- cyber attacks
- cyber security
- #CyberAware
- Cybersecurity
- hackers
- ransomware
- phishing
- other
- COVID19 scams
- types of phishing
- cyber security
- Cybersecurity
- network segmentation
- ransomware
- segment your network
- other
- network security
- Cybersecurity
- passwords
- #strong passwords
- DontRiskItSecureIt
- other
- #CyberAware
- Cybersecurity
- #cybersecurity awareness training
- #strong passwords
- DontRiskItSecureIt
- anti-virus
- other
- cyberattacks
- VPN
- #CyberAware
- Cybersecurity
- #Education Law
- #FERPA
- #university
- DontRiskItSecureIt
- other
- online safety
- COVID19
- Coronavirus
- COVID19 scams
- student personal information
- online learning security
- coronavirus cybersecurity
- Cybersecurity
- Healthcare IT
- hackers
- ransomware
- other
- data breaches
- COVID19 scams
- Cybersecurity
- dontrisksecureit
- information technology
- other
- online safety
- cyberattacks
- cloud security
- CASB
- Cybersecurity
- healthcare
- Healthcare IT
- HHS
- HIPAA
- telehealth
- telemedicine
- DontRiskItSecureIt
- COVID19
- online security
- video chat
- telenetworking
- Cybersecurity
- dontrisksecureit
- malware
- information technology
- other
- online safety
- cyberattacks
- data breaches
- COVID19 scams
- Cybersecurity
- DontRiskItSecureIt
- COVID19
- remote workforce
- WFH
- cybersecurity remote workforce
- VPN
- 24By7Security
- Aarohi Talati
- Akash Deo
- Akhil Deo
- Amanda Spence
- Andrea Richard
- Anirudh Nadkarni
- Arjun Talati
- Benjamin Stukes
- Brian Gomez
- David Jost
- Deepali Shah
- Gabrielle Grau
- Gail Blount
- Juan Carlos Hernandez
- Kelly Alvarez
- Martin Palencia
- Michael Brown
- Nitin Chowdhry
- Parita Patel
- Prakul Neupane
- Randy Rodriguez
- Rema Deo
- Rupal Talati, HCISPP
- Sanjay Deo
- Yashica Nagpal
July, 21 2020
Most of the data breaches we hear about on the news are executed to extract money or personal information from its[…]
July, 14 2020
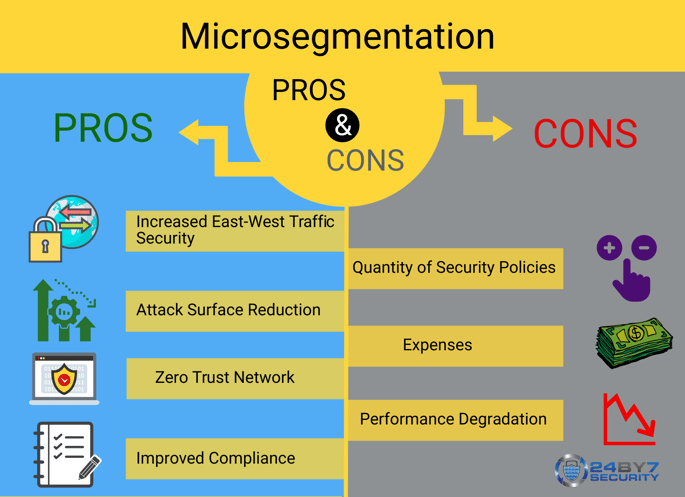
What is Microsegmentation? Microsegmentation is a method of heightening network security by logically splitting up[…]
July, 7 2020
Passwords are the first defense to protecting private information. It is important to implement strong passwords to[…]
June, 24 2020
According to McAfee, total mobile malware detections increased by about 48% from the beginning of 2018 to the end of[…]
June, 16 2020
With the cases of coronavirus on the rise, there has been a shift to virtual learning which may last longer than[…]
May, 18 2020
Ransomware attacks are on the rise this year, crippling cities and organizations that unfortunately fall victim to[…]
May, 5 2020
[Editor's Note: This post is part of our blog series, Foresight 2020: Top 11 Cybersecurity Actions Every Company Should[…]
April, 24 2020
Telemedicine has been around for years, but as a healthcare service it has been underutilized. Today, virtual visits[…]
April, 13 2020
Since the COVID-19 outbreak, hackers have been exploiting the public's worst fears and the need to seek relevant[…]
April, 6 2020
Let’s face it – telecommuting is on the rise. Yes, COVID-19 has changed the short-term decisions that businesses make[…]