Journey to NIST CSF 2.0 Has Officially Begun
The Cybersecurity Framework published by the National Institute of Standards and Technology (NIST) is one of the foremost resources for managing cybersecurity risks holistically across an organization. It has been downloaded more than 1.7 million times by organizations of various sizes, geographic locations, and sectors or industries. It is also in use internationally, with nine language translations in addition to the original English version.
Overview of Current NIST Cybersecurity Framework
 U.S. Government agencies and private entities who are responsible for our nation’s critical infrastructure comprise the original and primary audience for the NIST CSF framework. All federal agencies are required to comply with the framework in accordance with presidential Executive Order 13800 signed in 2017.
U.S. Government agencies and private entities who are responsible for our nation’s critical infrastructure comprise the original and primary audience for the NIST CSF framework. All federal agencies are required to comply with the framework in accordance with presidential Executive Order 13800 signed in 2017.
Through deliberate intention, the nature of the framework is such that it also can be adopted by small, medium, and large businesses in a wide range of industries—regardless of whether or not they have a role in our nation’s critical infrastructure. Their adoption is voluntary.
The NIST CSF framework consists of five core security functions, including identifying, protecting, detecting, responding and recovering. The core functions are classified into categories and sub-categories. Solid emphasis is placed on incident response planning and the actions required to respond to and recover from a data breach or other security incident.
Reasons for the CSF Update
The NIST Cybersecurity Framework was designed, from inception, to be a dynamic and living document. It is a framework intended to be improved and evolved over time in order to (1) keep pace with security technology and threat trends, (2) integrate lessons learned, and (3) transform from a best practice to a common practice.
Known variously as the NIST Framework for Improving Critical Infrastructure Cybersecurity, the NIST Cybersecurity Framework, Framework, or CSF, the original framework was released in February 2014 after extensive engagement and collaboration by both public and private sectors.
Four years later, in April 2018, NIST updated the Framework with CSF 1.1.
That version is now four years old, and a lot has changed since 2018, from new security technologies to new security threats to new bad actors. Following are some of NIST’s objectives for the next update:
- Develop new interactive and machine-readable formats for the framework, which generally is downloaded from the NIST website.
- Ensure the framework is simple and flexible, particularly for smaller organizations whose cybersecurity requirements and resources may be less robust.
- Provide implementation guidance to help organizations use the framework more readily and easily, especially those who are just beginning to develop cybersecurity programs.
- Show more clearly how the National Online Information References Program (OLIR) can be used to map the CSF framework to other NIST and non-NIST cybersecurity frameworks.
NIST has also indicated that determining “whether and how to incorporate supply chain cybersecurity or third-party risk into the framework will be a significant focus for NIST as we proceed with this update.”
Early Results of Feedback Include Six Guiding Themes
 The NIST call for feedback went out on February 28, 2022, in the form of a Request For Information (RFI) asking how the NIST Cybersecurity Framework can be improved.
The NIST call for feedback went out on February 28, 2022, in the form of a Request For Information (RFI) asking how the NIST Cybersecurity Framework can be improved.
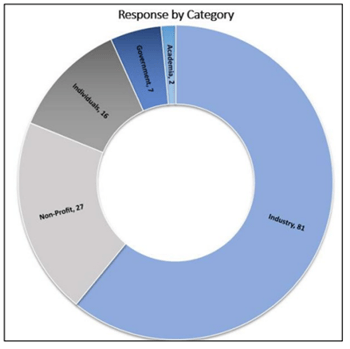
As of June 3, 2022, just three months later, more than 130 comments had been received, reviewed, and organized. The majority came from Industry (81 responses) and non-profits (27 responses). Some responses were very thoughtful and comprehensive, validating the sense that it is indeed time to update the framework again, and in a substantive enough way to warrant version 2.0 designation rather than version 1.2.
Analysis and organization of the 130 comments revealed commonalities and key areas of agreement and differences, which have been translated into six fundamental themes that will guide the framework update. As additional comments are submitted, NIST will incorporate as needed while avoiding duplication. The six themes, highlighted below, along with their sub-themes, are detailed in NIST’s summary of comments:
Theme 1: Focus on maintaining and building on the key attributes of the cybersecurity framework with the update. The sense is that the framework structure, including Tiers, Core, and Profiles, does not require significant changes.
Theme 2: Align the framework with existing efforts by NIST and others.
Theme 3: Offer more guidance for implementing the framework, which will be especially useful for smaller organizations and novices.
Theme 4: Ensure that the framework remains technology-neutral but is able to be readily applied to different technology issues, including new advances and practices.
Theme 5: Emphasize the importance of measurement, metrics, and evaluation in using the cybersecurity framework.
Theme 6: Consider various supply chain cybersecurity risks in developing the update.
Timing of CSF 2.0 Update and Interim Guidance
 The online Request For Information will remain open for comment for several more months. Anticipating that the update process will require a year or longer, NIST expects CSF 2.0 to be available toward the end of 2023 or early 2024.
The online Request For Information will remain open for comment for several more months. Anticipating that the update process will require a year or longer, NIST expects CSF 2.0 to be available toward the end of 2023 or early 2024.
Recognizing the investment organizations have made in implementing the framework as it exists today, NIST has indicated that it will consider backward compatibility as part of the update process.
In the meantime, NIST CSF 1.1 remains an active, viable, and widely adopted framework. Rather than deferring adoption of this effective cybersecurity framework in order to wait for the next version, NIST encourages organizations to adopt CSF 1.1 throughout the duration of the year-plus updating process.
Resources Available for NIST CSF 2.0 Update
Following are a few ways interested organizations can monitor the CSF update process.
- Visit the CSF Website. Visit the NIST CSF website for updates and opportunities to weigh in and check the new CSF 2.0 update page to follow the update process.
- Submit Comments. During the updating process, NIST intends to post at least one draft of CSF 2.0 and encourages input on what looks good and what can still be improved.
- Subscribe to Email Updates. Receive news about the CSF update delivered to your inbox, by signing up on the email subscription page.
- Stay Tuned with 24By7Security. We offer NIST CSF compliance support services and also publish a weekly blog on relevant cybersecurity and compliance topics, including NIST CSF 2.0.
Summary
Information security and cybersecurity are essential components of federal and corporate governance programs. In addition to being mandatory for federal agencies, the NIST Cybersecurity Framework assists organizations of all sizes and industries in developing effective cybersecurity programs without reinventing the wheel.
The process of updating to NIST CSF 2.0 began in February 2022, guided by multiple objectives that include keeping pace with evolving security technologies and threats, integrating lessons learned, ensuring the framework is simple and flexible enough to engage smaller organizations, and providing implementation guidance for new adopters.
The updating process will be collaborative and interactive and is likely to require a year or more to complete. Until CSF 2.0 is available in late 2023 or early 2024, NIST urges organizations to proceed with implementation of CSF 1.1, because cybersecurity is paramount for all.







.png)
.png)
