Using the Prioritized Approach Tool To Track and Report Progress
In 2006, the payment card industry (PCI) established the data security standard (DSS) to ensure that all companies who accept, process, transmit, or store credit card information, including user cardholder data, perform those functions securely, and can demonstrate that they do.
The data security standard is based on six guiding principles, with 12 security requirements comprising PCI DSS compliance. While enterprise companies with teams of information technology experts may have the resources to comply, smaller and mid-size merchants may be challenged in unique ways. To assist all companies in achieving compliance, the PCI Security Standards Council created several convenient alternatives along with associated forms and other tools.
Compliance Options Address Special Needs
One option is a Self-Assessment, which combines a Security Questionnaire with an Attestation of Compliance, enabling an organization to verify its compliance status with PCI DSS. Watch for a future blog describing this option.
Another option is the Prioritized Approach, a tool that provides a clear roadmap to complying with the 12 security requirements in accordance with six established security milestones that are prioritized by the merchant organization.
Today we will examine the Prioritized Approach and how it can help a merchant move efficiently and cost-effectively toward the required PCI DSS compliance.
Overview of the Prioritized Approach
The Prioritized Approach framework was first introduced by the PCI Security Standards Council more than a decade ago. It was designed to enable merchants to identify their greatest data security risks in order to address them first, thereby protecting cardholder data faster and reducing their risk while working toward compliance.
It also enables them to demonstrate their progress toward compliance to key stakeholders, such as banks and payment processing brands.
For smaller merchants especially, this approach lets them proceed at a pace their business can support and enables them to control the costs that are often associated with achieving and proving compliance on an aggressive schedule or at the enterprise level.
Prioritized Approach Milestones
The Prioritized Approach centers around six security milestones, giving merchants insight into the areas of their business that are most important to secure. The over-arching focus is on protecting cardholder data. Taking the required steps to comply with the PCI Data Security Standard is the best way to do that.
 Milestone 1: Remove sensitive authentication data and limit data retention. This is #1 for a reason. Storing cardholder data, especially very private authentication information, is a significant risk for merchants. Conversely, the lower the volume of cardholder data you store and retain, the lower the risk of its being lost, stolen, or otherwise compromised. The mantra here is, if you don’t need it, don’t store it.
Milestone 1: Remove sensitive authentication data and limit data retention. This is #1 for a reason. Storing cardholder data, especially very private authentication information, is a significant risk for merchants. Conversely, the lower the volume of cardholder data you store and retain, the lower the risk of its being lost, stolen, or otherwise compromised. The mantra here is, if you don’t need it, don’t store it.
Milestone 2: Secure the perimeter. Protect your systems and networks and be prepared to respond to a system breach. The perimeter includes various access points to the data you are processing or storing, and robust controls should be in place to secure those points. This milestone also addresses procedures for responding to data breaches, including notifications.
Milestone 3: Secure applications. The applications you use for credit card payments, processes around those applications, and the servers on which those applications operate are the focus of this security milestone. Weaknesses in any of them create vulnerabilities that can be exploited to steal or otherwise compromise cardholder data.
Milestone 4: Monitor and control access to systems. This is about security controls that enable you to identify who, what, when, and how individuals are accessing your network and cardholder data environment.
Milestone 5: Protect stored cardholder data. Think of this as a corollary to Milestone 1. If you have analyzed your business and determined that you must store primary account numbers, for example, this milestone identifies the important security protections for that data.
Milestone 6: Finalize remaining compliance work, and make sure all controls are in place. The intent here is to complete PCI DSS compliance, and finalize all remaining policies, procedures, and processes for protecting your cardholder data environment.
Description of the Tool
The Prioritized Approach tool is a three-tabbed Excel spreadsheet.
- Tab 1 – Instructions. This sheet offers simple instructions for using the tool, including completing certain form fields.
- Tab 2 – Prioritized Approach Summary. This sheet contains forms, with some fields to be completed before you begin. Others will auto-fill based on entries in Tab 3.
- Tab 3 – Prioritized Approach Milestones. This is where the real work happens. In addition to all 12 security requirements of the Data Security Standard, this sheet lists and describes numerous sub-actions to be completed as part of each requirement. Each sub-action is matched, using color coding, to one of the six milestones. This convenience enables users to focus on Milestone 1, for example, and easily find all sub-actions that must be completed for that milestone.
Instructions on Tab 1
The instructions include a cautionary note that achieving compliance entails successfully meeting ALL applicable PCI DSS requirements, regardless of the sequence in which they are implemented or the fact that the merchant is using the Prioritized Approach. This caution is meant to guide the thorough and careful completion of the Prioritized Approach Milestones (Tab 3).
As part of the instructions, users are asked to provide the Status of Compliance with each requirement and its sub-actions, line by line, by entering either Yes, No, or N/A in Column C of the Milestones sheet (Tab 3).
This step, in turn, automatically populates the Percentage Complete fields on the Summary sheet (Tab 2). This initial activity is essential in providing a starting point for all future compliance implementation activities.
- If an action is complete and fully compliant with the requirement, the status entered is Yes and no further action is necessary.
- If a requirement is not applicable to the organization, the status entered is N/A. In this case, the merchant must also describe why the action is not applicable.
- If an action is not complete yet, the status entered is No. In this case, the merchant must describe the stage of implementation, the estimated completion date for the milestone, and any clarifying comments.
Filter functions on the Milestones sheet (Tab 3) can be used to analyze status by milestone and sort in other ways for convenience in proceeding toward compliance.
The spreadsheet may be shared with the card processing entity or bank to demonstrate the merchant’s progress toward achieving compliance. It may also be shared with the merchant’s Qualified Security Assessor.
NOTE: 24By7Security is certified as a Qualified Security Assessor and can assist any organization in achieving and verifying PCI DSS compliance, including preparation of the Report on Compliance (ROC) and Attestation of Compliance (AOC).
Contents of Tab 2
The Prioritized Approach Summary collects contact information and other specifics about the merchant seeking compliance via the Prioritized Approach, as follows:
Part 1 – Merchant or Service Provider Information
Part 2a – Merchant Business
Part 2b – Service Provider Business
Part 3 – Relationships
Part 4 – Transaction Processing
Part 5 – Estimated Date for Achieving Full Compliance
Part 6 – Signature of Executive Officer
The Summary sheet also includes a matrix listing the six compliance milestones, the percentage of completion for each milestone, and the estimated date for full completion of each milestone. The matrix summarizes at a glance the data entered in Tab 3 and serves as a snapshot of compliance progress at any given time.
Below is a partial view of the Summary sheet.
![]()
Detailed Example from Tab 3
Requirement 1 of the 12 requirements of the PCI Data Security Standard has to do with installing and maintaining a firewall to protect cardholder data. Supporting this requirement, listed on Tab 3, are five sub-actions, including:
- Establish and implement firewall and router configurations standards as specified below.
- Build firewall and router configurations that restrict connections between untrusted networks and any system components in the cardholder data environment.
- Prohibit direct public access between the internet and any system component of the cardholder data environment.
- Install personal firewall software or equivalent functionality on any personal computing devices that connect to the internet when outside of the network and which are also used to access the cardholder data environment.
- Ensure that security policies and operating procedures for managing firewalls are documented, in use, and known to all affected parties.
The excerpt below illustrates sub-action 1.1 and the specific sub-requirements to be met, along with the milestone associated with each one.
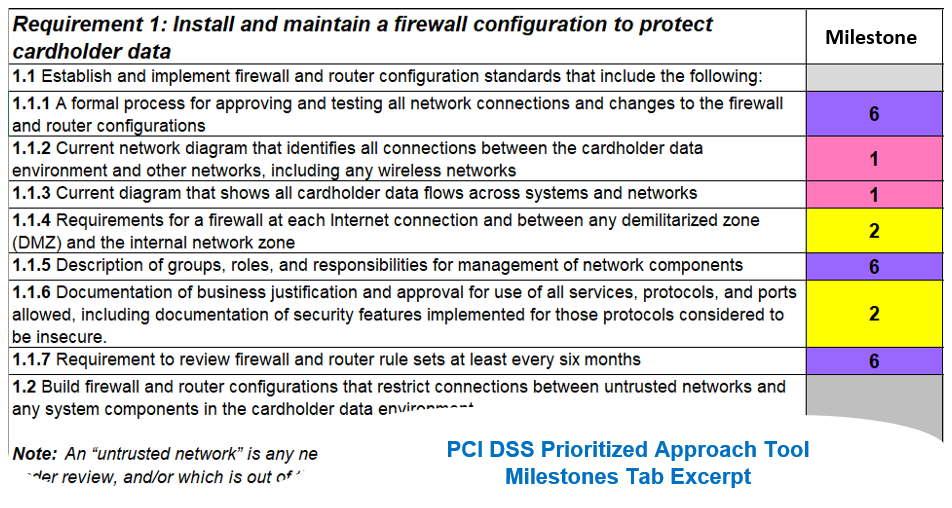
In all, Tab 3 presents 266 rows addressing all 12 compliance requirements and their sub-actions and supporting requirements. The snapshot above is representative of the organization and level of detail for each requirement. The complete spreadsheet tool is available here.
While detailed and comprehensive, the tool is surprisingly easy to navigate and serves as a thorough guide to achieving PCI DSS compliance for any organization.
In achieving and maintaining compliance, organizations can demonstrate their commitment to protecting cardholder data by effectively securing their cardholder data environments, including systems, networks, applications, servers, routers, and other components. In doing so, they significantly reduce their risk of data loss, theft, and abuse as well as the costs associated with data breaches.
Summary
The Prioritized Approach framework was designed by the PCI Security Standards Council to enable merchants to identify their greatest vulnerabilities in securing cardholder data so those risks may be addressed first. The priorities are presented as six milestones, which relate to the 12 security requirements necessary to achieve complete PCI DSS compliance.
The Prioritized Approach tool is a spreadsheet that helps merchants establish an initial benchmark (i.e., where they stand on Day One in terms of meeting the 12 requirements), track their progress toward compliance, and demonstrate their progress to key stakeholders at any given time. The tool is a comprehensive guide to achieving compliance at a pace and cost that some merchant businesses may find easier to support than more aggressive or enterprise-level approaches to compliance.
PCI DSS Update: Version 4.0 of the Data Security Standard is scheduled to be released near the middle of 2021. Watch this blog for more information.






.png)
.png)
