 In addition to tracking and imposing penalties for HIPAA violations and data breaches, the U.S. Department of Health & Human Services (HHS) Office for Civil Rights (OCR) publishes a variety of news, press releases, and newsletters, including one offering cybersecurity guidance for members of the healthcare industry.
In addition to tracking and imposing penalties for HIPAA violations and data breaches, the U.S. Department of Health & Human Services (HHS) Office for Civil Rights (OCR) publishes a variety of news, press releases, and newsletters, including one offering cybersecurity guidance for members of the healthcare industry.
Earlier this year, the newsletter highlighted the three most common cybersecurity threats, and outlined measures required by HIPAA to prevent or mitigate them substantially. The newsletter targets all covered entities, including healthcare providers and business associates.
As cybersecurity and compliance experts with a core practice in healthcare, the 24By7Security team felt duty-bound to help disseminate this information as extensively as possible throughout the community. Today’s blog is based largely on the OCR newsletter.
The Top Cyberattacks in Healthcare
The most common cyberattack vectors threatening healthcare covered entities today are (1) phishing schemes, (2) the exploitation of known vulnerabilities, and (3) taking advantage of weak cybersecurity practices. Below we describe each of these vectors, followed by OCR recommendations for addressing each one.
#1: Phishing Schemes
These popular schemes are called phishing because the cybercriminal is like an angler trying to lure a fish into taking the bait. In the ocean that is healthcare, there are plenty of bites.
In phishing attacks, a hacker or other cybercriminal impersonates a trustworthy source in order to trick employees into divulging sensitive information via email or other electronic communication. By similar definition, phishing is a technique for attempting to acquire sensitive data, such as bank account numbers, through a fraudulent solicitation in an email or on a website in which the attacker masquerades as a legitimate business or reputable person.
Phishing escalates to whaling when the scheme targets the bigger fish in an organization, such as executives or other senior members.
#2: Exploitation of Known Vulnerabilities
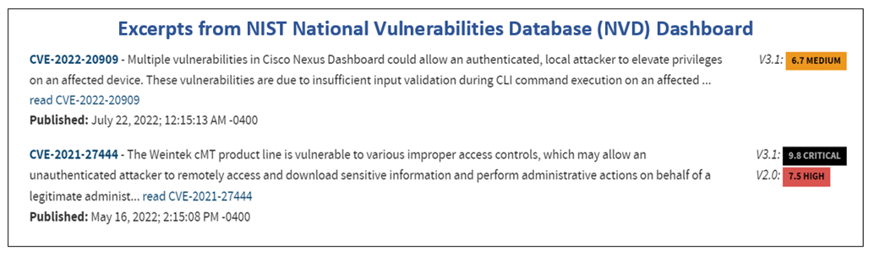
Hackers can penetrate a covered entity’s network and gain access to electronic protected health information, or ePHI, by exploiting vulnerabilities that are publicly known or acknowledged. The National Institute of Standards and Technology (NIST) maintains the National Vulnerability Database (NVD), which is the U.S. government repository for information about known vulnerabilities.
Exploitable vulnerabilities can exist in many parts of a covered entity’s IT infrastructure, including server, desktop, and mobile device operating systems; application, database, and web software; and router, firewall, and other device firmware. ePHI obtained through the exploitation of a known vulnerability can be readily sold on the dark web, and subsequently exploited by those who purchase it.
#3: Taking Advantage of Weak Authentication Practices
Weak, poor, or non-compliant cybersecurity practices are the low-hanging fruit of cybercrime and make an organization a very attractive target. Weak authentication practices enable attacks to be successful with high frequency. Citing a recent Verizon Data Breach Investigations Report, OCR noted that more than 80% of data breaches that result from hacking involve compromised or brute-forced login credentials.
Weak password rules, unenforced password rules, and single factor authentication are among the poor cybersecurity practices that contribute to successful attacks. And once an attacker is inside an organization, weak access controls can enable them to exploit privileged accounts, move at will among multiple computer systems, deploy malicious software, and steal ePHI.
Recommendations from the OCR
Citing these three attack vectors as the most common and successful within the healthcare industry, the OCR notes that some attacks may be sophisticated and exploit previously unknown vulnerabilities, which are called zero-day attacks.
However, the OCR emphasizes that most cyberattacks could be prevented or substantially mitigated if HIPAA covered entities and business associates implemented HIPAA Security Rule requirements to address the most common types of attacks.
More simply put, failure to comply with HIPAA Security Rule requirements allows the most common types of attacks to be successful.
The OCR newsletter recommends that covered entities take the actions detailed below. And knowing that the OCR is responsible for investigating and imposing penalties for non-compliant practices, this advice is ignored at your own peril.
How to Prevent Phishing Attacks
The OCR notes that the “HIPAA Security Rule requires implementation of a security awareness and training program for all workforce members” because every employee plays an important role in protecting the ePHI held by their organization. That role includes being able to detect a phishing attempt and take appropriate action.
- Teach your employees how to recognize phishing attacks and what to do when suspected attacks or actual attacks occur. A common procedure is to have employees report suspicious emails to a designated person or team.
- Training should also include management personnel, since they are subject to whaling attacks and need to know how to recognize and deflect them.
- The training program should be ongoing, evolving, and flexible enough to encompass recognizing and responding to both existing and emerging cybersecurity threats, from phishing to ransomware to malware and beyond.
- Employ innovative techniques to keep the training interesting and keep trainees engaged. Security training can fail if it is viewed as a burdensome or boring, or merely a “check-the-box” exercise consisting of self-paced slide presentations.
- Support your security training with periodic security reminders. One example of a security reminder is to send mock phishing emails to employees to gauge the effectiveness of the training and absorption. Offer additional, targeted training where necessary.
In addition to ongoing training and reminders, the OCR recommends implementing anti-phishing tools or technologies, noting that these can take several forms.
- There are tools that examine all incoming emails and verify that they did not originate from known malicious sites. Suspicious emails can be blocked, and appropriate personnel notified.
- Other tools scan links embedded in emails or documents attached to emails to identify potential threats and remove them if a threat is detected.
- Newer techniques use machine learning or behavioral analysis to detect potential threats and block them.
These solutions can be helpful in preserving the integrity and availability of ePHI, as required by HIPAA. The OCR further emphasizes that combining an engaged, educated workforce with technical solutions offers the best opportunity to reduce or prevent phishing attacks.
How to Prevent Exploitation of Known Vulnerabilities
Known vulnerabilities can often be addressed by applying vendor patches or upgrading to a new software version. If not available, vendors may recommend modifying configuration files or disabling affected services. In addition, the OCR recommends the following actions to prevent or reduce the exploitation of known vulnerabilities.
- Pay close attention to cybersecurity alerts, especially those describing newly discovered vulnerabilities. These alerts often include information on mitigation activities and patching. Two resources offering alerts are the Cybersecurity and Infrastructure Security Agency (CISA) and the HHS Health Sector Cybersecurity Coordination Center (HC3). You can also subscribe to the National Vulnerabilities Database email list or routinely monitor the NVD Dashboard.
- Upgrade, replace, or retire obsolete, unsupported applications, devices, and legacy systems to remove these vulnerabilities from your network or other IT infrastructure. If not immediately possible, add new safeguards or enhance existing safeguards to mitigate known vulnerabilities until an upgrade or replacement can occur. These interim safeguards may include increasing access restrictions, removing or restricting network access, disabling unnecessary features or services, and similar actions.
Another approach to preventing known vulnerabilities exploitation is to “implement a security management process to prevent, detect, contain, and correct security violations,” per the HIPAA Security Rule. The OCR emphasizes that the process must include conducting a risk analysis, as per 45 CFR 164.308(a)(1)(ii)(A)-(B).
- The risk analysis must assess potential risks and vulnerabilities to the confidentiality, integrity, and availability of ePHI. It must implement security measures sufficient to reduce those risks and vulnerabilities to a reasonable and appropriate level.
- The risk analysis must be accurate, thorough, and use processes that identify potential technical and non-technical vulnerabilities. Technical vulnerabilities, for example, may result from poor system development work or incorrectly implemented or misconfigured information systems.
- The risk analysis should also include use of a vulnerability scanner to detect obsolete software and missing patches and other vulnerabilities, as well as penetration tests to identify weaknesses that could be exploited by an attacker.
Once the risk analysis has identified, assessed, and prioritized all known vulnerabilities, the healthcare organization or business associate must implement appropriate measures to mitigate these vulnerabilities—such as applying patches, hardening systems, retiring or upgrading equipment, and various other mitigations.
How to Prevent Exploitation of Weak Authentication Practices
Covered entities are required to comply with authentication and access safeguards as described in 45 CFR 164.312(d), 164.312(a)(1), and 164.306(e). The OCR offers the following guidance to strengthen authentication and access controls, noting that a risk analysis should guide the implementation of appropriate authentication and access measures to reduce the risk of unauthorized access to ePHI.
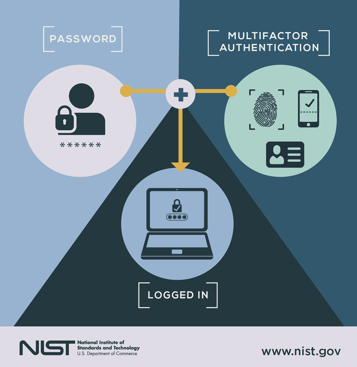 Implement authentication processes to verify that persons or entities seeking access to ePHI are who they claim to be. Stronger authentication solutions, such as multi-factor authentication, add another layer of cybersecurity, especially for remote workers.
Implement authentication processes to verify that persons or entities seeking access to ePHI are who they claim to be. Stronger authentication solutions, such as multi-factor authentication, add another layer of cybersecurity, especially for remote workers.- Restrict access to ePHI to only those requiring it. Use stringent role-based and/or user-based access. Align access policies with the minimum necessary standard or principle of least privilege by providing the minimum amount of access required for an employee to do the job.
- Establish a close connection to HR, so that access can be changed instantly when employee roles or employment statuses change.
- Consider a privileged access management (PAM) system. Privileged accounts, such as administrator and root accounts, have greater access freedoms. As a result, they present a higher risk of unauthorized access to ePHI than non-privileged accounts. A PAM system can control access to privileged accounts and detect and prevent their misuse.
- Periodically review and modify existing security measures to ensure they remain effective in protecting ePHI. Changes in operations, infrastructure, or environment can affect the security of your data and systems. When you implement a new technology, install a new system, identify a new threat to ePHI, or undergo a merger or acquisition, these changes can impact cybersecurity and compliance. Therefore, increased or additional security controls are required to reduce risk.
Password policies and enforcement can also help prevent unauthorized access to ePHI and other sensitive information. Extensive advice is available in this area from a variety of sources, including the 24By7Security blog.
Summary
The U.S. Department of Health & Human Services (HHS) Office for Civil Rights (OCR) publishes a variety of newsletters, including one offering cybersecurity guidance for members of the healthcare industry, including business associates. A recent newsletter highlighted the three most common cybersecurity threats in healthcare and outlined measures required by HIPAA to prevent or mitigate them substantially.
The most common cyberattack vectors threatening healthcare covered entities today are phishing schemes, the exploitation of known vulnerabilities, and taking advantage of weak authentication and access control practices. Actions required to prevent or seriously reduce these malicious exploits are not complicated or new. Instead, they are proven techniques that work effectively when actually implemented.
For covered entities who prefer professional assistance in implementation, help is a phone call away at 844.55.CYBER. That’s 844.552.9237.









