As of Nov 2021, CMMC 2.0 was introduced and the information below may not apply in its entirety.
November is widely appreciated for many reasons, not the least of which is the Thanksgiving Holiday. It’s also National Manatee Awareness Month, which is timely as tourists begin flocking to South Florida. It’s also National Entrepreneurship Month, honoring the hundreds of thousands of courageous individuals who have started their own businesses.
Of greater importance to those of us concerned with cybersecurity, November is also National Critical Infrastructure Security and Resilience Month. Yes, it’s quite a mouthful—almost as filling as turkey and stuffing (though not nearly as tasty).
Coming on the heels of Cybersecurity Awareness Month each October, National Critical Infrastructure Security and Resilience Month reminds government and quasi-public entities as well as private sector organizations about the importance of protecting our nation’s critical infrastructure and their roles in providing that protection.
What is Critical Infrastructure?
The first formal federal definition of Critical Infrastructure dates to 1996 when President Bill Clinton signed Executive Order 13010 addressing the importance of protecting the vital assets that comprise our critical national infrastructure.
List of Critical Assets. The list of these assets has evolved over time, and currently includes the following sectors, in alphabetical order: chemicals, commercial facilities, communications, critical manufacturing, dams, defense industries, emergency services, energy, financial services, food and agriculture, government facilities, healthcare and public health, information technology, nuclear reactors (and materials and waste), transportation systems, and water supply and wastewater systems.
A Mix of Public and Private Engagement. The order notes that energy may include electrical power systems and gas and oil storage as well as their transport and distribution. And that emergency services encompass medical, police, fire, and rescue services. These two examples, along with many similar examples among the other sectors, illustrate the mix of public and private participation in and responsibility for our critical infrastructure.
In fact, as the Cybersecurity and Infrastructure Security Agency (CISA) has publicly stated, “Because the majority of our national critical infrastructure is owned and operated by private companies, both the government and private sector have a common incentive to reduce the risks of disruptions to critical infrastructure.”
Lifeline Sectors. Four of these 16 sectors have been assigned ‘lifeline’ status—reflecting the assessment that their ability to continue functioning is so vital that the loss or disruption of any one of them would have ripple effects on the security and resilience of critical infrastructure across many of the other sectors. These lifeline functions are communications, energy, transportation, and water.
Threats to Critical Infrastructure
 The current list is comprehensive, as you can see, encompassing not only public or government systems but numerous private systems as well. In addition to their physical manifestations (operating plants, buildings, land, vehicles, containers, and so on), another element they all have in common is data.
The current list is comprehensive, as you can see, encompassing not only public or government systems but numerous private systems as well. In addition to their physical manifestations (operating plants, buildings, land, vehicles, containers, and so on), another element they all have in common is data.
Virtually all of these systems generate, process, retrieve, transmit, and/or store data, much of it highly sensitive or of vital importance. As such, the threats to our critical infrastructure include both physical and cyber threats and, in our digital age, the two are intertwined and interdependent. Physical security remains a vital component of any security program.
As Executive Order 13010 confirms, “Threats to these critical infrastructures fall into two categories: physical threats to tangible property (‘physical threats’), and threats of electronic, radio-frequency, or computer-based attacks on the information or communications components that control critical infrastructures (‘cyber threats’).
The order continues: “Because many of these critical infrastructures are owned and operated by the private sector, it is essential that the government and private sector work together to develop a strategy for protecting them and assuring their continued operation.”
And with this 1996 order, the call went out across the land to join together to protect our critical national infrastructure. In the ensuing years, this call has been further strengthened, enhanced, clarified, and broadened through various avenues, including annual presidential proclamations.
Additional Actions: 1998 to 2020
Presidential Directive 63. After his 1996 order, in May 1998 President Clinton further solidified the national emphasis on critical infrastructure protection with Presidential Decision Directive 63 (PDD-63). In part, this guidance called for several specific, important actions, including:
- Frequently reevaluating the reliability and vulnerability of our critical infrastructures in order to adapt our existing protective measures and responses to reflect changes in the nature of threats and in the technologies designed to thwart those threats
- Encouraging the creation of increasingly effective methods of infrastructure protection, based on ongoing research and development
- Focusing on implementing preventive measures, in addition to the emphasis on managing crises, executing threats, and disasters
- Encouraging private sector owners and operators to provide the maximum security feasible for the critical infrastructures they control
Presidential Directive 7. An update to PDD-63 occurred in the lengthy wake of 9/11/2001. In December 2003, President George W. Bush issued Homeland Security Presidential Directive 7 (HSPD-7) for critical infrastructure entification, prioritization, and protection. Entification refers to the act of giving objective existence to something, as in substantiating it, causing it to take shape, or otherwise making it real.
Cybersecurity and Infrastructure Security Agency Created. Also in 2003, CISA was created with the objective of leading the nation’s efforts to understand, manage, and reduce risk to our critical cyber and physical infrastructure. CISA was also given a central role in mobilizing a collective defense against those risks, bringing together public and private interests for optimum effectiveness.
Department of Homeland Security Leadership. Ten years later, in February 2013, Presidential Policy Directive 21 was released. PPD-21 emphasized the leadership role of the U.S. Department of Homeland Security in critical infrastructure protection, and set three strategic imperatives:
- To refine and clarify functional relationships across the federal government in order to unify the national effort to strengthen critical infrastructure security and resilience
- To promote more efficient information exchange by establishing baseline data and systems requirements for the federal government
- To implement an integration and analysis function to inform planning and operational decisions regarding critical infrastructure
FEMA National Planning Frameworks. The following year, in July 2014, the Federal Emergency Management Agency (FEMA) released the last in a series of five national planning frameworks designed to help guide disaster prevention, protection, mitigation, response, and recovery from “the threats and hazards that pose the greatest risk” to our nation’s critical infrastructure. The frameworks are part of the National Preparedness System and outline the roles and responsibilities of all participants in protecting our critical infrastructure.
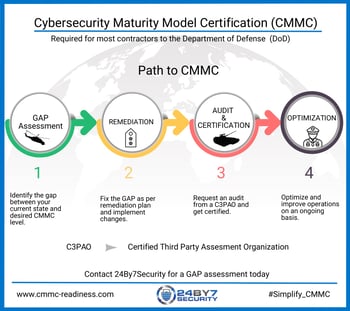 DoD Cybersecurity Maturity Model Certification. Another milestone event was launched in January 2020 by the U.S. Department of Defense (DoD). The defense supply chain consists of some 300,000 contractors and suppliers whose data protection and cybersecurity measures vary wildly based on the size, complexity, and nature of their product or service. Many of these contractors are responsible for critical infrastructure.
DoD Cybersecurity Maturity Model Certification. Another milestone event was launched in January 2020 by the U.S. Department of Defense (DoD). The defense supply chain consists of some 300,000 contractors and suppliers whose data protection and cybersecurity measures vary wildly based on the size, complexity, and nature of their product or service. Many of these contractors are responsible for critical infrastructure.
To address security weaknesses and better protect sensitive unclassified data across the supply chain, DoD introduced the Cybersecurity Maturity Model Certification (CMMC) to phase out the prevailing practice of allowing contractors to self-certify the security of their systems. Instead, the CMMC requires objective third-party cybersecurity certification against a clear set of established cybersecurity standards. The CMMC must be adopted by any contractor who desires to continue bidding on DoD work.
These are some of the most significant changes enacted since 1996 to protect critical infrastructure from both physical threats and cyber threats.
How Critical Infrastructure Affects You
Our critical infrastructure provides services that are vital to American society. Critical infrastructure includes the energy that powers our businesses, homes, and vehicles. The water we drink. The farms that grow and raise our food. The transportation and distribution systems that move people, food, goods, livestock, chemicals. The Internet and communication systems we depend on every day to conduct business and stay in touch. The hospitals and first responders in our communities. And more.
The business community plays an important role in supporting the security and resilience of many facets of our critical infrastructure. Businesses have a clear responsibility to effectively secure sensitive data, vital systems, and integral connections within their control.
According to CISA, “Strengthening public-private partnerships focused on critical infrastructure protection is both a national security and business imperative.”
What You Can Do
National Critical Infrastructure Security and Resilience Month is the perfect time to assess the security of your data, systems, and networks. You cannot know what components you are missing until you inventory and evaluate the components you already have.
Make sure you have completed these minimum activities as part of your security program:
- A recent security risk assessment, either a baseline (first-time) or annual reassessment
- Prioritization of the risks and vulnerabilities identified
- Remediation of high-priority risks and vulnerabilities without delay
- Investment in new technologies to enhance security
- Installation of software and app updates as vendors release them
- Enforcement of strong passwords among all employees
- Recent employee training in cybersecurity awareness, including phishing and other social engineering techniques
- Creation and enforcement of policies related to cybersecurity and physical security
There are numerous other best practices and proven cybersecurity measures that can be put in place to safeguard the data, systems, networks, and vital connections used in your business. Implementing the cybersecurity framework recommended by the National Institute of Standards and Technology (NIST) is a popular choice for many organizations, with a wealth of materials freely available on the NIST website.
Individual Americans can do their part at home, at work, and in their local communities by being prepared for all hazards, by reporting suspicious activities (“If you see something, say something”), and by learning more about critical infrastructure security and cybersecurity in general.
Summary
Since 1996, the U.S. has become increasingly focused on protecting our critical infrastructure and ensuring its resilience. Private companies are responsible for most of this infrastructure, which is why government entities and private companies must work closely together to ensure effective security for the near and long term.
Everyone has a role in protecting our critical infrastructure. Businesses have a clear roadmap to follow in implementing and maintaining effective cybersecurity, beginning with a security risk assessment. CISA, NIST, and other sources offer excellent materials and guidance to get you started. There’s no excuse for poor security.









