As of April 1, 2024, PCI Data Security Standard 4.0 rules the payment card industry. PCI DSS 3.2.1 is officially retired. Here’s what you should know.
Compliance Calendar for Implementing PCI DSS 4.0
The new PCI DSS requirements of version 4.0 were released two years ago on March 31, 2022. PCI DSS 4.0 imposes 64 new requirements that must be implemented by payment card industry members not later than March 31, 2025.
PCI DSS 4.0 is now the only authorized version of the industry-wide data security standard, with the previous standard, PCI DSS 3.2.1, officially retired as of March 31, 2024.
Merchants, third-party service providers, and card payment processors have been working since 2022 to adopt the new requirements of v4.0, which need to be implemented prior to the first annual v4.0 security assessment. Just 12 months remain for industry members to comply with v4.0 by adopting the new requirements and conducting their first v4.0 assessments.
Update to v4.0 Inspired by Four Objectives
PCI DSS v4.0 At A Glance spotlights some of the key changes from v3.2.1 to v4.0 along with the reasons for them.
One objective of v4.0 is to continue to meet the security needs of the payment industry, because “security practices must evolve as threats change.” Examples provided in the document include:
- Expanded multi-factor authentication requirements.
- Updated password requirements.
- New e-commerce and phishing requirements to address ongoing threats.
A second goal of PCI DSS 4.0 is to promote security as a continuous process, because “cybercriminals never sleep and therefore ongoing security is crucial to protect payment data.” Examples offered include:
- Clearly assigned roles and responsibilities for each requirement.
- Additional supplemental guidance to help industry members better understand how to implement and maintain security.
A third objective is to increase flexibility for organizations who employ different methods to achieve security objectives because greater flexibility allows more options to achieve a requirement’s objective and also supports payment technology innovation. Examples include:
- Allowance of group, shared, and generic accounts.
- Targeted risk analyses that allow members to establish frequencies for performing certain activities.
- A new method to implement and validate PCI DSS requirements called the Customized Approach, which provides another option for organizations that employ innovative methods to achieve security objectives.
A fourth goal noted in the document is to enhance validation methods, procedures, and reporting to increase transparency and granularity. One example offered is the improved alignment between information reported in the Report on Compliance (ROC) or Self-Assessment Questionnaire (SOC) and information summarized in the Attestation of Compliance (AOC).
These four objectives were instrumental in driving the latest version of the PCI Data Security Standard. Industry member feedback also played a vital role. Increases in payment card industry transaction volumes and values, and the risks they pose, also influenced the DSS update.
Transaction Volumes and Values at Record Highs
The use of credit, debit, and other payment cards, and the value of payment card transactions, continue to set records each year as consumers worldwide use their cards to acquire goods and pay for services. Globally, payment card transactions reached a record $625 billion (USD) in 2022, according to Statista.
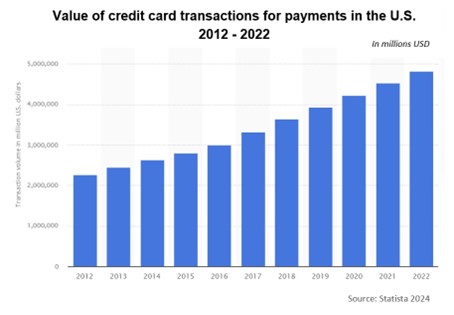 In the U.S. alone, the value of credit card transactions exclusively set another annual record at just under $5 million, according to Statista. This figure does not include debit cards and other payment cards.
In the U.S. alone, the value of credit card transactions exclusively set another annual record at just under $5 million, according to Statista. This figure does not include debit cards and other payment cards.
With these unprecedented transaction volumes and values, personally identifiable information and payment card data is being electronically transmitted in staggering numbers. Data breaches resulting from inadequate cybersecurity have generated unfavorable press for many businesses in the hospitality industry.
The increased risk resulting from skyrocketing card use led the payment card industry to revamp its Data Security Standard with dozens of new, more stringent security requirements and to impose a firm three-year implementation period.
Basic Compliance Steps for PCI DSS 4.0
Implementing PCI DSS 4.0 requires four activities that are essential to improving the security of payment account data and better protecting your customers.
- Annual Security Risk Assessment. This activity involves identifying the locations of all payment account data within your organization—and taking an inventory of all information technology assets and business processes associated with payment processing. It includes analyzing those processes and assets for vulnerabilities that could expose payment account data to hacking and other unauthorized access, and then implementing or updating all necessary controls. These actions culminate in the completion of a formal PCI DSS 4.0 risk assessment, required annually.
- Remediation of Vulnerabilities. This step includes identifying and addressing any gaps in your security controls, fixing all vulnerabilities that were identified during the assessment step above, and implementing secure business processes. It also requires that you securely remove any payment data that is being stored unnecessarily or beyond its use. With 64 new security requirements in v4.0, most organizations will discover additional vulnerabilities than in previous assessments.
- Reporting Assessment Findings. This activity requires documenting your assessment and remediation details and submitting a formal Report on Compliance (ROC) to the compliance-accepting entity, which is typically your acquiring bank or payment card brand. Smaller organizations who meet the criteria can report findings in a Self-Assessment Questionnaire (SOC). For most merchants, submission of an Attestation of Compliance (AOC) is also required.
- Monitoring and Maintenance. This is an ongoing activity that includes (1) the constant monitoring of security controls and safeguards that have been put in place to secure payment account data in your organization, and (2) maintaining those controls on an active and current basis, in compliance with PCI DSS 4.0.
These steps must be repeated annually by merchants and other payment card industry members. Level 1 and 2 merchants, who process more than one million transactions annually, must engage a Qualified Security Assessor (QSA) to conduct their annual assessments and produce the requisite Reports on Compliance. Level 3 merchants are generally eligible to conduct self-assessments using a formal Self-Assessment Questionnaire. Required Attestations of Compliance testify to the results of assessments.
All merchants are required to submit quarterly vulnerability scans to further demonstrate their compliance. Regular internal and external scans are highly beneficial in maintaining a secure perimeter and effectively safeguarding cardholder data. Anything less than full compliance is simply not worth the risk.
Assistance in Implementing PCI DSS 4.0
The new requirements of PCI DSS 4.0 must be incorporated into all new assessments and related documentation to meet the March 31, 2025 deadline. In its extensive document library, the PCI Security Standards Council offers templates for the new reports on compliance, self-assessment questionnaires, and attestations of compliance. In addition, the nearly 500-page PCI DSS 4.0 document reflects all the new requirements and is an excellent reference for implementation.
Qualified Security Assessors, including 24By7Security Inc., have been trained in the v4.0 update and are available to assist with assessments at any time. Be sure to contact a Qualified Security Assessor soon to schedule your assessment, as QSAs book up quickly. Organizations eligible for self-assessment should engage a professional cybersecurity and compliance firm, such as 24By7Security, to schedule assistance in navigating the v4.0 changes.
Either way, merchants, processors, and third-party service providers should be taking specific actions now, in accordance with the compliance calendar, to prepare for a thorough assessment against the new requirements. Because of its scale, this is not an undertaking you want to postpone any longer. No fooling.
Summary
The release of PCI DSS 4.0 in March 2022 introduced significant and extensive updates to the Data Security Standard, as well as the forms and reports required to assess and validate compliance. It replaces the previous v3.2.1, which was retired on March 31, 2024.
Going forward, payment card industry members need to embrace v4.0 requirements prior to their next annual assessments. Compliance will help reduce vulnerabilities and avoid costly data breaches, and is mandatory in the payment card industry. Organization leaders and security executives owe it to customers, shareholders, investors, and employees to implement the more rigorous security requirements of PCI DSS 4.0 by March 31, 2025, if not sooner.




.png?width=624&height=327&name=PCI%20%204-18-24%20webinar%20%20(1).png)

.png)


