Do you ever wish there was a single set of security and privacy rules that incorporated ISO, NIST, PCI, GDPR, HIPAA, and all the other requirements for protecting the data we’re responsible for?
Well, you know what they say about wishes. There is good news, though. HITRUST has gathered all of those rules and regulations and mapped them into a single, over-arching framework designed for ease of use, implementation, and certification.
That got your attention, didn’t it?
A Quick Overview
HITRUST was founded in 2007 to promote programs that help organizations safeguard sensitive information and manage their information risk and compliance from start to finish. Their HITRUST CSF framework is an industry-agnostic solution that has been adopted by organizations around the world who seek to improve trust among stakeholders and reduce the likelihood of data breaches.
The HITRUST CSF is an excellent option for any organization interested in implementing a comprehensive program to protect their sensitive information, whether personally identifiable information (PII), protected health information (PHI), payment card data, or other sensitive information.
The Unique Elegance of HITRUST CSF
The all-in-one HITRUST CSF is uniquely elegant for many reasons. It is flexible, scalable, and tailorable to accommodate differing organizational sizes, types, needs, systems, and compliance risk factors. Because it logically combines and maps security and privacy regulations into a single framework, it has become a popular, globally accepted solution.
The CSF is also uniquely elegant in:
- Eliminating the need for multiple assessments and reports;
- Scaling and customizing to adapt to an organization’s evolving needs; and
- Encompassing regulations, standards, and controls from authoritative international, federal, and state sources.
For these and other reasons, eight out of 10 top cloud service providers have adopted the HITRUST CSF and 75% of Fortune 20 companies use it. In addition, hundreds of thousands of HITRUST Assessments have been performed since the CSF was first introduced. Version 9.6.0, released in December 2021, is the current version of the HITRUST CSF.
Benefits of Adopting the HITRUST CSF
 There are many benefits organizations can enjoy by adopting the HITRUST CSF. Among the results of adoption are:
There are many benefits organizations can enjoy by adopting the HITRUST CSF. Among the results of adoption are:
- Increased trust and transparency among business partners and customers;
- Streamlined compliance interactions both within and outside the organization;
- Availability of a single benchmark to facilitate internal and external measurements against applicable security and privacy requirements; and
- Improved ability to manage the cost of compliance as well as the number, complexity, and degree of variation in security audits and assessments.
In addition, HITRUST offers a number of resources on its website. Two in particular are key partners of the HITRUST CSF—specifically the HITRUST CSF Assurance Program and MyCSF. Watch for information about these resources in our future blogs.
Two Options for Certification
Organizations who adopt the HITRUST CSF have a choice of two certifications, as described below.
HITRUST i1 Certified is the designation an organization receives after completing a HITRUST Implemented 1-year validated assessment with a passing score. The i1 is unique in addressing deficiencies found in other frameworks, using attributes not available through other assurance programs.
HITRUST r2 Certified is the designation granted to an organization upon completion of a HITRUST Risk-based 2-year validated assessment with a passing score. The r2 is considered the gold standard for information protection assurances due to the comprehensiveness of its control requirements, the depth of quality review, and the consistency of oversight.
Foundation and Structure of the HITRUST CSF
The HITRUST CSF is an all-in-one framework whose core is based on ISO/IEC 27001:2005 and 27002:2005, published by the International Organization for Standardization (ISO) and International Electrotechnical Commission (IEC). In total, the CSF includes 156 security and privacy control specifications, with associated implementation requirements.
The CSF incorporates the 11 clauses or categories of ISO 27001:2005, but also adds a 12th control category to address implementation of an Information Security Management Program—similar to the Information Security Management System of ISO 27001:2005—as well as a 13th category to address risk management. Finally, it includes a 14th control category for specific privacy practices, such as GDPR, that are not addressed in the other 13 categories.
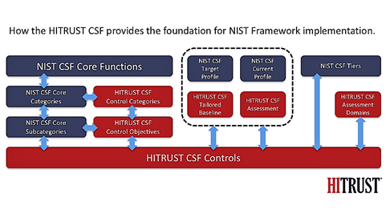 With this foundation, the HITRUST CSF incorporates more than 40 additional security and privacy regulations, standards, and frameworks in order to provide comprehensive and prescriptive coverage. These include the National Institute of Standards (NIST) Cybersecurity Framework (CSF), the Payment Card Industry (PCI) Data Security Standard (DSS), the Health Insurance Portability and Accountability Act (HIPAA) including the HIPAA Security Rule and HIPAA Privacy Rule, the General Data Protection Regulation (GDPR), and other prominent global, national, and state standards.
With this foundation, the HITRUST CSF incorporates more than 40 additional security and privacy regulations, standards, and frameworks in order to provide comprehensive and prescriptive coverage. These include the National Institute of Standards (NIST) Cybersecurity Framework (CSF), the Payment Card Industry (PCI) Data Security Standard (DSS), the Health Insurance Portability and Accountability Act (HIPAA) including the HIPAA Security Rule and HIPAA Privacy Rule, the General Data Protection Regulation (GDPR), and other prominent global, national, and state standards.
These compliance requirements are mapped to the HITRUST CSF, making it easy for organizations to adopt according to their needs. They are also able to (1) track their progress in complying with the requirements of their specific industry, and (2) provide certifiable risk assurances to their internal and external stakeholders, including regulators. The HITRUST strategy enables adopters to ‘Assess Once, Report Many.’
Latest Version: v9.6.0
As an indication of how HITRUST is committed to maintaining an up-to-date CSF, the latest version (v9.6.0) delivered these enhancements when released in December 2021:
- Created refreshed mapping for NIST SP 800-53 Revision 4;
- Added NIST SP 800-53 Revision 4 as a selectable compliance factor; and
- Modified certain requirement statements and illustrative procedures to support the new HITRUST Implemented 1-year (“i1”) Validated Assessment.
Fully Customizable for Your Organization
Because the HITRUST CSF is both risk-based and compliance-based, organizations of varying risk profiles can customize the security and privacy control baselines using an array of factors. These include an organization’s type, size, systems, regulatory requirements, and compliance requirements.
THE HITRUST CSF compliance-based approach allows organizations to incorporate additional regulatory or compliance components to meet their specific needs and industry requirements.
The HITRUST CSF risk-based approach offers three levels of implementation requirements based on organizational and system risk factors.
Level 1 provides the minimum baseline control requirements. Each subsequent level includes the previous level plus additional requirements, reflecting increased levels of risk. This approach is similar to the CMMC 2.0 framework for Department of Defense contractors, in which three levels of cybersecurity maturity are based on the sensitivity of information handled by an individual contractor.
Added Value: Assessment and Readiness Services
In order to become certified against the HITRUST CSF, organizations are required to utilize the services of a HITRUST Authorized External Assessor or HITRUST Authorized Readiness Licensee to conduct a third-party review as part of the process of a validated assessment.
HITRUST Authorized External Assessors. These organizations are approved by HITRUST to perform assessment engagements for clients seeking HITRUST Validation or Certification reports. HITRUST Authorized External Assessors may also assist clients with adoption of the CSF, implementation, and remediation efforts following adoption.
HITRUST Authorized Readiness Licensees. These organizations are approved by HITRUST to perform consulting and readiness work for clients looking to adopt the CSF or prepare for their first HITRUST Assessment. HITRUST Authorized Readiness Licensees may also assist clients with adoption of the CSF, implementation, remediation efforts following adoption, and facilitated self-assessments.
The Importance of Readiness
 As a HITRUST Authorized Readiness Licensee, 24By7Security is able to perform consulting and readiness work for any organization who wishes to adopt the HITRUST CSF or prepare for their first HITRUST Assessment. Making sure that your security program is in great shape before calling in the External Assessor can save valuable time and resources.
As a HITRUST Authorized Readiness Licensee, 24By7Security is able to perform consulting and readiness work for any organization who wishes to adopt the HITRUST CSF or prepare for their first HITRUST Assessment. Making sure that your security program is in great shape before calling in the External Assessor can save valuable time and resources.
To prepare your organization for the final steps, 24By7Security provides HITRUST Readiness Services that include, but are not limited to:
- Assistance in completing the self-assessment questionnaire, enabling you to determine which level of requirements apply to your organization, and the controls and requirements to be implemented.
- Assistance in implementing the CSF framework that applies to your unique organization, identifying compliance gaps, and remediating those gaps until all requirements are met.
- Preparation of policies, procedures, reports, and other documentation required by the CSF.
- Assistance in preparing for audit by an authorized HITRUST Assessor to determine whether you are certified compliant with the applicable HITRUST CSF framework.
Employing our HITRUST Readiness Services can help any organization avoid costly missteps and achieve your objective in a timely and efficient manner.
Summary
Security and privacy are crucial to everyone who conducts business online. Organizations the world over are governed by a multitude of regulations and standards designed to protect the sensitive information that we create, share, transfer, store, upload, and download each day.
Short of having one universal set of security and privacy rules to follow, HITRUST created the next best thing by mapping all of those regulations into a single, over-arching framework for information security and privacy. It’s no surprise that the HITRUST CSF has become a popular, globally adopted solution that has helped thousands of organizations manage their compliance and risk levels much more efficiently.
Is the HITRUST CSF right for your organization? Contact us for a complimentary consultation and let’s find out!