Two New PCI DSS Requirements Warrant Your Attention Sooner Than Later
Among the over 60 new requirements imposed by PCI DSS 4.0, some demand near-term attention
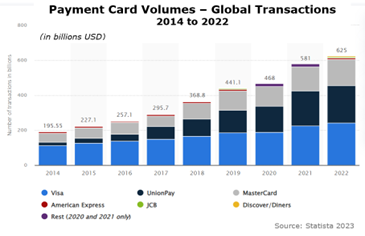
The use of credit, debit, and other payment cards, and the value of payment card transactions, continue to set records every year as consumers worldwide use their cards to acquire goods and pay for services.
Most recently, card transactions reached a record $625 billion (USD) globally in 2022, up 7.5% over 2021, according to Statista.
With this unprecedented use, personally identifiable information and payment card data are transmitted near and far in record numbers. Resulting data breaches have generated unfavorable press for hospitality giants like MGM Resorts, Marriott Hotels, and Carnival Corporation and have also plagued smaller organizations.
The increased risk resulting from record transactions led the Payment Card Industry to revamp its Data Security Standard last year with dozens of new, more stringent security requirements. The deadline for compliance with the more than 60 new requirements in PCI DSS 4.0 is looming for merchants, third-party service providers, and card payment processors.
Compliance Timeline for PCI DSS 4.0
The new PCI DSS requirements were released on March 31, 2022, and must be fully adopted by payment card industry members no later than March 31, 2025. The overall implementation timeline allows three full years, so there is no excuse for failing to comply with v4.0 by March 31, 2025. Members of the industry should already be well on their way toward incorporating this upgrade in their organizations.
The previous PCI Data Security Standard (version 3.2.1) will be officially retired on March 31, 2024. Unless you are currently actively engaged in a security assessment against that version, you will need to embrace v4.0 requirements before your next annual assessment.
The Perils of Partial Compliance
Compliance with the new PCI DSS requirements will help maintain security safeguards that effectively protect payment card data in motion and at rest. It will also significantly reduce vulnerabilities that present open doors for hackers, phishers, and ransomware criminals.
But what about organizations that have not complied fully with all applicable requirements? The facts indicate they are much more vulnerable. Consider these two industry reports:
- In the ten years that Verizon has been investigating and reporting on PCI DSS compliance for its annual Payment Security Report, the company has never found an organization that was fully compliant at the time it experienced a payment card data breach.
- Coming at it from a slightly different perspective, a study by SecurityMetrics found that only 43% of PCI DSS requirements had been implemented by an industry member when their card data was hacked.
Security executives owe it to their customers, shareholders, and investors to take PCI DSS compliance more seriously and to implement more rigorous security. The PCI Data Security Standard is the proven path to that goal, and v4.0 is the latest, most comprehensive security framework to keep your data safe and secure.
While there are more than 60 new requirements in the updated framework, some warrant closer scrutiny as you prepare to implement DSS 4.0 with your next security assessment. This article examines two of them that may demand extensive attention.
New PCI DSS Requirements Include Scoping Your Data Environment Before Your Security Assessment
One of the changes in PCI DSS 4.0 requires a compliant organization to conduct a formal, well-documented annual scoping exercise. This is specified in requirement 12.5.2 and entails significant work by the merchant or third-party service provider each year. The annual scoping exercise is required by 4.0 to ensure that changes in your data environment and organization are folded into your next annual assessment. This 4.0 scoping exercise is not to be confused with scoping conducted by your Qualified Security Assessor (QSA) during the annual assessment.
Following are the high-level requirements described in the Summary of Changes document developed by the PCI Security Standards Council and available in their Document Library.
- 12.5.2. New requirement to document and confirm PCI DSS scope at least every 12 months and upon any significant change to the in-scope environment (that is, the card data environment that lies within the scope of the PCI DSS 4.0 security framework). This requirement is effective immediately for all v4.0 assessments.
-
12.5.2.1. New requirement for service providers to document and confirm PCI DSS scope at least once every six months and upon any significant change to the in-scope environment. This is considered a security best practice until March 31, 2025, when it becomes a compliance requirement.
-
12.5.3. New requirement for service providers for a documented review of the impact to PCI DSS scope and applicability of controls upon significant changes to organizational structure. This is also considered a best practice until March 31, 2025, when it becomes a compliance requirement.
Changes to In-Scope Environment. The new scoping exercise is an annual process that must encompass not only the Information Technology department but also all of the organization’s business units in order to identify any shadow IT that may have been introduced in the past year. Throughout the course of 12 months, many organizations install new technology, retire legacy systems, implement new software, change IT processes, and upgrade systems. Very often, there is no documentation of these changes beyond a purchase order, for example. In addition, changes to the organizational structure may occur throughout the year and must also be included in the annual scoping exercise, to be certain they are folded into your next annual assessment as necessary.
Example of Change to Cardholder Data Environment. One of the infinite examples might be the self-assessable organization that has been submitting SAQ-B IP assessments because its point-of-sale system is linked to its data environment via an IP connection. Within the year, this organization decided to allow customers the flexibility to purchase products on an e-commerce platform, in addition to the traditional in-store experience. Clearly, this change has a significant impact on the scope of the cardholder data environment. It needs to be documented thoroughly and accounted for in PCI DSS 4.0 compliance actions—and included in the scope of the next security assessment.
New PCI DSS Requirements Include Documented Employee Engagement in Data Security
Another significant change in the PCI DSS 4.0 standard is the requirement, in 10 of the 12 requirement categories, that roles and responsibilities for performing activities in that category must be documented, assigned, and understood by all employees responsible for carrying them out. Specifically, this new requirement is spelled out consistently in these categories: 2.1.2, 3.1.2, 4.1.2, 5.1.2, 6.1.2, 7.1.2, 8.1.2, 9.1.2, 10.1.2, and 11.1.2.
We have noted, time and again, that employees are the weakest link in the security chain. They get busy, they get distracted, they don’t read the security procedures, they forget what they’ve read, and they get creative with the rules. Like all modern security frameworks, PCI DSS 4.0 recognizes these vulnerabilities and now insists that employees must be aware of their roles and responsibilities concerning payment card and card data security.
 Employee View. In conducting security assessments as a Qualified Security Assessor, 24By7Security frequently asks employees if their roles and responsibilities are documented, and if they understand them. Unfortunately, the common answer is along these lines, “Yeah, we know what we need to do.”
Employee View. In conducting security assessments as a Qualified Security Assessor, 24By7Security frequently asks employees if their roles and responsibilities are documented, and if they understand them. Unfortunately, the common answer is along these lines, “Yeah, we know what we need to do.”
Management View. However, when we ask management-level staff, Human Resources, and Information Technology personnel if these roles and responsibilities are documented, clearly assigned, and understood by the responsible employees, the answer is generally “No.”
Addressing the Gap. Organizations can easily survey their own employees with these questions to determine the extent of the knowledge gap and its associated vulnerabilities. The fastest and easiest way toward compliance with this requirement is to evaluate all job descriptions, update them with security responsibilities, review them with employees, obtain signatures as proof of understanding, and distribute them appropriately.
Like many compliance activities, this should be an annual exercise to ensure ongoing, consistent compliance with the new 4.0 requirement. Developing detailed procedures for data security adds power to the job descriptions and is often a compliance requirement. In addition, a responsibility matrix summarizing job responsibilities can provide a convenient overview for ongoing maintenance and updating.
Tips to Help You Get It Right
These two new requirements must be incorporated into all new assessments and related documentation, along with the 60+ other new PCI DSS requirements. In its extensive Document Library, the PCI Security Standards Council has posted a 492-page document that reflects all of the new requirements of PCI DSS 4.0 to help guide you toward compliance.
Qualified Security Assessors, including 24By7Security Inc., have been trained in the v4.0 update and are available to assist you at any time. Contact us to schedule your next assessment. Organizations eligible for self-assessment may also engage us for assistance in navigating the v4.0 changes.
Either way, merchants, processors, and third-party service providers should be taking specific actions now, in accordance with the compliance timeline above, to prepare for a thorough assessment of the new requirements. Because of its scale, this is not an undertaking you want to postpone.
Summary
The release of PCI DSS 4.0 in March 2022 introduced significant and extensive updates to the Data Security Standard, as well as the forms and reports required to assess and validate compliance. The previous v3.2.1 will be officially retired on March 31, 2024, and unless you are actively engaged in a security assessment against that version, you will need to embrace v4.0 requirements before your next annual assessment.
Now is the time to take action to adopt the new PCI DSS requirements throughout your organization. Incomplete or partial compliance can lead to dangerous data breaches and other embarrassing security incidents. To avoid becoming a data breach statistic in the next Payment Card industry report, you will want to be fully compliant with PCI DSS 4.0 before your next security assessment.



.png)



.png)