- #CyberAware
- ransomware
- phishing
- other
- Cybersecurity Month
- cybercrime
- #backups
- cyber attacks
- Cybersecurity
- offline backup
- ransomware
- DontRiskItSecureIt
- other
- cyber attacks
- cyber security
- #CyberAware
- Cybersecurity
- hackers
- ransomware
- phishing
- other
- COVID19 scams
- types of phishing
- cyber security
- Cybersecurity
- network segmentation
- ransomware
- segment your network
- other
- network security
- Cybersecurity
- Healthcare IT
- hackers
- ransomware
- other
- data breaches
- COVID19 scams
- #CyberAware
- Cybersecurity
- #cybersecurity awareness training
- incident response
- hacker
- ransomware
- Security
- DontRiskItSecureIt
- other
- cyber range
- practical training
- Cybersecurity
- healthcare
- ransomware
- Security
- security assessment
- DontRiskItSecureIt
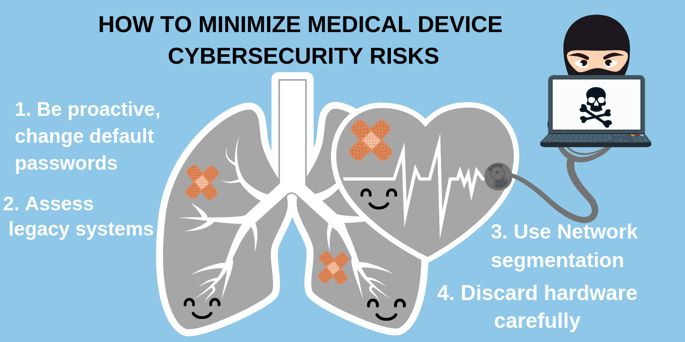
- medical devices
- cyberattacks
- cyber attacks
- cyber extortion
- #CyberAware
- Cybersecurity
- #cybersecurity awareness training
- ransomware
- Security
- phishing
- other
- ransomware
- #strong passwords
- DontRiskItSecureIt
- other
- online safety
- Chief information security officer
- CISO
- cyber security
- #CyberAware
- information security
- ransomware
- risk mitigation
- Security
- security controls
- security risk assessment
- security strategy
- vCISO
- virtual ciso
- wannacry
- DontRiskItSecureIt
- Risk Analysis
- malware
- phishing
- social engineering
- information technology
- firewall
- other
- 24By7Security
- Aarohi Talati
- Akash Deo
- Akhil Deo
- Amanda Spence
- Andrea Richard
- Anirudh Nadkarni
- Arjun Talati
- Benjamin Stukes
- Brian Gomez
- David Jost
- Deepali Shah
- Gabrielle Grau
- Gail Blount
- Juan Carlos Hernandez
- Kelly Alvarez
- Martin Palencia
- Michael Brown
- Nitin Chowdhry
- Parita Patel
- Prakul Neupane
- Randy Rodriguez
- Rema Deo
- Rupal Talati, HCISPP
- Sanjay Deo
- Yashica Nagpal
October, 6 2020
Imagine. You are on your phone or computer, and you begin scrolling through your emails. You do this every day to see[…]
August, 11 2020
With the amount of ransomware going around in the state, it would be crazy not to consider some type of backup. Whether[…]
July, 21 2020
Most of the data breaches we hear about on the news are executed to extract money or personal information from its[…]
July, 14 2020
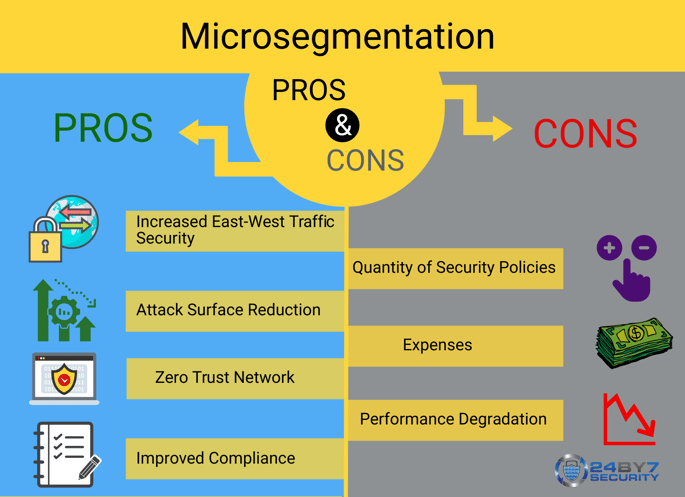
What is Microsegmentation? Microsegmentation is a method of heightening network security by logically splitting up[…]
May, 18 2020
Ransomware attacks are on the rise this year, crippling cities and organizations that unfortunately fall victim to[…]
October, 8 2019
Imagine a team of IT security professionals connecting to a simulated security environment, when suddenly one of them[…]
July, 31 2019
Medical devices, just like any other Internet of Things (IoT) object, are prone to hackers. These hacks can get[…]
March, 18 2019
Phishing scams have long been an effective social engineering technique used by criminals to adversely affect[…]
November, 26 2018
Following #NationalCyberSecurityAwareness Month, we celebrate #ComputerSecurityDay. Help spread the word on social[…]
September, 18 2018
Can your business benefit from a part-time CISO? Table of Contents: A real story of risks found on a site and how this[…]