage point decline in PCI DSS compliance since 2016.
In 10 years of investigating and reporting on PCI DSS compliance, Verizon has never found a company that was fully PCI DSS compliant at the time it was breached. A study by SecurityMetrics supports this statement, finding that only 43% of PCI DSS requirements had been met when data was breached. It’s so unnecessary when you consider that the vulnerabilities exploited by hackers to breach payment systems are covered by specific sections of the PCI Data Security Standard. If the standard had been fully applied, the vulnerabilities would have been resolved.
Merchants, payment processors, and third-party service providers have abundant security tools, data security guidance, and compliance services available to them. And yet they continue to ignore the value of PCI DSS compliance.
Benefits of PCI DSS Compliance
 Achieving and maintaining compliance with the PCI Data Security Standard offers a number of benefits, including greater peace of mind knowing that cardholder data has been protected and secured in accordance with established payment card industry guidance.
Achieving and maintaining compliance with the PCI Data Security Standard offers a number of benefits, including greater peace of mind knowing that cardholder data has been protected and secured in accordance with established payment card industry guidance.
Additional benefits for organizations who are fully PCI DSS compliant include the following:
- Avoids the costs of non-compliance, which include fines and fees applied by merchant banks and card payment processors. Costs also include lawsuits and legal claims and the termination of bank accounts and card processing contracts.
- Reduces the odds of experiencing a data breach by resolving the security vulnerabilities that lead to breaches.
- Enhances business credibility and reputation and increases customer confidence and loyalty.
These benefits can be enjoyed by any merchant, payment processor, and other third-party service providers who make a commitment to achieve and maintain compliance with the prevailing PCI Data Security Standard.
Updated Version of PCI DSS is Now Available
The PCI Data Security Standard is a framework of technical and operational requirements designed to guide those in the payment card industry in better protecting customer account data. The current version of the standard, PCI DSS v3.2.1, has been updated to v4.0 effective as of March 2022.
For all payment card industry companies, these two new requirements are effective immediately for all PCI DSS 4.0 assessments:
12.3.2 - A targeted risk analysis must be performed for each PCI DSS requirement that is met with the customized approach.
12.5.2 - PCI DSS scope must be documented and confirmed at least once every 12 months.
For service providers, these four new requirements are effective immediately for all PCI DSS 4.0 assessments:
8.3.10.1 - If passwords/passphrases are the only authentication factor for customer user access, passwords/passphrases must be changed at least every 90 days or the security posture of accounts must be dynamically analyzed to determine real-time access to resources.
11.4.7 - Multi-tenant service providers must support their customers for external penetration testing.
11.5.1.1 - Covert malware communication channels must detect, alert and/or prevent, and address via intrusion-detection and/or intrusion-prevention techniques.
12.9.2 – Third-party service providers must support customers’ requests to provide PCI DSS compliance status and information about PCI DSS requirements that are the responsibility of the service provider.
In addition to these new requirements of PCI DSS v4.0, which are effective immediately, the myriad other new requirements must be implemented not later than March 31, 2025.
As an aid, a complete summary of changes is available from the PCI Security Standards Council in this PDF.
In addition, 24By7Security, Inc. is a certified PCI Qualified Security Assessor Company authorized to guide and assist members of the payment card industry in achieving PCI DSS compliance. Our Managing Director, Rema Deo, is certified as a PCI Qualified Security Assessor and, as such, oversees all PCI DSS compliance engagements for the company.
Summary
With annual credit card transaction volumes approaching $4 trillion, securing data at every point in the cardholder data environment is not just good business. Comprehensive security throughout the payment cycle is required by the Payment Card Industry’s Data Security Standard. Merchant banks and payment processors are responsible for enforcing the standard and can impose fines and terminate processing contracts for non-compliance, especially when it leads to a data breach.
PCI DSS compliance is trending downward, and industry sources have found that companies who suffer data breaches are far from fully compliant. This cause-and-effect relationship has an obvious message.
To help merchants and other industry members achieve compliance, the PCI Data Security Council has certified certain security firms, including 24By7Security, to serve as Qualified Security Assessors. These QSAs are authorized to assist merchants in assessing the security of their cardholder data environments, reporting on their compliance status and remediation plans to merchant banks and card processing brands, and assisting with remediation implementation.









