You Need The Security Framework That’s Best For Your Organization
As an aid to companies in their quest for better cybersecurity, several associations have developed security frameworks in the past two decades. Choosing the appropriate framework for your business is a strategic decision and is one of the early steps in building a complete cybersecurity program for your organization.
Security frameworks vary in terms of industry focus, type and number of security requirements, and other layers of complexity. Several security frameworks are widely known and have been broadly adopted for reasons we’ll explore in this blog. Several others are less prevalent but provide flexibility and options that may be attractive to smaller businesses and certain other organizations.
Security Framework 1: NIST CSF
Sponsor: The National Institute of Standards and Technology (NIST)
Framework Name: Cybersecurity Framework (CSF)
Established: 2014
Primary Audience: U.S. Government entities responsible for critical infrastructure.
Secondary Audience: Any organization
Primary Purpose: Ensuring government agencies and entities protect the U.S. critical infrastructure from internal and external threats, as well as the private organizations who are responsible for critical infrastructure.
 Additional: Developed in response to presidential Executive Order 13636 signed in 2013 to Improve Critical Infrastructure Cybersecurity. This order aimed to increase the level of core capabilities for our critical infrastructure to manage cyber risk through three key areas: information sharing, privacy, and adoption of cybersecurity practices.
Additional: Developed in response to presidential Executive Order 13636 signed in 2013 to Improve Critical Infrastructure Cybersecurity. This order aimed to increase the level of core capabilities for our critical infrastructure to manage cyber risk through three key areas: information sharing, privacy, and adoption of cybersecurity practices.
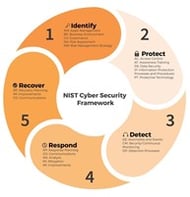
The NIST CSF framework consists of five core security functions, including identify, protect, detect, respond and recover. The core functions are classified into categories and sub-categories. A solid emphasis is placed on incident response planning and the actions required to respond to and recover from a data breach or other security incident.
The NIST Cybersecurity Incident Handling Guide provides specific advice for rapidly detecting incidents, minimizing loss and destruction, mitigating the weaknesses that were exploited, and restoring IT services after an incident.
Applicability: All federal agencies are required to comply with the framework as directed by presidential Executive Order 13800 signed in 2017. For all other organizations, NIST is a voluntary framework. It can be applied to most businesses, including small, medium, and large businesses in a wide range of industries—regardless of whether you have a role in our nation’s critical infrastructure.
Security Framework 2: SOC SSAE 18
Sponsor: The American Institute of Certified Public Accountants (AICPA)
Framework Name: Statement on Standards for Attestation Engagements (SSAE), System and Organization Controls (SOC) Reporting
Established: 2017

Primary Audience: Vendors and third parties who provide services to other organizations.
Primary Purpose: Facilitate proper security safeguards in organizations that collect and store personal customer information in cloud services, including software-as-a-service (SaaS) companies, and other vendors and third parties.
Additional: SSAE18 is an auditing standard that defines how assessments of internal controls on financial reporting are conducted for Service Organizations (i.e., vendors and third-party service providers). SSAE18 replaced the previous SSAE16 standard from 2010.
SOC 2 is a challenging framework to implement, with 61 compliance requirements governing the destruction of confidential information, the monitoring of systems for security anomalies, procedures for responding to security events, and internal communications, among others.
The SSAE audit assessments, or attestations, result in one or more of three basic reporting types as outlined below.
- A SOC 1 report is issued on an organization’s internal controls over financial reporting (ICFR). This report helps verify if the service organization is managing its finances correctly.
- SOC 2 & 3 reports are issued on an organization’s controls over its systems relating to security, availability, processing integrity, confidentiality, and privacy. These reports are useful if service organizations are providing IT services such as billing, technology services, cloud services, or remote hosting, to name a few.
- The SOC 2 report is intended for a limited audience – those within the service organization and their clients who understand the parameters of a SOC 2 report.
- SOC 3 is a more general-use report that covers the same topics but is intended for anyone.
Applicability: If you are a service organization and hold information that belongs to others, you should be able to demonstrate that you have the necessary controls, policies, and procedures in place to safeguard your customers’ data and ensure data privacy. SSAE 18 would also apply to any subcontractors who may support you in handling that sensitive data.
SSAE18 can provide your organization with an advantage over your competitors who have not adopted this security framework.
Security Framework 3: ISO IEC 27001
Sponsor: The International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC)
Framework Name: ISO IEC 27001 Standards
Established: 2005
Primary Audience: Any organization
Primary Purpose: Promulgate international standards for managing information security management systems (ISMS) to protect data and similar digital assets.
Additional: Most organizations have information security measures in place to one degree or another. Too often, however, those security controls are fragmented and may resemble a patchwork of band-aids applied over time to address specific issues. An information security management system (ISMS) brings organization and integration to a company’s information security program. It helps you protect the security of financial information, intellectual property, employee details, and information entrusted to you by third parties.
With 114 controls in 14 categories, ISO 27001 offers detailed requirements for establishing, implementing, maintaining, and improving your organization’s information security management system (ISMS). For the same reason, this security framework can be challenging to implement for smaller and mid-sized businesses.
While certification to the ISO 27001 Standard is optional, many organizations take this additional step to demonstrate that they have properly implemented the framework in order to effectively protect their stakeholders’ information assets.
A complementary information privacy standard, ISO 27701, was developed in 2019 to aid organizations in complying with the European General Data Protection Regulation of 2016 (GDPR).
Applicability: The ISO 27001 framework is appropriate for any organization seeking to achieve and demonstrate an effective information security program. It can be used in conjunction with many other regulatory requirements, such as the HIPAA Security Rule and ONC and CMS Rules in healthcare, the GLBA and FFIEC in the financial industry, and other regulations that have provisions for information and data security.
Security Framework 4: SOC For Supply Chain
Sponsor: The American Institute of Certified Public Accountants (AICPA)
Framework Name: Statement on Standards for Attestation Engagements (SSAE), System and Organization Controls (SOC) for Supply Chain
Established: 2020
Primary Audience: Organizations that are part of a supply chain, including manufacturers, producers, and distributors.
Primary Purpose: To help manufacturers, producers, distributors, and their business partners identify, assess, and address supply chain security risks.
 Additional: Supply chains have become highly sophisticated and complex in the digital age, and there is often a great degree of interdependence and connectivity between them, which increases risk and vulnerability throughout the supply chain. Recently, the pandemic has spotlighted the crucial role of supply chains in sustaining consumers, businesses, and healthy national economies.
Additional: Supply chains have become highly sophisticated and complex in the digital age, and there is often a great degree of interdependence and connectivity between them, which increases risk and vulnerability throughout the supply chain. Recently, the pandemic has spotlighted the crucial role of supply chains in sustaining consumers, businesses, and healthy national economies.
This new security framework enables organizations to have an attestation engagement performed by a Certified Public Accountant (CPA) in their manufacturing, production, or distribution system. This results in a professional financial view of the audited organization’s system and a professional opinion on the effectiveness of security controls within that system.
This objective review is not unlike the new role third-party assessment plays in validating supply chain security among defense contractors.
The end result is to assist organizations in evaluating their risks, understanding the effectiveness of their controls, and identifying weaknesses that need to be addressed in order to better secure their part of the supply chain.
These controls apply the same criteria used to evaluate system controls in a service organization (SOC 1 and 2) and organization-wide controls in a cybersecurity examination, according to the SOC For Supply Chain description by AICPA.
Applicability: If you are part of a supply chain, especially an extensive and complex system, every time you conduct business with a supplier or other service provider new risks are introduced into the supply chain. Now, you have access to a voluntary but useful framework designed to protect your organization, your suppliers and subcontractors, your customers, and your information.
Several Other Frameworks to Consider
 COSO Risk Management Framework for Not-for-Profits (NFPs)
COSO Risk Management Framework for Not-for-Profits (NFPs)
The Committee of Sponsoring Organizations of the Treadway Commission (COSO) is a joint initiative to combat corporate fraud and help NFPs ensure proper stewardship for funds they manage. Established in 1985, the framework is sponsored by the American Institute of Certified Public Accountants, the American Accounting Association, and three other financial/accounting associations. The COSO framework specifies three categories of internal controls (operations, reporting, and compliance) with a focus on securing an organization’s assets against fraud.
Center for Information Security (CIS) Controls Framework for Business
Designed for any business or organization, the CIS Controls framework specifies a manageable 20 cybersecurity requirements intended to help enhance your security posture. CIS offers three levels of information security controls based on whether your cybersecurity expertise and resources are limited, moderate, or advanced.
This voluntary framework is especially popular among SMBs because it (1) helps them create cybersecurity programs that are within their budgets, (2) provides the ability to prioritize program implementation activities and phase them in, and (3) clarifies how to implement the controls.
Control Objectives for Information Technologies (COBIT) Framework for Business
Control Objectives for Information and Related Technologies, or COBIT 2019, is an integrated IT cybersecurity framework for businesses. First released in 1996, the framework is sponsored by the Information Systems Audit and Control Association (ISACA) to promote information technology management and governance. The voluntary framework defines generic processes for managing IT, with each process defined along with process inputs and outputs, key process activities, process objectives, and performance measures.
Summary
Information security and privacy have become increasingly vital components of overall corporate governance programs. Industry associations like NIST, ISO, AICPA, ISACA, and others have developed security frameworks to guide businesses in implementing effective cybersecurity.
These security frameworks provide proven standards that can be adopted by any organization to demonstrate that the company is serious about protecting the information assets of its diverse stakeholders. The security frameworks are dynamic and evolutionary and are routinely updated to reflect advances in cyber threats as well as in information security techniques.
Today, businesses of all sizes across virtually all industries have ready access to a security framework that is right for them.






.png)
.png)

